Quarterly insights: Cybersecurity
Proliferating APIs expand attack surface for adversaries
Application programming interfaces (APIs) are a critical building block of modern software whose use has surged in recent years, making the importance of APIs for web traffic today hard to overstate. As a result, APIs have become key targets for attackers.
Traditionally, entities have primarily used web application firewalls (WAFs) and API gateways to secure APIs from attackers. But while WAFs and gateways play crucial roles in security architectures, they have limits.
These limits have highlighted the need for new approaches to safeguard against advanced emerging threats and have led to a new generation of API security platforms. Generally, these solutions belong to one of three specialized areas: API security posture, API runtime security and API security testing and secure development. We provide an overview of each of these three areas.
The API security market contains numerous competitors. We briefly profile 10 companies offering these newer API security approaches, usually as part of a broader security or enterprise software platform. We also provide more detailed profiles of six pure-play companies providing API security in the new areas.
TABLE OF CONTENTS
- APIs are a critical building block of modern software
- APIs’ prevalence and centrality make them key targets for attackers
- Web application firewalls and gateways are the traditional API security solution
- Elevating API security in the modern landscape
- API security posture platforms
- API runtime security platforms
- API security testing and secure development platforms
- API security providers
- Keeping the connectors safe
- Sector market activity: Cybersecurity index performance, M&A activity highlighting Splunk, Imperva and Contxt, and private placement activity highlighting OneTrust and Stamus Networks
Includes discussion of 42Crunch, Akamai (AKAM), Amazon Web Services (AMZN), Barracuda Networks, Cequence, Cloudflare (NET), F5 (FFIV), Fastly (FSLY), Fortinet (FTNT), Imperva, Microsoft (MSFT), Noname Security, Radware (RDWR), Salt Security, ThreatX, Traceable and Wallarm.
APIs are a critical building block of modern software
An application programming interface is a set of defined rules that enable software applications to communicate with each other. APIs process data transfers between systems: Software users request data in one application, which sends the request to an API. The API, in turn, retrieves requested data from another source and returns it to the user. There are many types of APIs, and they are used in many ways across many different data structures.
Web service APIs are common APIs most people use (indirectly) every day. Web service APIs accept hypertext transfer protocol (HTTP) requests, which dictate how information on the web travels. Web service APIs expose the uniform resource identifiers (URIs) that provide access to specific resources in databases. These requests could contain data formatted in XML (extensible markup language, used to store and transfer data in a relatively user-friendly format) or JSON (JavaScript object notation, another easily understandable format often used to send data from a server to a web page). A server might respond with HTML (hypertext markup language, which structures how web content should behave), XML, or JSON data, which web browsers and other applications can process. Other data formats used with web service APIs include SOAP (simple object access protocol, a type of XML protocol used for exchanging structured data), and REST (representational state transfer, an architectural style that defines a set of constraints for creating web services). REST can be used for its own API, also known as a RESTful API.
Other types of APIs include open APIs, which are public APIs accessible to everyone; partner APIs, which can only be accessed by designated developers; internal APIs, also known as private APIs, which are only exposed by internal systems of an organization; and composite APIs, which combine different data and service APIs that perform sequences of tasks.
APIs are a critical building block of modern software, facilitating seamless interaction and data sharing among diverse applications. They enable interoperability, scalability, and agility among different systems, services, and components to support major computing trends such as cloud migration, microservices architecture, and event-driven applications. As a result, API use has surged in recent years, and the importance of APIs for web traffic today is hard to overstate. Tony Lauro, director of security technology and strategy at leading content delivery network company Akamai, estimates API calls currently represent 83% of all web traffic.
APIs’ prevalence and centrality make them key targets for attackers
As a result of their increased use, APIs have become key targets for attackers. Bad actors try to exploit vulnerabilities in APIs to gain unauthorized access to data and systems. There are many types of attacks targeting APIs, including the following:
- Denial of service (DoS) attacks: DoS attacks aim to make APIs unavailable by overwhelming them with traffic.
- Data injection attacks: These attacks inject malicious data into APIs to manipulate their behavior.
- Broken authentication or broken access control attacks: Attackers take advantage of incorrectly implemented APIs to impersonate users and perform actions that enable them to gain access to internal systems, view sensitive data, and disrupt system processes and organizational operations.
- Cross-site scripting (XSS) attacks: XSS attacks inject malicious scripts, usually JavaScript, into content that is then served to users. Since JavaScript can access cookies, attackers might steal users’ cookies to impersonate them online.
- Bot attacks: Bad actors automate processes and tactics to identify and exploit vulnerabilities while remaining undetected.
While API use and its associated security risks have been increasing for many years, focus on the problem increased significantly in 2019 when OWASP (the Open Web Application Security Project, a standard awareness document that represents the most critical security risks to web applications) started including API security in its list of the top 10 security risks.
The concern is not simply theoretical. In addition to thousands of incidents that go unreported, there have been many high-profile incidents. Here are some examples:
In September 2022, Optus, an international telecom company, reported a breach of 10 million customer records because of an unprotected and publicly exposed API that did not require authentication before facilitating a connection.
In July 2022, Twitter (now X), reported an API breach that occurred from late 2021 into 2022 and exposed personally identifiable information of 5.4 million user accounts. The attacker gained access through an API vulnerability that allowed users to find other users and mistakenly revealed personal information. This is a clear example of a broken object level authorization (BOLA) exploit, where attackers can slowly pull information and data from organizations without the organization knowing for some time.
In August 2021, T-Mobile suffered a massive data breach affecting millions of customers due to a misconfigured API, which exposed sensitive data like social security numbers and driver’s license numbers, ultimately leading to the data being sold on the dark web.
Web application firewalls and gateways are the traditional API security solution
Traditionally, entities have primarily used web application firewalls (WAFs) and API gateways together to filter out malicious traffic, enforce access controls, and direct requests for APIs. WAFs, as security tools, are adept at filtering, monitoring, and blocking HTTP traffic to and from web applications, including APIs. They detect attacks based on signatures and user-based session behavior checks, fortifying API security by guarding against vulnerabilities and ensuring compliance with industry standards such as the payment card industry data security standard (PCI DSS). Some advanced WAFs also use machine learning to reduce false positives and deliver more accurate detection. The inception of WAFs can be traced to the late 1990s and early 2000s, when proliferating web application attacks necessitated a proactive defense mechanism. Notable pioneers include Imperva, F5, Breach Security (acquired by Trustwave), and Barracuda Networks (acquired by NetContinuum).
API gateways, serving as API front ends, are intermediaries between API providers and consumers. They enforce security policies and throttle traffic while also managing authentication and authorization processes. Their role extends to rate limiting, preventing API overloads, and providing valuable insights through monitoring and analytics. API gateways emerged in the mid-2000s, spurred by the escalating popularity of web services. Today, AWS, Apigee, Microsoft, and Tyk are among many companies offering API gateway products.
API requests are filtered through WAFs, then authenticated and routed to appropriate backend services via API gateways
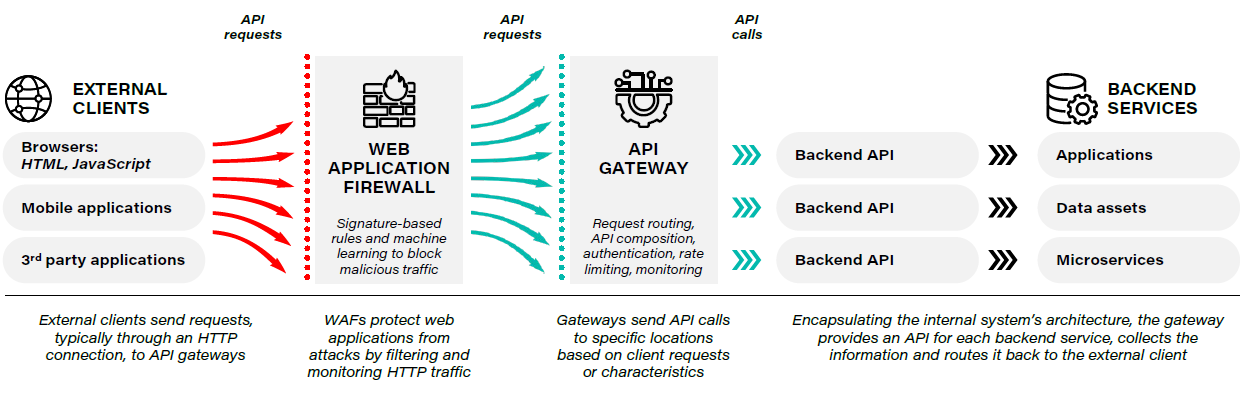
Source: First Analysis.
While WAFs and gateways play crucial roles in security architectures, they have several limitations:
- WAFs are limited to monitoring and filtering traffic that passes through them, leaving anything outside this traffic flow unobserved and unguarded.
- WAFs rely heavily on pre-set rules to detect known attack patterns, and this approach can cause problems, such as blocking legitimate traffic, allowing malicious activity to slip through, and triggering false positives.
- If a WAF has not been updated to detect a novel threat, attackers can use unknown or zero-day attacks to bypass it.
- Many companies ultimately use multiple API gateways, which each contain their own set of API rules and logs, making it difficult to manage rules and update for vulnerabilities as applications evolve.
- If an API gateway fails, it can affect all the APIs it manages and lead to system-wide outages.
- With a single API gateway, performing a task may require client software to send and receive data to and from several backend services, resulting in added latency.
Both network tools have nonetheless made improvements to better mitigate threats; however, they still struggle to combat complex attacks that exploit intricacies in API logic and behaviors, and they cannot cover 100% of the attack surface.
Elevating API security in the modern landscape
The limitations of traditional API security solutions highlighted the need for new approaches to safeguard against advanced emerging threats. As a result, a new generation of API security platforms has emerged. Generally, these solutions belong to one of three specialized areas: API security posture, API runtime security and API security testing and secure development. Each contributes to comprehensive API protection – from design and configuration to real-time operation to ongoing testing and validation. However, some platforms encompass all three areas in an effort to provide comprehensive support and defense.
API security posture platforms
Platforms in the first area, API security posture, help organizations identify and categorize all APIs within an environment. They create catalogs and directories of APIs, including details on endpoints, functions, data formats, and related metadata. This comprehensive mapping creates a governance framework, ensuring the entire API landscape remains under watch. Users can manage version control and change tracking to ensure updates do not disrupt existing applications. The software assesses API vulnerability by scanning and scrutinizing APIs for prevalent issues and ensuring compliance with industry standards and best practices, such as OWASP API Security Top 10. Users can conduct performance checks to identify bottlenecks and enhance overall system efficiency. These tools play a critical role in enhancing APIs’ overall security posture by identifying and mitigating potential vulnerabilities and misconfigurations. Noname, Cequence, ThreatX, Salt and Traceable are a few solutions helping manage security posture and discovery.
Cequence provides a view into organizations’ API infrastructures
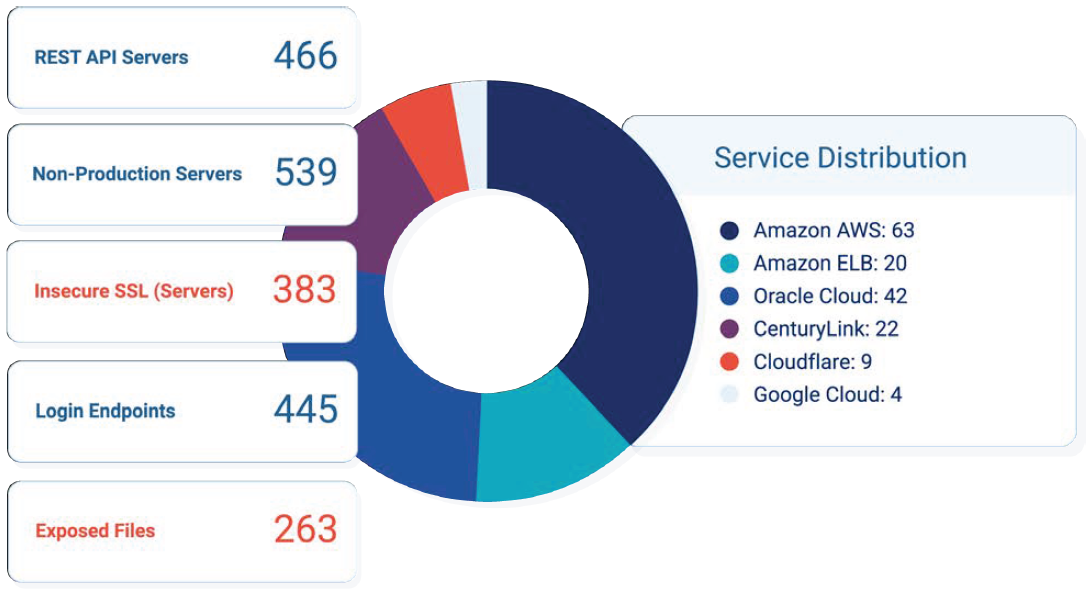
Source: Cequence Security.
API runtime security platforms
Platforms in the second area, API runtime security, focus on real-time monitoring and anomaly detection using tools such as machine learning, artificial intelligence (AI), and behavioral analytics. They detect and prevent malicious activities targeting APIs during execution by establishing baselines of normal API activity. With these baselines, they can quickly identify anomalies that could signify attacks, and they can trigger timely alerts, notifications, and automated actions. Often they include workflow integrations to help with ticketing to automate remediation processes. The primary goal is to safeguard APIs against various threats, including SQL injection, cross-site scripting, denial-of-service attacks, and data breaches. Companies including Wallarm, Cequence, ThreatX, Salt and Traceable feature API runtime security as a major component of their platforms.
Noname Security’s runtime solution protects APIs after deployment
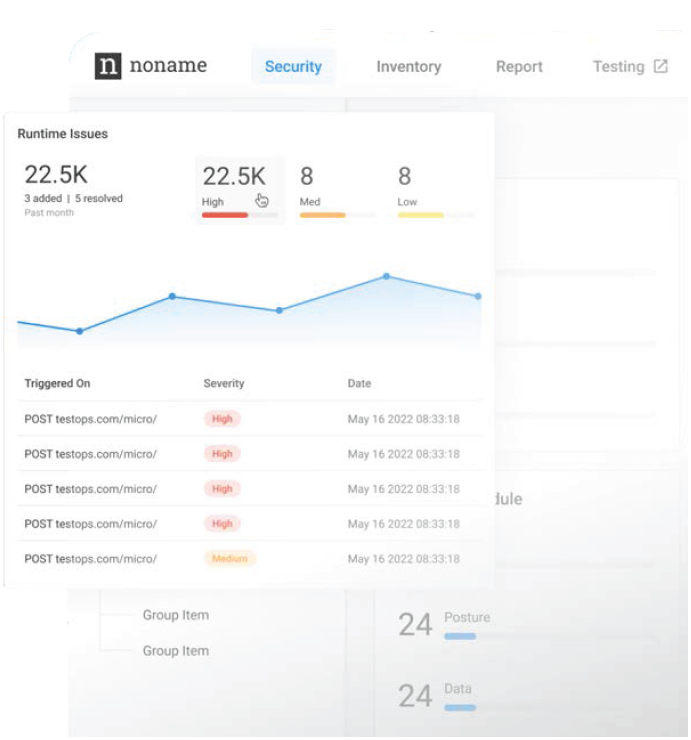
Source: Noname Security.
API security testing and secure development platforms
Platforms in the third area, API security testing and secure development, are tailored for developers and testing teams involved in API development. These platforms assess and verify API security throughout development life cycles. Companies in this space provide tools that help developers and testers interact dynamically with APIs to simulate attack scenarios and identify security vulnerabilities early in the development process. With the rise of continuous integration and delivery (CI/CD) in software development, frequent testing, feedback loops, and validation of APIs are critical. Tools in this category offer features such as automated testing, code analysis, vulnerability scanning, penetration testing, and compliance checks, ensuring APIs remain secure in the fast-paced and ever-evolving software development landscape. Noname, Cequence, Salt and Traceable provide API security testing solutions, while 42Crunch’s platform is primarily focused on developer-led API security.
42Crunch audits and tests APIs against security vulnerabilities in development
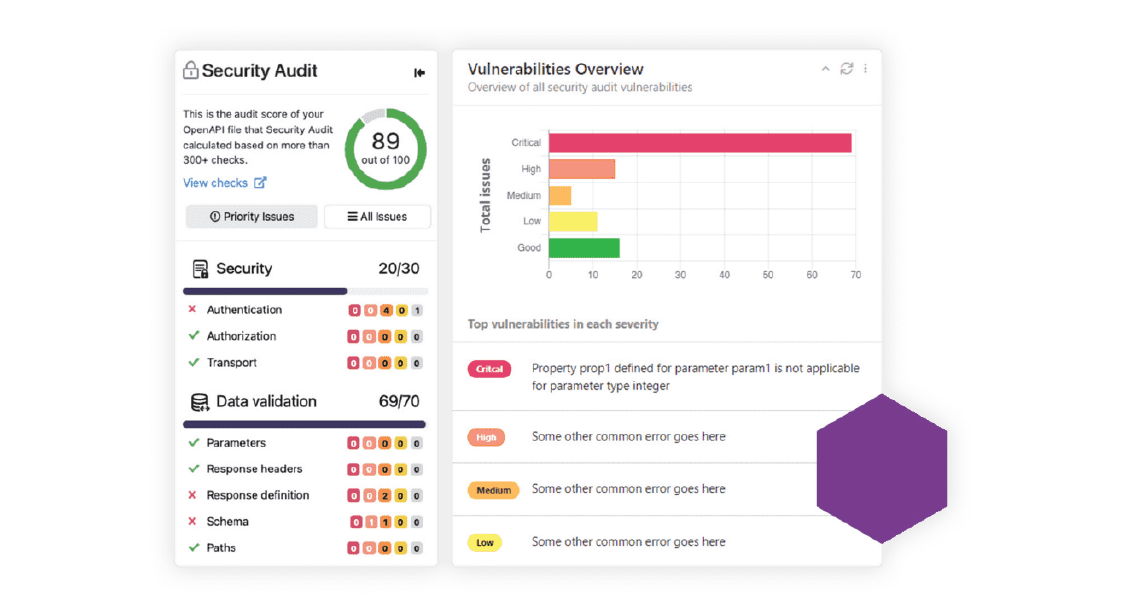
Source: 42Crunch.
API security providers
The API security market contains numerous competitors. Below, we highlight 42Crunch, Cequence, Noname Security, Salt Security, ThreatX, and Traceable – a few of the players in the modern pure-play API security market today. But first, we note several other significant companies providing API security solutions within broader offerings:
- Akamai (AKAM) – Akamai is a prominent content delivery network and cloud service provider specializing in content delivery, web security and cloud optimization with many API functions: discovery and inventory, detection with AI, automated response and ticketing, and proactive threat hunting with timeline investigations.
- AWS (AMZN) – Amazon Web Services’ vast cloud computing offerings include API security offerings such as API gateways (leader in the space) and a WAF (which sits on top of its application load balancer and content delivery network), DoS prevention and bot mitigation.
- Barracuda Networks – Barracuda offers a broad array of data protection solutions including email protection, network security, a managed extended detection and response tool, and application security encompassing a WAF, distributed denial-of-service (DDoS) and bot protection, and testing and production capabilities.
- Cloudflare (NET) – Cloudflare is a large cloud-services provider helping connect the cloud, provide network security at scale, and protect and accelerate applications. It offers API gateways, WAFs, bot management, and DDoS attack protection.
- Imperva – Imperva is a large application data security and compliance company that helps protect, monitor, audit and secure business applications and databases. It offers content delivery networks, WAFs, runtime protection, and bot and DDoS protection.
- F5 (FFIV) – F5 is a multicloud application security and delivery company offering a broad line of API security solutions including WAFs, DDoS protection, bot defense, and API discovery capabilities.
- Fastly (FSLY) – Fastly provides an edge cloud platform for processing, serving and securing its customers’ websites and applications. It includes bot protection, DDoS mitigation, and a WAF.
- Fortinet (FTNT) – Fortinet is a leading network security company whose broad lineup includes many application security solutions such as WAF, server load balancing, and security testing.
- Microsoft (MSFT) – Microsoft offers a range of software products, cloud services and cybersecurity solutions with API threat detection and WAF built on top of its content delivery network.
- Radware (RDWR) – Radware’s application delivery and protection, denial-of-service protection and bot management capabilities ensure security of applications, APIs, development platforms and infrastructure.
- Wallarm – Wallarm provides a comprehensive AI-powered API security platform focused on real-time web application and API security with security posture and discovery management, runtime protection, and testing for API development.
Founded in late 2016, 42Crunch is an API security company focusing on providing developers with tools to best code and architect their APIs. Headquartered in London, it also has offices in San Francisco, Denver, Dublin, London, Madrid and Montpellier, France. It raised $17 million in its latest Series A round from Energy Impact Partners and returning investor Adara Ventures. As an evangelist for the OWASP Top 10, 42Crunch focused its platform on bridging the gap between API development teams and API security teams.
The platform first discovers APIs via integration or traffic monitoring and then defines organizations’ APIs in an OpenAPI contract, a standardized way to describe and document API functionality, structure, and behavior in a machine-readable format. 42Crunch audits these contracts for quality and security vulnerabilities. Once audited, development teams can write their APIs using the contracts as frameworks. Then, they can test their APIs using 42Crunch’s security scoring and remediation advice. When clients deploy their APIs they use “allow lists” that constrain API traffic to conform to the OpenAPI contracts. 42Crunch connects regularly with the developer community through APISecurity.io, its biweekly newsletter. Its website features customers such as Bridgestone, Ford, Travelers Insurance and Verizon.
Another large, comprehensive pure-play API security company, Cequence was founded in 2013 in Sunnyvale, California. According to Capital IQ and independent research, the company has raised over $127 million across three rounds from Menlo Ventures, Icon Management, T Ventures, HarbourVest Partners, Shasta Ventures, Dell Capital, T-Mobile Ventures, HP Pathfinder, KPN Ventures and Prosperity7. With that capital, it has expanded quickly and added offices in Cincinnati, France, the United Kingdom, India and Germany.
Its comprehensive product suite features three modules. Spyder helps discover API attack surfaces and informs clients about what is going on at a technical level within organizations’ API footprints. Sentinel provides additional context around organizations’ risk postures before and after production to best remediate issues that could lead to data loss or business disruption. This includes testing APIs for critical vulnerabilities. Lastly, Spartan prevents real-time automated attacks from exploiting vulnerabilities. This functionality helps mitigate and stop attacker traffic without calling out to a WAF or gateway. Cequence positions itself for midsize and large customers who are concerned about APIs. It also offers its solution as a managed service for customers looking to reduce the burden on their internal teams; with this solution, internal teams can still write or adjust policies to fit their needs.
Palo Alto, California-based Noname Security has tremendous momentum in the modern pure-play API security market and provides comprehensive functions for all three API security areas. The company has expanded quickly since its founding in 2020 and has raised $220 million across three rounds from Lightspeed Ventures, Georgian, Insight Partners, Cyberstarts, ForgePoint Capital, Next47 and Syndicate Group. The post-money valuation of the latest raise in December 2021 was $1 billion. The company also has offices in Tel Aviv and London.
Noname monitors and analyzes network traffic at chokepoints, offering faster analysis compared to competitors who offload traffic to multitenant SaaS clouds. While this approach enhances speed and scalability, Noname envisions the future of API security as an original-equipment-manufacturer solution where its software is directly integrated into leading network infrastructure products. Its platform automatically discovers and builds inventories of APIs and domains and assesses them for misconfigurations and compliance risks while preventing attacks in real time using AI and machine-learning-based detection that integrates with existing tools for alerts and ticketing. The platform adds a security layer to its clients’ development processes to ensure APIs are implemented without vulnerabilities. The company positions itself for enterprise customers and supports over 20% of the Fortune 500. We believe Noname’s solution functions as advertised and, with its ample funding, has the resources to focus on the needs of large, complex customers.
Salt Security, another leading comprehensive API security platform, was founded in 2015 in Palo Alto, California, and also has an office in Tel Aviv. The company has raised over $271 million (which we believe is the most of any pure-play API security company) from Capital G, Sequoia, Y Combinator, Tenaya Capital, Advent International, Alkeon Capital, DFJ Growth, S Capital, Accel Partners and CrowdStrike (CRWD). The latest post-money valuation was $1.4 billion.
Salt uses agentless deployment to mirror API traffic synchronously through a feed. It aggregates API attributes in a data lake where machine learning and AI models provide insights into security postures in relation to relevant API vulnerabilities, and it pinpoints APIs that may be exposing sensitive data. In real time, the solution distinguishes mistakes from attacks and either automatically blocks them or allows for manual intervention. The platform uses knowledge gathered from API runtime activity to provide developers with recommendations for remediating vulnerabilities. AI helps explain found vulnerabilities and remedies in plain context for developers and integrates with workflow and ticketing applications for easy resolution. Salt supports large enterprise customers like Zoom, Aon and Payoneer.
Founded in Boston in 2014, ThreatX has raised over $60 million from Habert Growth, Vistara Growth, .406 Ventures, Access Ventures and Grotech Management, according to Capital IQ. The company provides its customers with a managed API and application protection platform that includes an around-the-clock protection-as-a-service team: a dedicated group of experts who constantly monitor, hunt and remediate threats. In addition to managing APIs on a day-to-day basis, the team can help configure security measures to fit specific client needs. The platform provides an attacker-centric view of API security. It discovers and analyzes all APIs within organizations, watches for attackers targeting APIs and tracks their behaviors over time so it can automatically stop malicious activity.
Unlike some solutions that rely on third-party WAFs for signature-based attacks, ThreatX is a cloud API-native solution, offering a single platform to cover traditional WAF threats, bot defenses, and DDoS protection through a combination of signature-based methods and behavioral analysis. Within the platform, ThreatX uses AI and machine learning to examine attackers’ behaviors and correlate threats to identify and prevent potential security breaches. The platform is deployed without agents. ThreatX positions itself for companies focused on threat detection and prevention across APIs and applications with less emphasis on securing development and build processes.
San Francisco-based Traceable has raised over $77 million from Institutional Venture Partners, Tiger Global, Unusual Ventures, BIG Labs and Silicon Valley CISO, with the latest post money valuation at $450 million, according to Capital IQ. It was founded in 2018. The platform provides comprehensive API security across all three API security areas. Traceable aims to achieve what it calls “360 API Context,” a full understanding of its clients’ APIs.
Traceable tracks and correlates API transactions, whether benign or malicious, to help detect and stop signature-based, unknown, and business logic attacks. It provides insights to developers to help maintain best practices during testing and development processes. Traceable can deploy through agents or without agents. Based on our research, we believe Traceable positions itself to appeal to customers looking for a comprehensive API solution with strong application log history and analytics capabilities. Traceable’s website features customers such as Deserve, Houwzer, Jobvite and Informatica.
Keeping the connectors safe
The foundation of information technology’s transforming effect on society has been the ability to share information quickly and seamlessly across disparate systems, entities, and geographies. APIs are among the most important tools that make this possible, but their critical role also makes them a key point of vulnerability for malicious actors. We’re encouraged to see many innovative companies rising to the challenge of protecting APIs against ever more sophisticated attacks.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
