Quarterly insights: Cybersecurity
RSA 2024 and recent conversations: Key insights and takeaways
We present our key takeaways from the 2024 RSA cybersecurity conference and recent industry conversations.
In recent years, several factors have heightened concern about the fate of best-of-breed cybersecurity solutions. However, we see evidence that robust demand for both best-of-breed solutions and single-vendor platform solutions will persist for the foreseeable future.
The pace of cybersecurity M&A and financing remains incredibly robust, but we feel it is increasingly important to pursue capital strategies that align constituents around probable exit valuations rather than strategies premised on improbable unicorn valuations.
AI in cybersecurity was an even hotter topic at RSA in 2024 than in 2023. We see most cybersecurity companies adding AI capabilities to their existing solutions, but we are seeing more cybersecurity companies built from the ground up with AI engines at their core.
Looking at specific cybersecurity subsectors, data security stood out as seeing substantial innovation and winning much attention. Several factors appear to be driving this increased focus on data security.
TABLE OF CONTENTS
- Strong attendance suggests cybersecurity remains among the most active tech areas
- Best-of-breed vs. platform debate continues, but both do well
- Deal activity hype remains strong, yet unicorn valuation exits unlikely
- AI even more prominent, but levels of use vary widely
- Highly competitive data-security subsector garners meaningful attention and excitement
- Challenge of finding security professionals gets less air time
- Still an exceptionally fertile market
- Sector market activity: Cybersecurity index performance, M&A activity highlighting Darktrace, Venafi and Noname Security, and private placement activity highlighting Cyberhaven and ThreatLocker
Strong attendance suggests cybersecurity remains among the most active tech areas
While artificial intelligence (AI) has become the most topical area in tech over recent years, strong attendance at 2024’s RSA conference suggests cybersecurity remains among the most active tech ecosystems. This year, the buzz on the floor and at surrounding hotels and venues struck us as markedly greater than at the past two RSA conferences since the event resumed convening in person in 2022. The 2024 conference attracted over 41,000 attendees, over 650 speakers, and over 600 exhibitors, ranging from startups to large publicly traded companies. Conference attendance was up from the past few years and near 2017’s record 43,000 attendees. From presentations, meetings and discussions, it was evident that startup financing and merger and acquisition activity continue at a strong pace, indicating that despite the industry’s growing scale, opportunities for companies at all stages remain significant.
Best-of-breed vs. platform debate continues, but both do well
This year, like every year, we heard much debate over the appeal of best-of-breed solutions versus single-vendor platform solutions. In recent years, several factors have heightened concern about the fate of best-of-breed solutions. These include the success of massive platform players such as Palo Alto Networks (PANW), Fortinet (FTNT) and CrowdStrike (CRWD) and the fear that buyers struggling with the sector’s chronic talent shortage would increasingly be unable to take on the complexity inherent in running multiple best-of-breed solutions.
However, we have become convinced robust demand for both approaches will coexist for the foreseeable future, and our recent interactions have reinforced this view. Large enterprises with high cybersecurity risk profiles and large cybersecurity budgets continue to need and opt for best-of-breed solutions across subcategories, sustaining the kind of robust population of innovative cybersecurity startups that has characterized the broad cybersecurity market for decades. At the same time, many organizations have personnel, IT architecture, and other factors that make buying multiple cybersecurity functions in a unified, easy-to-use package more compelling and effective for addressing their cybersecurity needs.
Further, we’re seeing a trend that will likely make this debate less relevant in the future: an increased willingness of platform vendors to open their user interfaces to not only take feeds from smaller, best-of-breed vendors’ solutions, but also to integrate tightly enough to trigger actions on these best-of-breed vendors’ solutions. Our conversations indicate this shift is at least in part due to buyer demand. The change means buyers across the spectrum of company size and cybersecurity risk can better tap the advantages of both best-of-breed and single-platform solutions, supporting demand for both approaches. This may come with some shift in the locus of value in the cybersecurity ecosystem, but overall, it seems like a win for all constituents.
Deal activity hype remains strong, yet unicorn valuation exits unlikely
With all types of vendors able to succeed, it’s no surprise the pace of M&A and financing remains incredibly robust. This is despite what we see as a disconnect between early-stage valuations and exit valuations. To fuel growth and win market share in a market crowded with similar-sounding vendors while also minimizing ownership dilution, many early-stage companies receive large funding rounds at high revenue-multiple valuations (albeit slightly lower recently due to rising interest rates and other factors that have pushed the capital markets to be more disciplined).
Meanwhile, exit valuations have remained fairly stable, and very large exits remain the exception. Piper Sandler’s CEO Summit, which overlaps with the RSA conference, provided metrics that reflect this. They show median exit values for cybersecurity companies have been relatively steady at around 7.5 times revenue over the past six years. With declining cybersecurity sector revenue growth rates (see our April 2 report), that means it takes longer for these companies to grow to a level where their exit multiple provides good returns for early investors. Further, Piper Sandler reported that of the 1,110 cybersecurity transactions since 2018, only 15% involved exits greater than $100 million, only 9% greater than $300 million, and only 3% greater than $1 billion.
The gap between early stage and exit valuations puts pressure on companies to clear extremely high performance hurdles to warrant additional funding or interest from financial sponsors or strategic buyers at valuations that create good returns for investors. So, while there remains significant opportunity in the cybersecurity market, we feel it is more important than ever to pursue capital strategies that align constituents around probable exit valuations rather than strategies premised on improbable unicorn valuations.
AI even more prominent, but levels of use vary widely
AI in cybersecurity was an even hotter topic at RSA in 2024 than in 2023. AI-based cybersecurity solutions have long existed, but today they’re applied across the industry. A quick walk through the RSA conference floor made it clear most cybersecurity solutions have and highlight an AI story. Indeed, a company that doesn’t do so risks being perceived as falling behind, a risk that is pushing companies to promote their AI capabilities regardless of their utility or extent.
There is a broad spectrum of ways cybersecurity companies are adopting AI, but overall, we see a pattern like we saw with cloud adoption in cybersecurity. At the early stage of cloud adoption, most established cybersecurity companies created cloud-enabled versions of their historically on-premise solutions, and many eventually developed full cloud-based solutions. Simultaneously, some new cybersecurity companies began as cloud-based companies and developed their entire solutions in and for the cloud. Some of these natively cloud-based companies achieved tremendous success because of their cloud-centric origins. Examples include CrowdStrike, CloudFlare (NET), Zscaler (ZS) and SentinelOne (S).
With AI adoption, we see most cybersecurity companies adding AI capabilities to their existing solutions. These AI-enabled solutions typically use AI to augment and improve existing capabilities or help automate workflows previously done by humans. They also often use AI to quickly and easily make sense of substantial amounts of complicated data. Examples of the latter include using AI to scan emails and websites to identify potentially fraudulent activities and using AI to quickly detect cybersecurity threats by analyzing and identifying network patterns that may indicate attacks. Examples of AI for automating previously human workflows include executing routine patch management and normal system updates, which frees time for security analysts to focus on more complex problems.
We have started to see some cybersecurity companies built from the ground up with AI engines at their core. These AI-native solutions use AI as their vital component, coded from day one, to perform most of their applications’ major functions, and their AI foundation is central to their market positioning. Because the AI in these solutions often works autonomously, they can face challenges winning over buyers who perceive it as important to have humans monitor the solutions to ensure they are working effectively and correctly, to help explain what is happening and to guide decisions. DarkTrace, a company we featured in our network detection and response report last year, was founded in 2013 and is among the early examples of AI-native solutions. Many AI-native startups of the past few years are using incredibly dynamic and complex AI at their cores.
While AI-enabled solutions often rely on LLMs built by other companies and trained on proprietary data, AI-native solutions often use many of these other AI technologies. AI-native solutions continue to grow in complexity as new AI methodologies develop, and we expect them to increasingly combine multiple AI technologies in their solutions. One example of a company doing so is Cybral, an AI-powered security and continuous monitoring tool company that we connected with at the conference.
Conditional generative adversarial network illustration
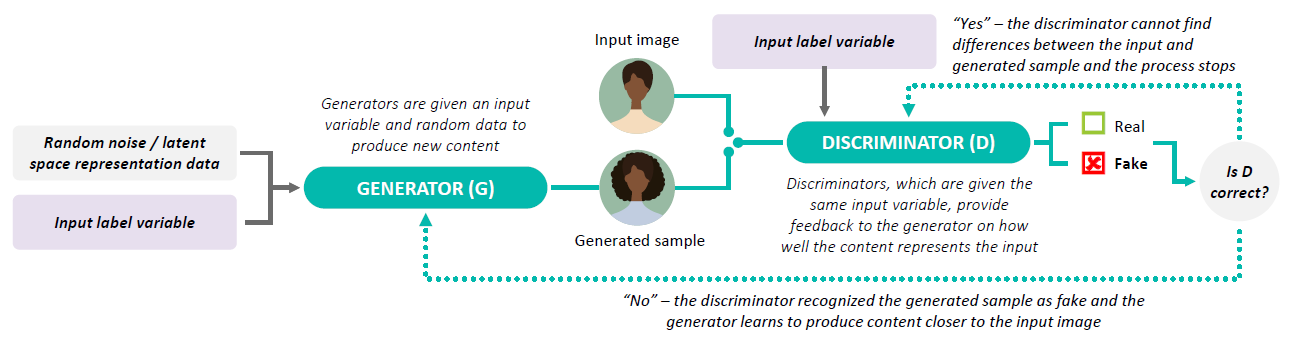
Source: First Analysis.
The following are some of the key AI technologies being deployed in cybersecurity:
- Large language models (LLMs): Deep learning LLMs train on enormous amounts of text data to understand and generate human language.
- Graph neural networks (GNNs): GNNs work with data structured as graphs, where each data point represents a node, or a particular entity (like a person in a social network), and relationships between nodes (such as a social network friendship) represent edges. Communication between nodes across edges manipulates and updates both. This information is used for predictive analysis.
- Generative adversarial networks (GANs): GANs use two neural networks – one that generates data and another that analyzes and compares the data to input data to ultimately train the generating network to produce an exact replica of the input data. (We provide more detail in our January report on deepfake detection.)
- Natural language processing (NLP): NLP enables machines to understand, interpret and generate human language that is meaningful and useful.
- Bayesian networks and probabilistic graphical models: These are particularly useful for modeling causal relationships and for reasoning under uncertainty. They update the probabilities of hypotheses as more evidence becomes available.
- Optical character recognition (OCR): OCR enhances and analyzes images and documents for text, matching for known characters and converting content into editable and searchable data.
Highly competitive data-security subsector garners meaningful attention and excitement
Looking at specific cybersecurity subsectors, data security stood out as seeing substantial innovation and winning much attention. “Data security” is a relatively new term for an area that has absorbed many historically distinct subsegments, including data encryption, data loss prevention (DLP), policy and access control, compliance management, data masking, and backup and recovery.
Several factors appear to be driving increased focus on data security. First, already enormous data volumes continue to grow rapidly. Second, where and how data is accessed and used is undergoing a revolution: Organizations increasingly store data in the cloud and enable myriad applications, both within and outside their purview, to access the data via application programming interfaces. Third, data for AI training has become central to many burgeoning AI applications, and managing the interactions between AI and data presents numerous challenges, such as authorizing AI’s access to data, enforcing access controls, managing data storage related to AI applications, and, in some cases, navigating regulatory scrutiny around AI. At the show and in follow-up meetings, we saw innovative startups that are tailoring solutions to address these challenges and established players that are expanding their data security portfolios to provide more comprehensive data security platforms.
Bayesian network illustration
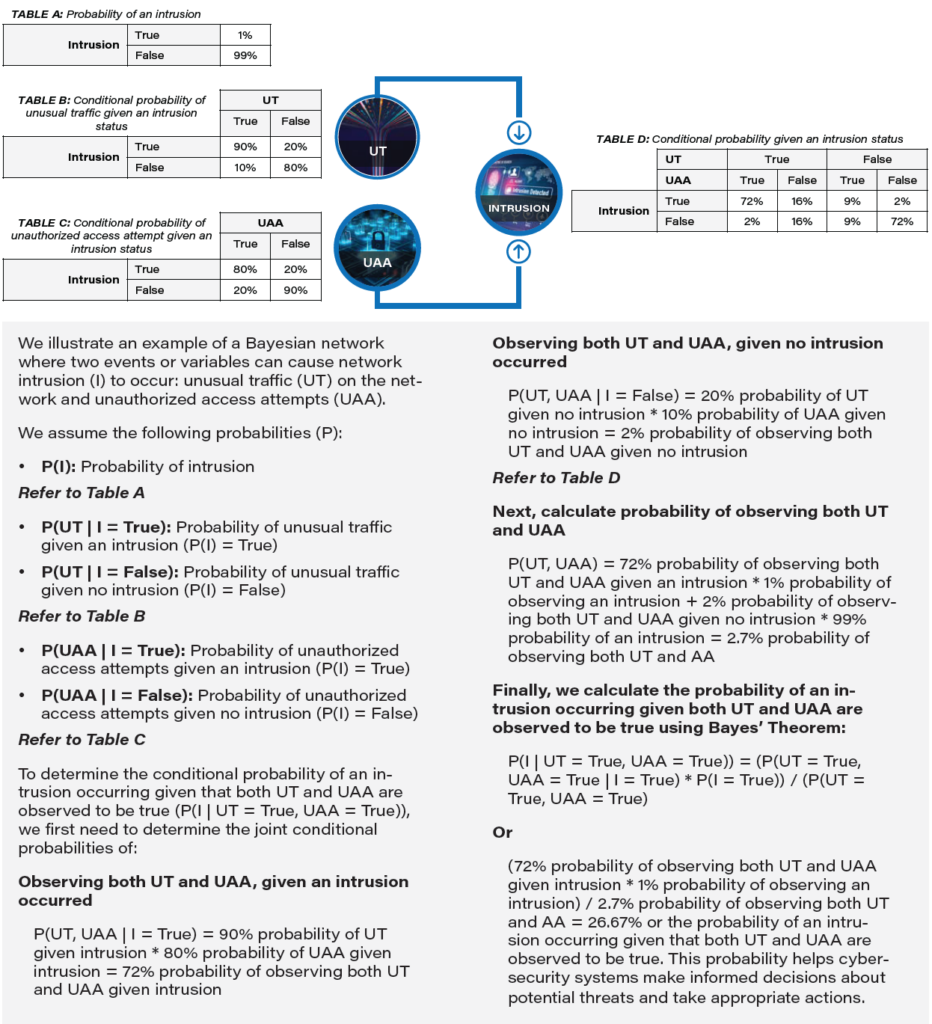
Source: First Analysis.
Challenge of finding security professionals gets less air time
At the 2022 and 2023 RSA conferences, we noted the substantial attention given to the ongoing cybersecurity talent shortage by speakers, exhibitors and attendees. That was not the case this year. We found this puzzling, because we see no evidence the shortage has materially abated and believe it remains a serious problem. While AI promises to significantly reduce cybersecurity human labor needs at organizations, any material effect on the labor market is some time off. Further, while layoffs at many high-profile technology companies took some pressure off the market, the effect was not significant relative to the supply-demand imbalance. Lastly, cybersecurity threats continue to proliferate and increase in sophistication, underpinning the need for more, higher-skilled and better-trained security operations personnel.
For now, we attribute the lack of focus on the talent shortage to AI’s dominance as a theme. We think the shortage will continue to be a material factor in the sector’s future but will watch more closely for signs of a fundamental change in talent supply and demand.
Still an exceptionally fertile market
RSA 2024 underscored a consistent truth: The perpetual race between increasingly advanced cyberattacks and defensive measures fuels a dynamic landscape ripe for innovation. Entrepreneurs find many opportunities to create impactful solutions, addressing ever-changing and growing market needs. Consequently, we see the cybersecurity sector as a compelling and robust area for ongoing investment.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
