Quarterly insights: Cybersecurity
RSA 2025 and recent conversations: Key insights and takeaways

We present our key takeaways from RSA 2025 and other recent conversations with operators, chief information security officers, acquirers and investors across the cybersecurity ecosystem.
Enterprise adoption of agentic artificial intelligence (AI) is accelerating, creating a surge in non-human identities that are challenging existing identity governance models. This identity sprawl is fast becoming one of the most urgent — and under-secured — problems in the enterprise.
AI remains a central design theme in cybersecurity software, but vendors and buyers are increasingly focused on tangible efficiency outcomes: reduced analyst workload, faster response times and improved coverage with fewer resources.
Network security is regaining strategic relevance as attackers shift away from hardened endpoints and toward lateral movement, unmanaged systems and traffic flows that traditional tools miss.
Merger and acquisition and financing activity remains steady, but the bar for investor and acquirer interest has risen. Companies with strong customer retention, scalable go-to-market models, and credible platform expansion narratives are best positioned in this more selective market.
Non-traditional acquirers and strategics backed by private equity and venture capital have become more active transaction participants, even as public cybersecurity acquirers take a more measured approach to M&A.
TABLE OF CONTENTS
- Cybersecurity remains a leading technology priority
- Capital discipline and an evolving buyer landscape
- Agentic AI and the rise of non-human identity risk
- AI in cybersecurity: Focus shifts to measurable efficiency
- Network security reclaims attention
- Final thoughts: A sector in constant motion, still defined by opportunity
- Sector market activity: Cybersecurity index performance, M&A activity highlighting Red Canary and Protect AI, and private placement activity highlighting Guardz and Cerby
Cybersecurity remains a leading technology priority
RSA 2025 reaffirmed that cybersecurity remains one of the most dynamic and resilient sectors of the economy. This year’s conference drew more than 42,000 attendees and 700 exhibitors — marking a return to near-record levels of participation. Attendance and engagement across sessions, side meetings and the expo floor reflected a continued depth of interest across acquirers, software buyers, vendors, and investors.
Importantly, the energy at RSA was not concentrated around a single trend. Discussions covered a wide range of topics — from integration of AI into the security stack and the challenges of autonomous agents to the re-emergence of network visibility as a core control layer. Despite macroeconomic headwinds, there remains a robust pipeline of cybersecurity startups, a healthy pool of acquirers and sustained demand from chief information security officers working to modernize their defenses and improve operational efficiency.
Capital discipline and an evolving buyer landscape
Cybersecurity continues to receive strong budget prioritization. According to Piper Sandler’s 2025 RSA keynote1, 89% of organizations expect to increase security spending this year, making it the top information technology budget category. This prioritization has supported relative strength in the public markets, where cybersecurity stocks have outperformed the broader enterprise software indices year-to-date. As of July 15, the First Analysis Cybersecurity Index had appreciated 33.8% — 22 points ahead of the S&P 500 and the Nasdaq. However, revenue growth expectations have moderated.
As we noted in our April report, the 2025 initial revenue growth guidance for public cybersecurity companies averaged 13.4%, down from actual 2024 growth of 17.2%. As top-line growth slows, capital markets have increased their focus on execution. Acquirers and investors increasingly emphasize gross revenue retention, gross margin, free cash flow generation, and scalable go-to-market strategies as key markers of business quality.
Revenue multiples have declined
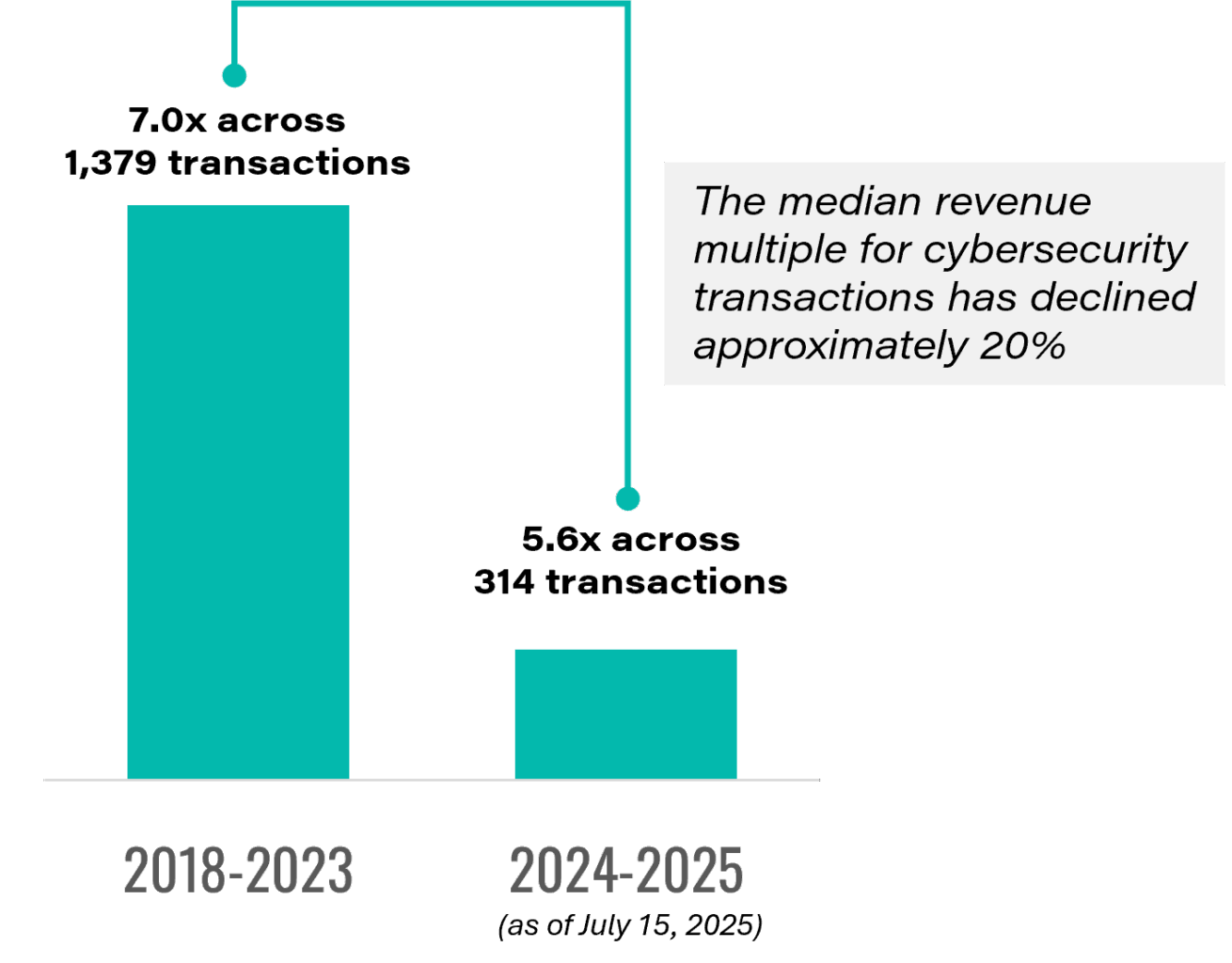
Source: First Analysis.
At the same time, the acquirer landscape is shifting. Traditional public cybersecurity strategic acquirers have been quieter. Piper Sandler noted that 16 of the 30 largest public cybersecurity vendors made no acquisitions over the past 18 months. In contrast, publicly traded companies that are not cybersecurity companies, such as Mastercard (acquirer of Recorded Future) and Crane NXT (acquirer of OpSec) have stepped in alongside private equity-backed and venture-backed platforms to drive continued transaction volume. With the exceptions of very large public technology companies with substantive cybersecurity offerings such as Microsoft, Cisco, Broadcom, and Google, publicly traded companies outside of cybersecurity have not historically been common acquirers of cybersecurity companies.
While the M&A market remains active, valuation discipline has become more pronounced. The median revenue multiple for cybersecurity transactions has declined approximately 20% — from 7.0 across 1,379 transactions in the years 2018 to 2023 to 5.6 across 314 transactions completed since early 2024.
This compression comes at a time when many private equity investments made between 2020 and 2022, which was a period of relatively high valuations, are approaching their expected exit timelines. With fewer initial public offerings and more selective acquirers, financial sponsors are increasingly focused on capital efficiency, strategic fit and financial durability. As a result, we expect further emphasis on realistic valuation frameworks and business fundamentals over the next 12 to 24 months.
Agentic AI and the rise of non-human identity risk
Among the most talked-about topics at RSA 2025 and in surrounding conversations was the emergence of agentic AI — autonomous software agents that interact with systems and data on behalf of users. These AI agents are rapidly finding their way into enterprise environments, performing tasks ranging from ticket routing and patch deployment to managing infrastructure policies and workflows and automating Tier 1 security operations.
This adoption has led to a dramatic increase in user identities that are machines, not humans. These machine identities already outnumber human users in many large organizations, and they are often poorly governed: over-permissioned, provisioned in bulk, and rarely decommissioned. Because they often fall outside the reach of traditional identity and access management (IAM) and privileged access management (PAM) solutions, they are becoming a frequent target for lateral movement, privilege escalation and long-term attacks.
AI agents being used to drive efficiency
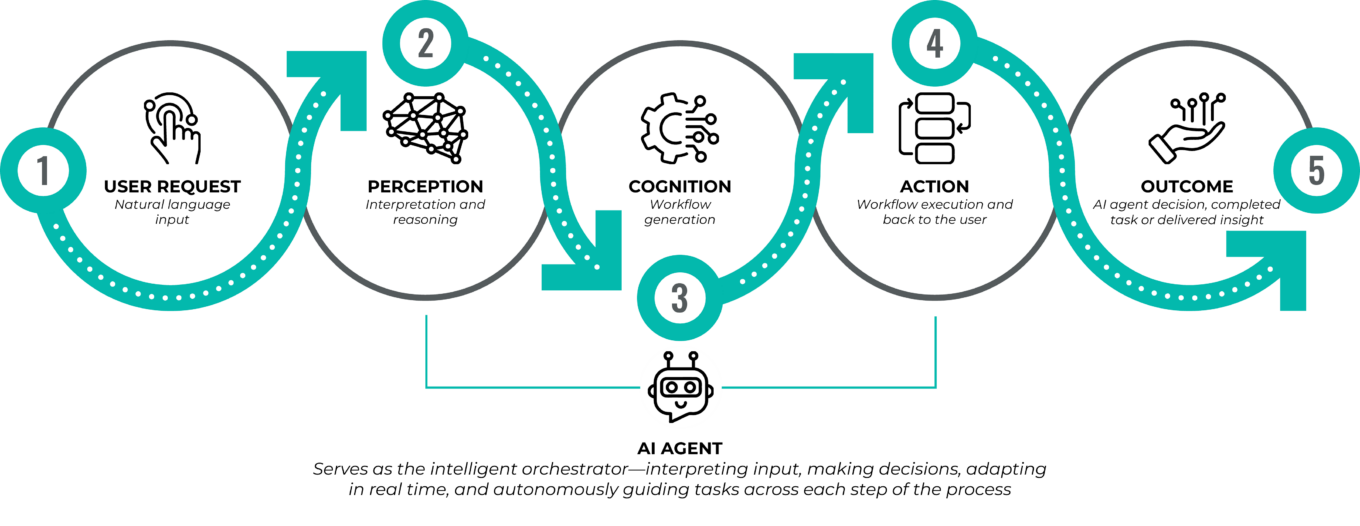
Source: Aisera, Landbase, First Analysis.
We are seeing a growing number of startups focused specifically on this challenge. New, innovative solutions are emerging to map and classify machine identities, enforce least-privilege access, and monitor agent behavior over time. Some vendors are integrating identity governance into continuous integration and continuous delivery (CI/CD) pipelines, which are automated DevOps workflows that streamline software delivery. These pipelines often rely on automation to maintain code quality, enforce policy and reduce human error. Other vendors are applying behavioral analytics to detect unusual agent activity, such as accessing systems outside typical patterns and initiating activity during off-hours. With agentic AI adoption accelerating, we expect this to remain a critical area of innovation and investment.
AI in cybersecurity: Focus shifts to measurable efficiency
AI remains a central theme in cybersecurity, but the tone has shifted. AI in cybersecurity was previously characterized by broad large-language-model integrations and conversational copilots. It has now evolved into more targeted and efficiency-driven applications.
At RSA 2025, we saw increased focus on solutions that help security teams reduce manual effort, speed up investigations and lower overall operational burden. In the security operation center, AI is being applied to enrich alerts, prioritize threats and draft preliminary incident reports. In IT operations, AI tools accelerate patching workflows and close tickets more quickly. In development, AI is being embedded in pipelines to support secure code reviews and early-stage vulnerability identification. While nearly every vendor now highlights AI capabilities, buyers are placing greater weight on depth of integration and actual performance impact — distinguishing between lightweight bolt-on features and AI that materially drives detection, automation and decision support.
This shift reflects an industry-wide focus on doing more with less. Security teams remain under pressure, tasked with managing more systems, more identities and more telemetry, often with fewer resources. In this environment, solutions that tie AI to tangible outcomes, such as shorter response times, fewer false positives, and reduced analyst fatigue, are earning a more favorable reception.
Network security reclaims attention
While endpoint protection remains a foundational layer in enterprise cybersecurity, we think RSA 2025 showed a resurgent interest in network security. In many discussions, we explored what might be the cause. We believe exceptionally robust innovation in endpoint detection and adoption of endpoint detection solutions in the past few years has make it more difficult for bad actors to penetrate organizations through this vector, leading them to look for other, easier attack vectors. This is analogous to the innovation and investments in perimeter security many years ago that caused bad actors to target more aggressively the endpoints to begin with. Today, attackers are turning to new avenues: internal lateral movement, Internet of Things exploitation, and cloud-to-cloud traffic flows that often go unmonitored.
Organizations are struggling to secure activity across fragmented environments — on-premise, hybrid, and multi-cloud — and are seeking tools that deliver broad visibility without requiring endpoint agents, which are cumbersome and sometimes impossible to deploy across entire environments. This has led to growing adoption of network detection and response (NDR) solutions that leverage behavioral analytics and static signatures to identify anomalous activity. Key selection criteria for these tools include ease of deployment, ability to span multiple architectures, and speed to actionable insight.
The resurgent interest in network security does not come at the expense of endpoint or other existing controls. Network focus is increasingly viewed as a necessary complement to these other elements, particularly as traditional perimeters erode and encrypted east-west traffic becomes more common. As chief information security officers seek broader and more cooperative detection frameworks, we expect continued growth in intelligent network visibility solutions.
Network detection and response averts attacks with comprehensive visibility across networks
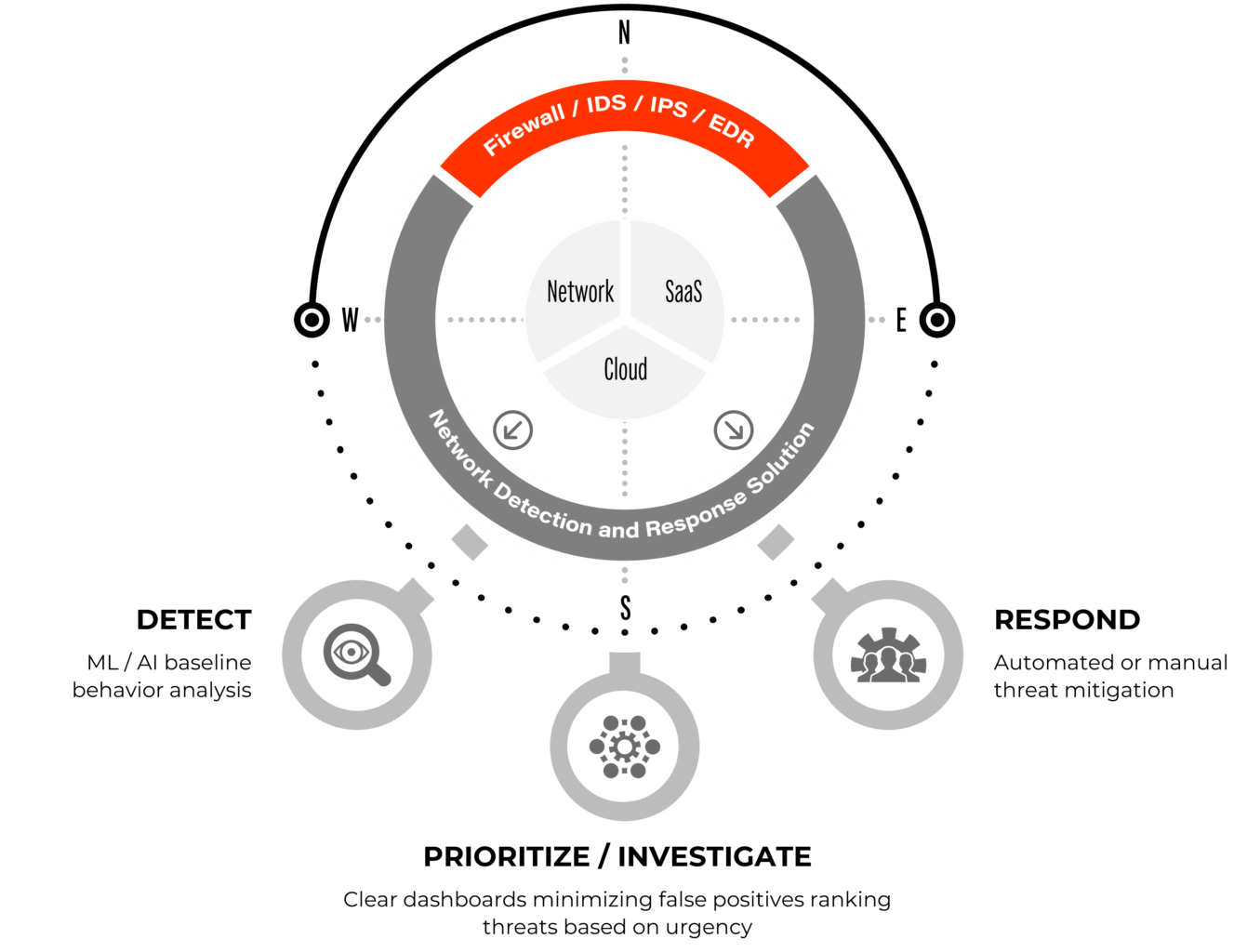
Source: First Analysis.
Notes: ML = machine learning. AI = artificial intelligence. IDS = intrusion detection system. IPS = intrusion prevention system. EDR = endpoint detection and response.
Final thoughts: A sector in constant motion, still defined by opportunity
All our second-quarter interactions underscored a consistent truth: Cybersecurity continues to be shaped by a dynamic interplay of threat evolution, technology advancement and organizational complexity. While tighter capital markets and more selective acquirers are reshaping the path to liquidity, the fundamental demand for effective security solutions remains strong — and is increasingly focused on automation, visibility and control.
We continue to see meaningful opportunity across the market, particularly in areas like agent identity management, network-level analytics, and AI-powered efficiency tools. As attackers evolve and environments become more decentralized, the need for adaptive and interoperable solutions will only grow. For entrepreneurs building in the space, and for the capital supporting them, we think cybersecurity remains one of the most fertile and enduring areas in enterprise technology.
1 Piper Sandler. (2025, April 28). Key takeaways from the Cybersecurity CEO Summit [Conference presentation]. Piper Sandler Cybersecurity CEO Summit, San Francisco.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
