Quarterly insights: Cybersecurity
Business of managing supply chain risks more critical than ever

Securing supply chains against cyberattacks and similar disruptions whose effects are magnified by the interconnectedness of modern infrastructure is a challenge that has been gaining priority for many years. Recent developments such as trade wars, the COVID-19 pandemic, global human rights protests and increasingly sophisticated state-sponsored cyberattacks have further heightened awareness of the critical need to understand and address supply-chain vulnerabilities.
Given the complexity and expansiveness of modern supply chains, this is a daunting and potentially expensive undertaking. In response, a number of companies are building innovative solutions to make this process more efficient and effective. We highlight several such companies.
Regulation is becoming an increasingly prominent driver of the impetus to assess and manage third-party risk, representing a tailwind for these solution providers.
We believe this confluence of forces, along with the inherently ever-evolving nature of risk, will make third-party risk management a large and fast-growing opportunity area for many years to come.
TABLE OF CONTENTS
Includes discussion of CYBR, QLYS and 12 private companies
- Business of managing supply chain risks more critical than ever
- Increased regulation also contributing to heightened vendor focus
- Large and long-lived opportunity for third-party risk management
- Cybersecurity index surges from its COVID-19 low, eclipses S&P 500, NASDAQ
- Cybersecurity M&A momentum slows in 2Q
- Cybersecurity private placements in line, average deal size close to two-year mean
Business of managing supply chain risks more critical than ever
Events over the past year have highlighted the need for entities to focus on their supply chains to understand which elements are critical and to ensure they can function through challenging situations. Recent examples of such events include trade wars that prompted new tariffs and trade restrictions, the COVID-19 pandemic with its myriad supply chain and other economic disruptions, protests related to the killing of George Floyd that have restricted transport and other movement in urban centers, and ongoing and increasingly sophisticated state-sponsored cyberattacks.
These events have occurred against a longer-term backdrop of computers having become essential components of most critical systems in all industries as well as a general move of IT infrastructures to cloud based architectures and reliance on cloud-based applications. We believe the convergence of these developments has created a tipping point for third-party risk management to become a central focus for all participants across the supply chain. We expect all types of vendor risk to see increased scrutiny, including analysis of geographic, financial, and reputational risk. But due to the reliance on increasingly interconnected computing systems and networks as well bad actors’ ability and strategy to attack infrastructure through connected third parties, third-party cyberattacks are on the rise.
A November 2018 Ponemon Institute publication reported that 61% of surveyed U.S. company chief information security officers reported a data breach caused by a vendor or third party in 2018, up from 56% in 2017 and 49% in 2016. An additional 22% did not know if they had been breached through a third party or not. And while the number of third-party breaches has been rising, as shown in Table 1, the impact of these breaches as measured by information compromised has risen at a far faster rate. We think this reflects the greater interconnection of third parties and the greater damage breaches can cause. With such third-party attacks on the rise, we think assessing, managing and mitigating cyber risk will be at the fore and sometimes integrated with non-cyber considerations to gain a holistic and more meaningful context for managing overall third-party risk.
For almost all situations, a starting point in assessing cyber risk is identifying all the vendors an entity uses. This is not as straightforward as one might think. First, entities typically use assets and applications on their networks from numerous vendors without the knowledge of administrators tasked with controlling risk. We think the move to working at home exacerbates this challenge.
According to a post-COVID-19 survey of about 2,900 office workers by consulting firm Global Workplace Analytics, the percent of respondents working from home at least one day per week has grown from 31% prior to the pandemic to 88%, with 77% working from home full-time, up from 9% pre-COVID-19. Discovery tools such as Qualys’ IT asset inventory, which automatically discovers and classifies, to the extent possible from this type of scan, anything on a network, can aid significantly in the effort to identify vendors across such highly distributed networks. Second, each asset that is identified may have myriad subsystems from different vendors with each subsystem having its own risks.
While IT assets often have many subsystems (think of a computer with its processor, screen, operating system keyboard. mouse, camera, casing and microphone, all coming from different suppliers), they are some of the easier to understand because of how they are designed and report information. Operational assets, such as turbines and compressors, also have myriad subsystems that are often very hard to identify but just as critical to understand and monitor for third-party vendor risk. We think owners of such assets will increasingly focus on this area in the future.
TABLE 1: Data breaches and records lost, 2012-2019
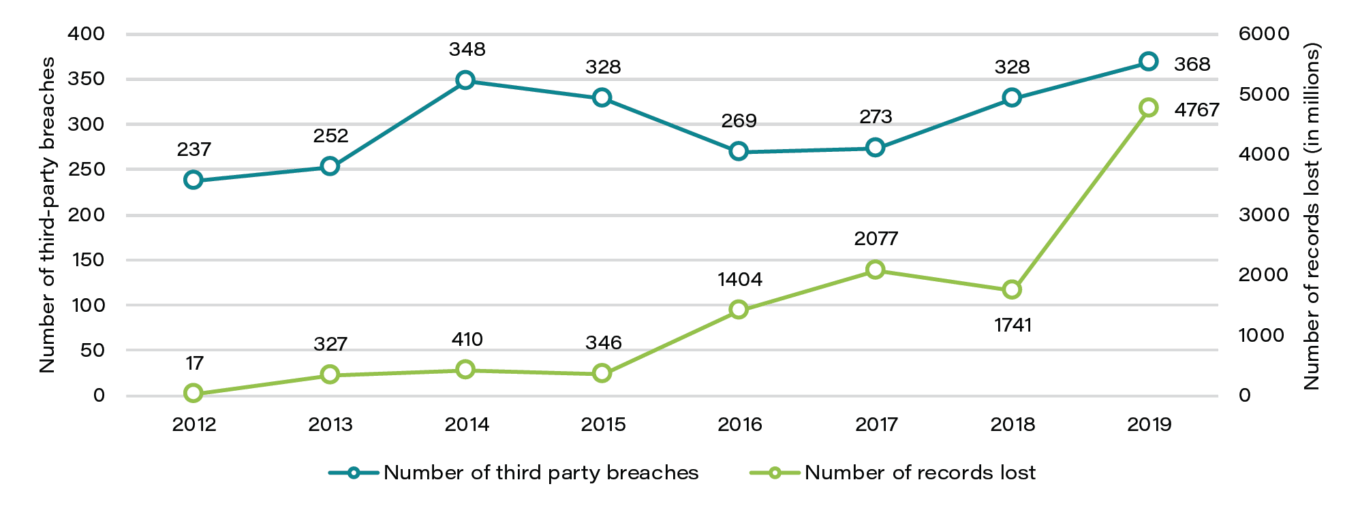
Source: Risk Based Security Inc.
Once identified, assets and vendors can be grouped into risk categories depending on what they do and which other systems they interact with. The level of effort to discover, monitor and mitigate risk depends on the type of asset, not necessarily its vendor. For example, a utility that purchases a General Electric refrigerator for its break room has a very different view of GE from a risk perspective than one that purchases its primary turbines from GE.
Because some vendors and assets provide relatively discreet, non-critical products and services, they may be deemed irrelevant from a risk perspective and require no further scrutiny. However, even some seemingly benign assets such as the refrigerator can pose risks if they have IP addresses and connect to a network — as some “smart” refrigerators do — or if they require service from on-site technicians from vendors with inadequate hiring practices relative to the security needs of the customer.
For vendors and assets that require further analysis, we think companies will deploy a layered approach with specific combinations of assessment, management and mitigation procedures most appropriate for each type and level of risk.
A starting point for many is assessing the security posture of a vendor’s publicly facing assets and other assets for which information is readily available and easily obtained in an automated manner based on public sources. Companies such as SecurityScorecard, BitSight and RiskRecon (a MasterCard company) are leaders in this area and provide a risk score (sometimes customizable for the attributes a customer is most focused on) based on such information. Depending on how critical a vendor is to an entity’s mission as well as the score, this step can be the end of the investigation, a factor influencing next steps or just one small factor in the overall risk assessment.
When taking the analysis a level deeper, companies often ask vendors to complete questionnaires about their security practices. Figuring out which questions to ask, tracking responses and following up on missing or confusing answers can be extremely time consuming. There are several companies such as OneTrust and Panorays that provide platforms to help automate and monitor this process, often integrating security scores provided by the companies mentioned above.
For vendors responding to these questionnaires, filling them out is time consuming. To address this pain point, companies such as Whistic and ThirdPartTrust highlight their platforms’ ability to not only automate the task of creating and tracking responses but also to respond to security questionnaires in standard formats and then share these with requesting parties. This relieves a heavy burden of having to respond to each questionnaire piecemeal. Of course, efficiency is helped by having some standard questions and formats. For example, Whistic natively supports the following commonly used questionnaires:
- Center for Internet Security — CIS Critical Security Controls (CIS First 5 / CIS Top 20)
- Cloud Security Alliance — Consensus Assessments Initiative Questionnaire (CAIQ)
- National Institute of Standards and Technology — NIST (800–171)
- Shared Assessments Group — Standardized Information Gathering Questionnaire (SIG / SIG-Lite)
- Vendor Security Alliance — VSA Questionnaire (VSAQ)
Key vendors may require scrutiny beyond self-reported questionnaires. Many companies turn to some combination of 1) hiring outsourced resources with subject matter expertise to follow up on questions, 2) continuous monitoring of compliance, 3) vulnerability monitoring and even 4) partnering with outside audit firms to verify that statements made by vendors are accurate. Venminder, CyberGRX and Fortress Information Security[1] are examples of entities offering this level of solution.
CyberGRX is interesting in that it offers an exchange of vendor assessments. It believes much of the vendor assessment process is redundant and aims to reduce the price of assessments by bearing the cost of an assessment itself and then selling the assessment to (hopefully) numerous customers on its exchange. A limitation of CyberGRX’s approach is that companies cannot modify assessments for their specific needs.
Fortress also has an exchange offering but is highly focused on a few verticals, such as regulated utilities. It allows its customers flexibility to customize assessments to their needs and believes others in the industry will desire these highly specific assessments. It then helps these customers resell their assessments on its Asset to Vendor network, enabling them to recover some (or theoretically all) of their costs for the assessments. Because it takes such a vertical focused approach, Fortress also offers assessments of specific assets (in addition to vendors) as well as related cyber monitoring, vulnerability management and patching services for these assets.
Most of the solutions discussed here can be integrated into broader integrated risk management (IRM) or governance, risk and compliance (GRC) solutions. While these broader platforms from companies such as RSA (through its RSA Archer product) and Navex accept data from a wide variety of sources, they also may have their own proprietary modules that can provide some of the above functions.
Increased regulation also contributing to heightened vendor focus
A growing alphabet soup of regulations is focused on third-party risk, and we expect significantly more to come. Historically, industry groups have taken the lead in developing and enforcing some of the more effective security frameworks. For example, PCI DSS (the Payment Card Industry Data Security Standard) has been enforced for more than a decade for credit cards.
However, we think the tide is turning to governments and associated regulators taking a more active role. The European Union’s General Data Protection Regulation, which became effective in 2018, is a well-known example as is the California Consumer Privacy Act, which became effective at the start of this year. These two regulations tend to deal more with data protection and privacy rights rather than critical infrastructure third-party vendor risk.
In early 2019, the European Banking Authority published revised guidelines that include a focus on third-party vendor risk. The guidelines address outsourcing arrangements, making it clear that financial institutions are responsible for the performance of their critical systems even if they are run by or located at a third party and that those institutions must devote adequate resources to assess and manage this risk. Perhaps even more sweeping is the U.S. Department of Defense’s v1.0 of its previously announced Cybersecurity Maturity Model Certification (CMMC) initiative.
Released earlier this year, it requires each of the more than 300,000 DOD contractors to become certified at various levels beginning in October this year (subject to a five-year phase-in). While this is still a work in progress, requests for proposals are being regularly issued to enable this framework, and we think it points to a new level of seriousness for the government in regard to critical assets as well as a greater appreciation of how even relatively small third-party contractors can pose serious risk to national security.
In addition to focusing on obvious military- and government-owned assets, the U.S. government is putting greater focus on assets owned by private institutions. The fight to keep Huawei components out of 5G networks in the United States and among its allies has been widely reported. The power grid is receiving less attention. But in November last year, the Wall Street Journal reported on what were believed to be foreign-nation-state-sponsored coordinated attacks on more than a dozen relatively small U.S. utilities with operations in 18 states.
Measures that should help reduce the potential success of such incidents in the future include enactment of the North American Electric Reliability Corp. (NERC) Critical Infrastructure Protection Standard CIP-013-1, which mandates bulk electricity producers implement specific security controls over their supply chains or face fines of up to $1 million a day for non-compliance. Putting a further exclamation point on the risk and seriousness of protecting the power grid, President Trump on May 1 signed an executive order declaring unrestricted access to systems supporting the bulk power system a national threat and issued several directives including ordering an inventory of critical components designed or produced by entities under control of foreign adversaries and devising ways to “identify, isolate, monitor, or replace such items as soon as practicable.”
Large and long-lived opportunity for third-party risk management
The challenges of adequately assessing, monitoring, and managing third-party risk are substantial. Further, we expect these risks to constantly evolve, as they do in the broader cybersecurity realm, with unanticipated events, adoption of new technologies, and new modes of attack by malicious actors revealing ever more vulnerabilities. As such, we believe third-party risk management will be a large and fast-growing opportunity area for many years to come.
[1] First Analysis is an investor in Fortress Information Security through its venture capital funds.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
