Quarterly insights: Cybersecurity
RBVM – key to not getting crushed by the vulnerability boulder

Patching all an enterprise’s cybersecurity vulnerabilities is a Sisyphean task that’s only made harder by a scarcity of qualified cybersecurity personnel.
Risk-based vulnerability management (RBVM) solution providers make it easier for enterprises to protect their business with vulnerability prioritization technology that optimally focuses their remediation efforts on the vulnerabilities that are most important in the context of each business. Several recent events highlight how the RBVM space remains as interesting and important as ever.
We examine the considerations related to each of the three elements of the RBVM framework (vulnerabilities, assets and threats), some of the main approaches to RBVM, and some of the companies focused on moving solutions forward.
TABLE OF CONTENTS
Includes discussion of CSCO, QLYS, RPD, TENB and seven private companies
- A Sisyphean task
- The universe of vulnerabilities
- Which vulnerabilities do I have?
- Adding threat intelligence
- Assessing damage potential
- Choosing RBVM solutions
- One size does not fit all
- A sample of solution providers
- Making an impossible task a little more possible
- Cybersecurity index continues to outperform the Nasdaq and S&P
- Q2 cybersecurity M&A activity continues to slow
- Q2 cybersecurity private placements sustain recent pace
A Sisyphean task
It is no secret that today’s IT organizations face a Sisyphean task in trying to patch all known vulnerabilities, a challenge that’s only made harder by a scarcity of qualified personnel. To help manage the task, IT security departments often advise IT staff on which of the myriad vulnerabilities they should prioritize based on a variety of factors. At its highest level, this is called risk-based vulnerability management (RBVM), and the solutions used to aid in this task are usually referred to as either RBVM software or vulnerability prioritization technology (VPT), with the terms being generally synonymous.
This challenge of how to best prioritize vulnerabilities is decades old, and solutions have continuously evolved over this time. But several recent developments highlight how the space remains as interesting and important as ever. These include government-issued guidelines suggesting a risk-based approach to vulnerabilities to help combat ransomware, the May 14 announcement that Cisco will buy VPT specialist and leader Kenna Security, and the June 8 announcement that risk-based cybersecurity firm Brinqa received $110 million in its first institutional funding round.
The basics behind a risk-based approach are simple, and the framework shown in the Venn diagram in Table 1 can be applied to almost any vulnerability assessment, computer-related or not. The three main considerations are vulnerabilities (in this case, generally known vulnerabilities as described below), assets (enterprises’ computer hardware, operating systems and applications), and threats (bad actors and malware that exploit the vulnerabilities).
But the simplicity of this framework belies daunting challenges to practical implementation, particularly for mid-size to large enterprises, which often face an overwhelming number of vulnerabilities and often have incomplete asset inventories. Furthermore, threats change dynamically, and the business impact of a successful attack by bad actors is extremely difficult to predict.
TABLE 1: Risk-based approach – vulnerabilties, assets, and threats
Source: First Analysis.
Below, we examine in more detail the considerations related to each of the three elements of the framework, some of the main approaches to RBVM, and some of the companies focused on moving solutions forward.
The universe of vulnerabilities
Gaining visibility into vulnerabilities is probably the easiest step. Once a vulnerability is publicly disclosed, it is added to the National Vulnerability Database (NVD) managed by the National Institute of Standards and Technology and to the Common Vulnerabilities and Exposures (CVE) database managed by MITRE, a not-for-profit research organization focused on security and technology for government.
Another public interest organization, the Forum of Incident Response and Security Teams, maintains the Common Vulnerability Scoring System (CVSS), which assigns NVD and CVE listed vulnerabilities a score from 0-10, with 10 being the most severe. This is a first step toward prioritization. In 2020, the databases registered roughly 18,000 new vulnerabilities, the majority of which were classified as having critical or high severity. So trying to patch only the most critical by this criteria does not do much to simplify the task.
Which vulnerabilities do I have?
TABLE 2: Common Vulnerability Scoring System (CVSS) severity distribution over time
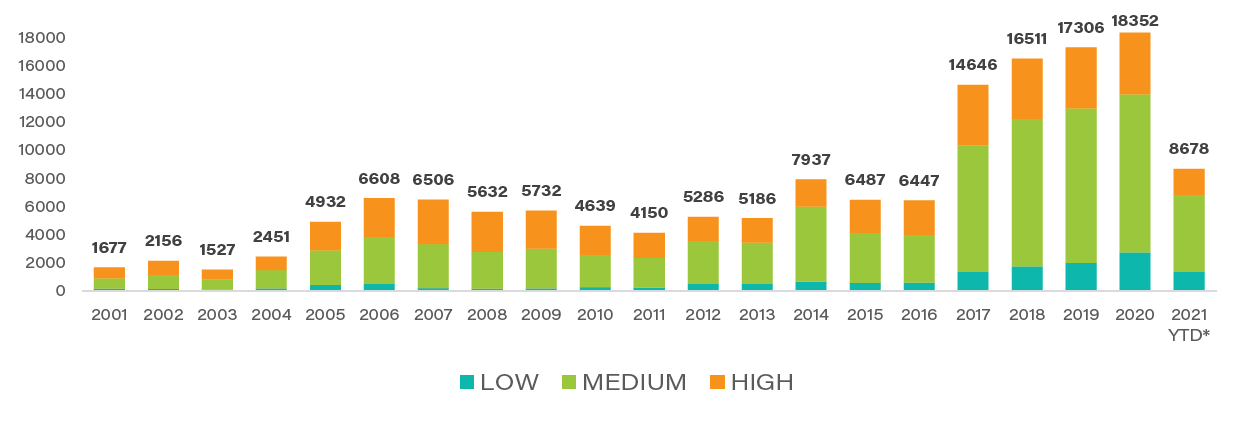
Source: National Institute of Standards and Technology, U.S. Dept. of Commerce.
Notes: *2021 data as published on the NIST website as of June 25, 2021.
Many vulnerabilities will not be relevant to an enterprise, such as an Oracle database vulnerability for an enterprise that uses purely Microsoft products. However, most enterprises don’t have an exhaustive, centralized inventory of all IT assets and the systems and applications they host. Thus, a good asset discovery tool that queries the environment to record what assets and operating systems are present is critical to effective vulnerability management. Once the enterprise maps vulnerabilities against a comprehensive inventory or scans all assets for known vulnerabilities, it will have a good idea of which vulnerabilities are present in its environment and can start the prioritization process in earnest.
TABLE 3: Typical vulnerability management process
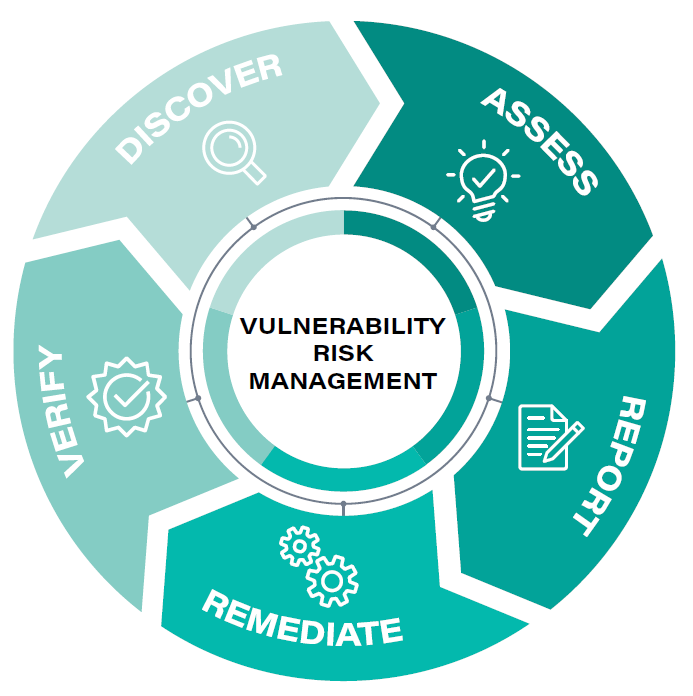
Source: First Analysis, industry literature.
Adding threat intelligence
Sophisticated solutions go well beyond a CVSS score to determine which vulnerabilities are most critical to address. Such solutions gather data from proprietary and public sources to detect trends regarding which vulnerabilities are actively being exploited by bad actors and what type of momentum they have. Some solutions even monitor discussion groups and experimental activities on hacking sites to predict which unexploited vulnerabilities are likely to be exploited soon. While this functionality was rare a decade or so ago, it is integrated into most of the leading solutions today.
Assessing damage potential
Once enterprises understand what vulnerabilities are present in their environment and which are most likely to be exploited, they have accomplished a substantial feat. But the list of vulnerabilities will still be too long to practically address in its entirety. From this point, enterprises need to prioritize the vulnerabilities by assessing their potential to cause material damage.
As a contrived example of why this is important, there may be two new vulnerabilities involving operating systems that threat data shows are likely to be exploited, one CVSS level 10 and one CVSS level 4. At one enterprise, it happens that the level 10 vulnerability is only on one computer used by visitors to record their names and dates of visit. The data is stored locally on the computer, and the computer is not connected to any network or other systems. The level 4 vulnerability is running on hundreds of networked computers, including the primary work computers of the IT, research and development, and finance department staff. In this case, fixing the low level-4 threat is much more important than fixing the high level-10 threat.
There is no simple way to gain visibility into potential business impact of an exploited vulnerability. To help address the issue, some companies use network maps that can simulate the effect, including what systems will be down and what data could be lost. This ability to see what systems are affected and the snowball effect on other systems can be exceptionally helpful in the prioritization process.
However, to our thinking, it still falls short of ideal. The holy grail of risk analysis is translating this knowledge of what IT systems will be affected into expected business impact. That is, what is the impact in terms of factors such as human safety (very important in critical infrastructure environments), monetary losses, reputation, customer satisfaction, and regulatory compliance. The list of areas to consider is long, complicated and multidimensional. Some assets are critical in terms of uptime but contain no valuable information. Others can be down for days but contain highly sensitive information. Ideally, prioritization should also map vulnerabilities against these types of considerations. But security and IT staff, while possessing exceptional technical knowledge, usually don’t have sufficient knowledge to assess the impact of system failures in such a broad range of non-technical business areas. In fact, it would be rare to find any single person or department with knowledge sufficient to accurately assess these risks across an enterprise.
In practice, enterprises that tackle this last step usually have security and IT personnel assign a risk number to each asset or guess at a monetary value to the business. This is far from ideal, so we think solutions that can help systematize bringing a diverse range of institutional knowledge into the impact analysis calculation and also use machine learning, artificial intelligence (AI) and other technologies to further calculate business risk is where much of the innovation in RBVM is happening and where it will continue for the foreseeable future.
Choosing RBVM solutions
In selecting RBVM tools, enterprises typically consider several key factors.
Ease of implementation. To be effective, RBVM tools should make it easy to understand prioritized vulnerabilities and make it efficient to remedy them. User interfaces should give clear guidance to IT staff, and the software should automate some or all remediation. Often, RBVM tools integrate with ServiceNow or other IT workflow systems. The quality of these integrations and the ability to leverage existing workflow technology and processes are key to successful RBVM programs. In this context, we note risk-based prioritization is being implemented in many other areas of security. Most relevant for this discussion are 1) asset management, 2) application security, which is often tested dynamically in dynamic application security testing (DAST) or statically in static application security testing (SAST) that yield their own list of results similar to vulnerability scans, and 3) container security. Many RBVM solutions have already integrated these capabilities, and we feel most of the market will quickly follow.
Number and scope of inputs analyzed. The more inputs an RBVM solution considers, the more comprehensive and granular results can be. As a result, many competitors highlight the number of integrations they have with third-party systems and data sources to differentiate their solutions.
Machine learning and AI capabilities. The strength of a solution’s machine learning and AI capabilities can be key to its ability to optimally prioritize vulnerabilities taking into account risk and mitigation time and effort. This is very difficult for purchasers to evaluate, but through pilot programs and references, enterprises can get a sense of how a solution will perform in their own environment. Enterprises can also use outside audits or engage a firm to “red team” attack the enterprise to help assess a solution’s effectiveness over time.
One size does not fit all
Creating, implementing and maintaining a sophisticated RBVM plan can be expensive and time consuming, so companies need to weigh the costs and benefits in selecting solutions that best meet their needs. Smaller, IT-light companies may find a relatively simple program is sufficient. For these companies, low price and easy implementation may be the key buying criteria, with number of integrations and modeling engine sophistication and flexibility taking a back seat. We think larger companies – particularly those responsible for critical infrastructure – will lean toward comprehensive solutions with sophisticated risk modeling capabilities at the top of the criteria list.
A sample of solution providers
Qualys (QLYS), Rapid7 (RPD) and Tenable Holdings (TENB)dominate the vulnerability management market. All three offer solutions that help prioritize patching based on risk. For customers who want broader or higher levels of risk analysis from more specialized vendors, these vendors make it easy for the vulnerability data they collect to be used as a data source for products from more specialized vendors.
Qualys’s VMDR (Vulnerability Management, Detection and Response) offering aims to identify and categorize all known and unknown IT assets on a network. It identifies misconfigurations and vulnerabilities on these assets and uses correlation and machine learning to prioritize remediation tasks. Finally, it includes easy, one-button remediation solutions. While Qualys VMDR is appropriate for many needs, Qualys also partners with leading risk-based solutions such as Brinqa, Kenna Security, and RedSeal for customers who want the broader risk approach these vendors provide.
Rapid7’s InsightVM enables customers to apply Rapid7’s vulnerability research and knowledge to obtain an exceptionally granular “Real Risk Score” that rates risks on a 1-1,000 scale and then makes it easy to track remediation and integrate into other IT task management systems.
Tenable’s Lumin solution provides a “Cyber Exposure Score” based on a mapping of the customer’s vulnerabilities against asset criticality and threat data to provide clear guidance and focus remediation efforts. Lumin displays metrics in easy-to-understand dashboards to manage risk and see how it changes over time. Earlier this year, Tenable bundled Lumin, Tenable.io (its core vulnerability management solution), web application security, and container security into a new offering called Tenable.ep. This is its most comprehensive solution to address and prioritize threats across the growing attack surface.
Privately held Balbix combines asset discovery, threat research and its AI engine to help companies get a clear view of where risks are highest and develop remediation plans. In our opinion, Balbix’s user interface and dashboards, which provide numerous ways to visualize risk across multiple dimensions (location, types of asset, functional area), are exemplary.
Privately held Brinqa is a knowledge platform that ingests data from myriad sources and enables enterprises to create knowledge graphs that highlight risk related to cybersecurity. It currently offers products for four cybersecurity areas, one of which is vulnerability management. Brinqa is one of a handful of companies that has started with this data-heavy, broad-based, and cross-functional view of risk and risk assessment that is more complicated to implement than some solutions but may position it well as the industry evolves, particularly for enterprises where the consequences of an exploited vulnerability are high.
Privately held Fortress Information Security[1] helps regulated companies operating critical infrastructure focus on their cybersecurity risk. It is best known for its vulnerability compliance and third-party vendor risk management solutions. However, it has worked with critical infrastructure customers to develop a vulnerability management solution that addresses the prioritization issue from an exceptionally high level and with a broad scope. We feel specialized companies like Fortress, because their customers manage critical infrastructure and thus must invest in comprehensive, holistic risk mitigation, warrant monitoring in this market.
Privately held Kenna Security, which has announced it will be acquired by Cisco later this year, is arguably the leading pure-play specialist in the market. Kenna has an incredibly broad array of integrations from which its analysis engine pulls data, and it was very early in promoting an ability to predict which vulnerabilities will be exploited in the future based on its broad threat intelligence capabilities. Its solution enables customers to easily take actions based on its findings. The list of Kenna’s leading customers is a testament not just to Kenna’s prioritization acumen, but also the product’s usability. Cisco plans to integrate Kenna into its SecureX platform, and we think it will quickly bring Kenna’s capabilities to the large SecureX customer base.
Privately held NorthStar is another company taking a data-centric approach to the market. Rather than recreate data that already exists in an organization, it ingests a wide array of data gathered by other systems within an enterprise and then provides a platform for customers to flexibly and accurately assign real business risk levels to assets. Though it is a relatively early stage company, we think NorthStar’s focus on data combined with a process to accurately assign risk specific to each customer’s environment may prove a winning formula as the industry matures.
We also highlight Skybox Security and RedSeal, both of which map enterprises’ entire attack surface, taking into account existing cybersecurity controls and other important factors. Customers use Skybox and RedSeal solutions for a number of cybersecurity purposes, vulnerability management being just one. Their RBVM modules can visualize not just which assets would be compromised if a vulnerability were exploited, but how the attack might propagate through the enterprise, which downstream assets might be at risk and what other mitigation efforts might be deployed to lessen consequences. The power of these visualization platforms makes them compelling to use in coordination with other vulnerability management tools to form a more complete solution.
Making an impossible task a little more possible
Like Sisyphus pushing his boulder up the hill, enterprises will likely struggle with constantly evolving cybersecurity vulnerabilities forever. Risk-based vulnerability management technologies that make it easier for enterprises to protect their business are the key to not being crushed by the vulnerability boulder. We foresee strong and growing demand for these technologies.
[1] First Analysis is an investor in Fortress through its venture capital funds.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
