White paper: Cybersecurity
The new Endpoint Security landscape: Exploring an important growth area

We frame and assess the endpoint security landscape, discussing dynamics such as market drivers and the growth outlook, solution trends, hurdles facing next-gen market evolution, positioning of 25 or so private players, and an overview of eight key players. Some of our commentary highlights include:
Two main approaches. Prevention and detection-plus-response are in our view emerging as two primary next-generation endpoint security approaches. Both paradigms have strengths and weaknesses, and we believe prevention is garnering most interest while detection platforms (including usually greater investigation capacity) may be particularly valuable for resource-richer enterprises.
Agent consolidation significant issue. The industry-wide move toward greater security consolidation and more strategic buying is also felt on the endpoint. Companies look to simplify their endpoint agents and related management burden toward a smaller number of endpoint solutions featuring the necessary security functions while ensuring user productivity and easier deployment/management.
Two key adoption factors. Despite fast growth (off a relatively low base), next-gen adoption is still in early innings. We see break-out traction depending on more compliance certification, allowing antivirus budget to be spent on new solutions, and greater familiarity and comfort with new technology approaches (it is a noisy market causing some customer confusion).
TABLE OF CONTENTS
- Rethinking endpoint security
- The next-generation endpoint security market
- The next-gen landscape: What’s going on?
- What’s driving new endpoint security solutions?
- Endpoint security primer: What is it and why does it matter?
- Company profiles
Includes profiles of: Carbon Black, CrowdStrike, Cylance, Digital Guardian, FireEye (FEYE), Palo Alto Networks (PANW), Symantec Corp. (SYMS) and Tanium.
Rethinking endpoint security
‘Endpoint security’ refers to directly protecting end-user-accessed, network-connected devices, such as laptops. It is arguably the most valuable and vulnerable segment of an organization’s infrastructure.
While endpoint security has existed for a long time (mainly in the form of antivirus), this report seeks to orient readers about the newer ‘next-generation’ endpoint landscape that is building up and commanding growing attention. Endpoints now require multiple security solutions, not just antivirus. (How many solutions enterprises will tolerate is an important question in this evolving market.) It’s a landscape featuring easily more than 25 private companies and significant associated venture funding, as well as a handful of public security players sporting next-gen endpoint solutions, along with legacy antivirus players seeking to evolve with the market.
We touch on market and technical dynamics, as well as highlight a handful of public and private players that feature next-gen offerings. We aim to supplement over time this door-opening effort with a series of follow-ups that serve as ongoing commentary about what should become an increasingly meaningful security growth area.
Pockets of urgency and a general recognition something must be done. Need for more robust endpoint protection is fairly widely understood. For instance, a late-2015 Promisec survey found that more than two-thirds of 150 C-level IT professionals agree that endpoint protection is their top security concern. More recently (April 2016), a Ponemon Institute survey found 61% of respondents say endpoint security is becoming a more important part of their organizations’ overall IT security strategy.
Pushing the issue to the fore are fundamental dynamics, such as 1) recognition that existing solutions (mainly antivirus), and perimeter-only architectures (firewall-centric), are usually inadequate and/or too system-heavy to form a reliable, lightweight endpoint barrier. At the same time, 2) increasingly sophisticated, ongoing breaches (Yahoo!, the Democratic National Committee, Verizon Enterprise Solutions, and others) pose greater business risk and render overall security posture a more visible board/governance issue.
The still relatively early-stage market is seeing adoption pains, but nonetheless, well-known security reseller Optiv reports that the “vast majority” of its roughly 600 Fortune 1,000 clients feature an endpoint-security refresh as a roadmap key, with an emphasis on advanced threats.
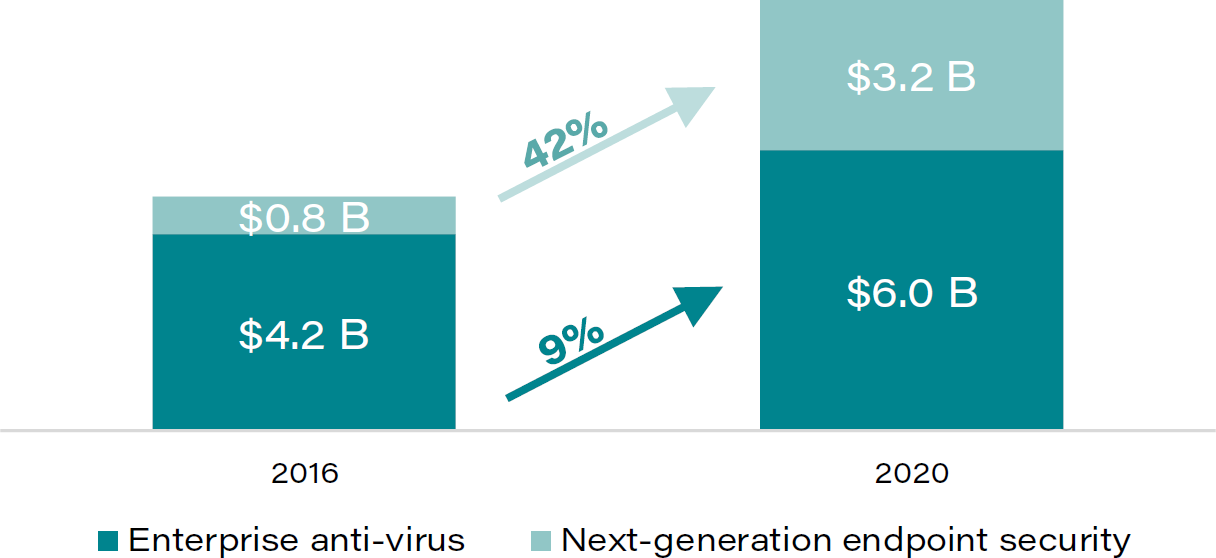
This translates into a pretty attractive market. EMA research pegs the 2016, roughly $800MM next-gen endpoint security market growing to $3B-plus by 2020—an implied 42% CAGR.
Thus, there are at least pockets of endpoint security urgency, and we think there’s underlying recognition that something about endpoint risk exposure must be done. However, we think to a greater degree than its predecessor, first-generation endpoint era, there is significant confusion about the right answer to address the need.
A battle to define the market, and other adoption hurdles. Because there are different endpoint security approaches (discussed in this report), we and market experts with whom we speak observe a palpable battle among players to define next-gen endpoint protection. This alone serves as an adoption hurdle.
Related and other hurdles include:
- Solution education efforts remain paramount to guide prospects. While we observe generally growing interest in next-gen solutions/technology, there’s significant need for education about the somewhat ill-defined solution landscape.
- Threat landscape poses another education problem: threat knowledge. Coupled with notable solution understanding holes is the fact that many would-be next-gen endpoint buyers rather surprisingly don’t seem to well understand advanced threats – a key component driving necessity for a new breed of solutions.
- A management and performance snag: Agent overload spurs need for endpoint agent consolidation. A recurring theme in our conversation is agent-fatigue (too many distinct agents deployed per endpoint), which can cause both endpoint management and endpoint-performance-related productivity issues. To alleviate this, we think the market is moving toward convergence of endpoint-security functions, a trend that would benefit vendors/partners capable of subsuming functionality of at least a few existing endpoint agents (we think ultimately two or three agents will perform all endpoint agent functionality). However, lack of execution clarity in achieving this broad desire plays havoc with next-gen endpoint adoption.
Market breakout timing tough to assess, see catalyst resting in fair part on products achieving regulatory certification as an antivirus substitute. Certainly, greater enterprise confidence in the functionality, usability, and manageability of next-gen tools (including sometimes burdensome implementation) should naturally facilitate broader next-gen adoption. However, we see market traction notably determined by the speed at which antivirus-tied budget is freed up at organizations (antivirus may continue to exist as a free or more affordable good-enough version).
A key catalyst for tapping into existing antivirus budgets is next-gen players obtaining regulatory certification for their products (compliant with industry regulations such as HIPPA, PCI, etc.). The key is for new solutions to allow organizations to meet or remain compliant with industry regulations. This translates into regulators and auditors certifying new technologies to be a credible antivirus substitute.
We note according to Enterprise Management Associates (EMA) some next-gen players (such as Carbon Black, SentinelOne, and Palo Alto Networks) have attained in various ways antivirus certification (e.g., approved Corporate Endpoint Protection by AV-TEST), which ensures the product meets compliance standards.
The next-generation endpoint security market
Market size: Breaking down the endpoint landscape
Blending several industry forecasts, Table 1 illustrates the size and expected growth paths of three primary endpoint-security segments. Next-generation tools currently represent a minor fraction of the overall endpoint-security space, but are set to significantly expand their market share. Antivirus solutions are expected to remain a dominant tool, projected to grow at a respectable high-single-digit rate. The remainder category includes tangential security software, such as data leak prevention (DLP), host IPS/IDS, anti-spyware, device control, and application control.
TABLE 1: Market size and market growth comparison (anti-virus vs. next-generation)
Source: Enterprise Management Associates, Gartner, ResearchandMarkets, Exclusive Networks Australia.
We note the next-gen market size and growth projection is entirely incremental to the existing endpoint-security landscape. Depending on the pace of antivirus-dollar reallocation toward next-gen solutions, we expect the next-gen market could grow even faster by taking greater antivirus share.
Thinking ahead by looking back: First-gen endpoint market (antivirus) offers useful perspective on potential next-gen evolution
We find it somewhat instructive to look at the first generation of endpoint-security companies, which sprang up largely between the mid-eighties and the turn of the century (MSFT is an outlier). Most of these older-generation vendors currently deliver some capabilities beyond basic, pattern-based antivirus. We observe two dynamics:
A fair degree of staying power: Three-fourths still exist. Fully 19 of 24 first-generation endpoint companies (founded in years up to and including 2001), or about three-fourths of them, still exist today as independently operating companies. (The timeline may suffer from moderate survivorship bias.)
Two primary company tiers. Among these 24 players, 1) a top tier of five antivirus leaders/consolidators formed (McAfee, Symantec, Sophos, TrendMicro, and Kaspersky Labs), while 2) a second tier of less than a dozen smaller players with mixed enterprise and down-market focus emerged, such as AVG, Kaspersky Lab, Bitdefender, ESET, F-Secure, GFI, Panda Security, and Webroot. The balance (perhaps a third tier) of players haven’t been particularly meaningful survivors.
Implications for current generation vendor landscape:
(1) Number of players expected to thin at least somewhat. It’s tough to generalize about buying behavior for next-gen solutions. It only makes sense that the crowded market of at least about 25 players should shrink somewhat. Lacking critical mass due to mixed demand, some smaller players will likely face a cash crunch, pushing them out of operation or into the arms of larger, cash-richer peers. One recent indication is the acquisition of Confer Technologies by Carbon Black.
On the other hand, given the early days of the next-gen endpoint market, some enterprises may initially experiment with a variety of new innovations. For example, a worldwide sales head of a prominent next-gen endpoint-security vendor notes enterprises are somewhat often layering multiple EDR solutions in addition to or as a replacement to existing antivirus agents. We think this indicates there’s a search to find what’s best.
(2) A few larger winners likely to emerge. It is not unthinkable for the current-generation endpoint industry to morph into a similar, more concentrated structure, similar to how the first generation evolved. This would feature a handful of dominant endpoint-security vendors and a greater number of smaller companies.
A couple supporting, similar drivers for this likely move toward greater consolidation and concentration include
From a CIO or IT admin perspective: Customers yearning for simplification, consolidation for easier management. A well-known security challenge is the abundance of unintegrated existing endpoint agents and related management snarl. While certainly more than a handful solutions may viably compete to be among a couple or so endpoint-security installation, it’s hard to conceive this desire to do more with less would help sustain the current array of alternatives.
From an end-user perspective: Expect endpoint-agent reduction to improve endpoint performance, productivity. Specifically, customers look to alleviate performance pains and related productivity constraints by opting for a limited number of agents. One knowledgeable contact suggested there would likely be two to three core components (security, management, and DLP) as part of future endpoint-security deployments. Supporting this idea, other voices speak of “agent fatigue,” referring to the multiple agent-based solutions installed on endpoints (relating to AV, host IP, compliance, etc.).
FireEye, Palo Alto Networks: Takeaways for higher-profile public players.
While there are about two dozen private players vying for greater prominence, larger public companies, such as PANW and FEYE, have entered the field relatively recently as well.
FEYE HX: Endpoint to some extent a potential source of helping overall business momentum. FEYE’s HX appliance is proven to work successfully with Mandiant to find infiltrations post-breach, and it may be a robust product. It’s an important component of relatively successful FireEye-as-a-Service. For better or worse, to work well, HX really requires running either the core NX offering, FX (files), or EX (email). From a cost and management perspective, the offering seems moderately complicated, but we’ve not heard this to be a particular drawback. We think the company’s endpoint offering is a top endpoint-detection-and-response solution, and we are encouraged it’s being enhanced with exploit detection and prevention capabilities.
PANW: Competitive endpoint offering tied to firewall platform, prevention story. Traditionally network-security focused, we believe PANW has a soundly articulated endpoint security proposition tied to its firewall-centered platform. While it is still early days for its prevention-based Traps subscription solution, management is confident it could see a similar adoption pattern as its firewall (slow start to then accelerate). We consider it a promising source of revenue upside; despite mixed feedback, we believe the product’s integration with the rest of the platform (specifically, cloud threat-intelligence system WildFire) and further product tuning should make it an appealing option.
TABLE 2: Endpoint security vendor timeline, first-and next-generation
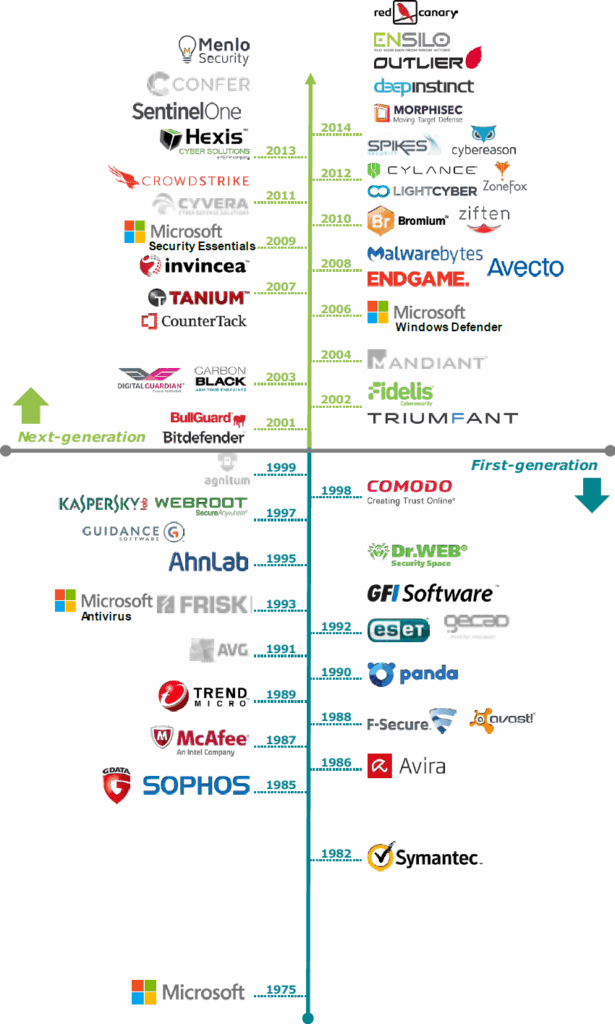
Source: First Analysis.
Notes: Blue dates indicate first-generation; green dates indicate next-generation; logos in gray indicate the company no longer operates independently.
The next-gen landscape: what’s going on?
See two high-level approaches emerging
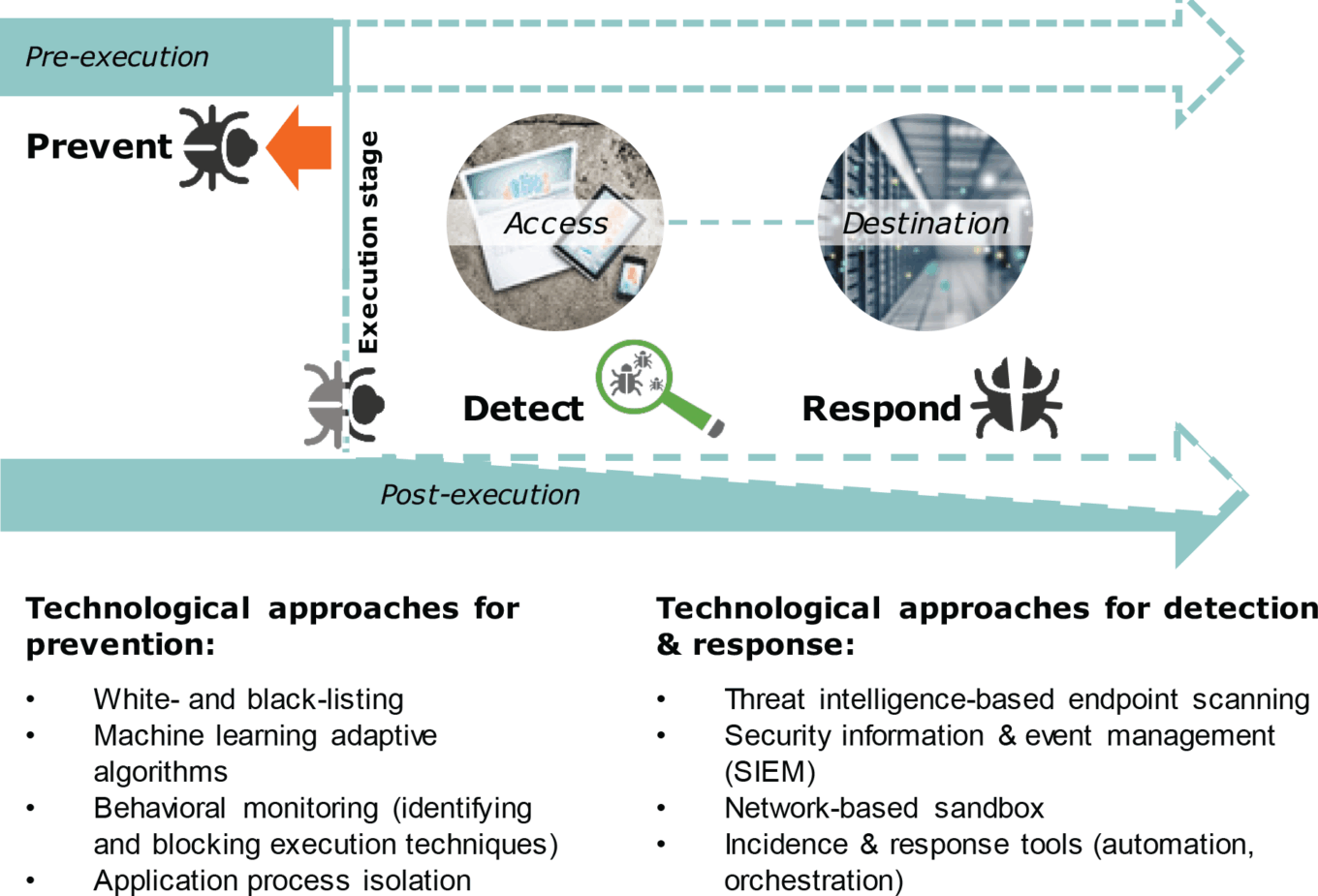
The revitalizing endpoint-security space is surely complex, rife with technical jargon and vendor promises. While the core distinguishing feature of “next-gen” is the lack of signature- or hash key-based detection mechanisms typical of antivirus (hash keys are text strings transformed into numbers), at the highest level, we see two main security philosophies (prevention and detection-plus-response) taking center stage. Both are designed to allow for a more proactive security posture, either via 1) outright prevention or 2) active threat hunting.
TABLE 3: Next-generation endpoint protection: prevention vs. detection response
Source: First Analysis.
Prevention to avoid damage: Pre-compromise interception. While we have not come across a vendor claiming 100% prevention is attainable, some explicitly aim to achieve a high attack-interception level before threats can successfully execute on the endpoint. Technologies include 1) whitelisting (allow only authorized applications and processes) and blacklisting (block unauthorized applications and processes) to reduce the attack surface, 2) application exploit prevention (enable only normal, safe application execution), and 3) various technique-, emulation-, or algorithm-based blocking methods, often enriched by proprietary or crowd-sourced threat intelligence. Some degree of response capability (if only through an alert mechanism) may be included.
Detection to limit damage: During/post-compromise detection and remediation. Termed ‘endpoint detection and response,’ or ‘EDR’ by Gartner, this centers on endpoint-activity monitoring or scanning to 1) rapidly identify security breaches (“hunt”), usually through behavioral-anomaly detection, and 2) enable faster response (more effective containment or remediation).
Some describe EDR as a DVR for the endpoint, data from which is dumped into a database for analysis. More technically, detecting compromised endpoints via a behavioral method is usually performed by looking for indicators of compromise using threat-intelligence (generated by a network-level sandbox detection engine for example) and log data from the network, operating system, and applications. As a result, EDR generally requires collecting or correlating large amounts of data to find the needle in the haystack, which may be an analytical and financial burden. EDR solutions often include forensic investigation and reporting capabilities that leverage the recorded endpoint-activity data for post-breach analysis purposes.
Blended and/or other technology approach. While the prevention-detection paradigm seems to us a recurring and sensible technological distinction, we recognize some companies look to either 1) blend both approaches as part of their value proposition and/or 2) incorporate other technologies into their product, such as data loss protection, data encryption, application control, vulnerability scanning, endpoint IPS, personal firewall, and mobile security.
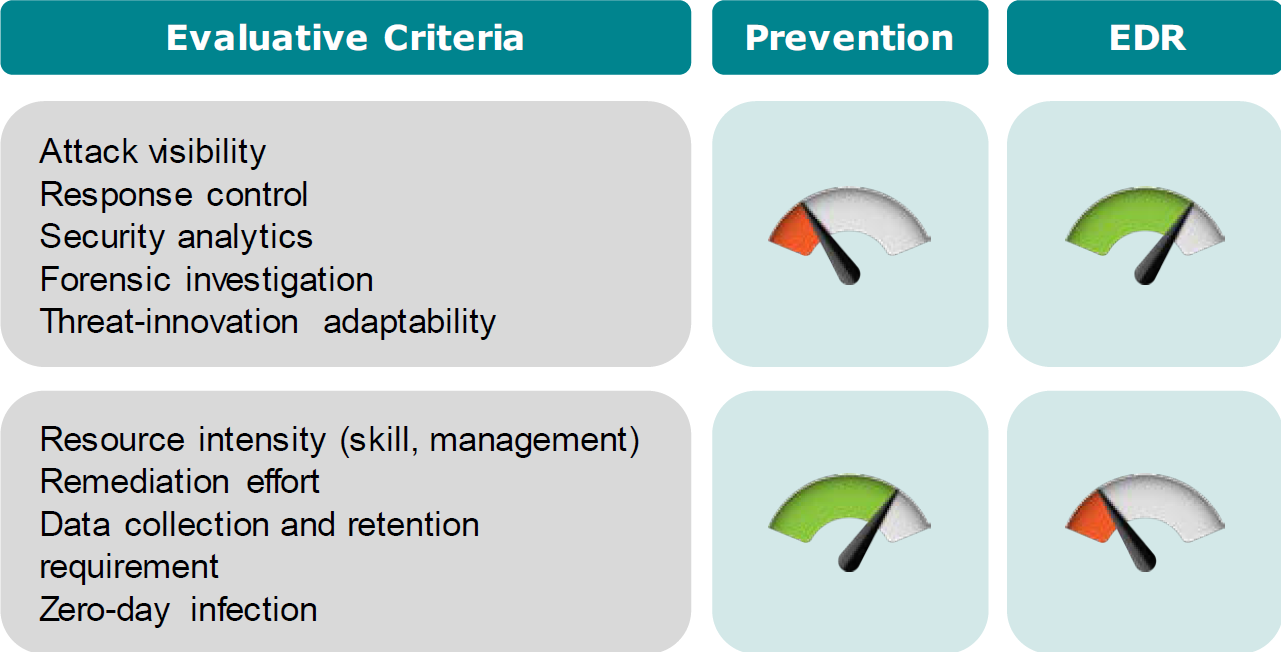
Assessing the two principal functional approaches
Below we sketch our assessment of the prevention and detection/response approaches. We summarize their relative strengths and weaknesses in Table 4.
Prevention perhaps popular, but under-represented; delivers cost-savings value. While there are many more next-gen EDR endpoint solutions on the market, we’re rather surprised to see recent Enterprise Strategy Group research indicating most enterprises consider prevention, while “massive” enterprises evaluate and deploy EDR solution. This is understandable given their larger security teams and greater resources. Prevention is perhaps generally a more technically sophisticated approach, which may partly explain why there are fewer players.
We think the market’s prevention interest is understandable since an effective prevention solution addresses at least a few key security management pains, especially for organizations that are particularly resource-constrained. These include 1) lower resource requirements for alert management and response efforts – attractive in the context of ongoing security-skill shortage. Also, 2) data-storage related costs and overhead would be lower.
EDR appealing to resource-rich companies, delivers context, visibility antivirus can’t. On the other hand, EDR provides valuable investigation capabilities around breaches, addressing a key antivirus visibility problem: Antivirus delivers no context about penetrations, and it doesn’t know what it didn’t catch. EDR also helps often complex forensic analysis and speeds up the remediation process if a breach occurs. Threat responders also usually retain more manual control regarding how and when to intervene, including the ability to mitigate or remediate threats (saving hours of time rebuilding or re-imaging endpoint systems). We think such benefits should be appealing to organizations possessing larger, dedicated staff with in-house security skills and experience.
TABLE 4: Gauging the virtues of prevention versus EDR approaches
Source: First Analysis.
High-level player overview: Leaders and followers
We’ve noted that as an important security segment, next-gen endpoint security features a substantial number of players. We depict these vendors in Table 5. Most of the next-gen ‘leaders’ we identify are pure-plays; a few deliver next-gen endpoint solutions as an adjunct to their core biz. The ‘followers’ we identify are mainly first-gen endpoint vendors striving to morph in some fashion into delivering next-gen solutions.
TABLE 5: Endpoint security matrix
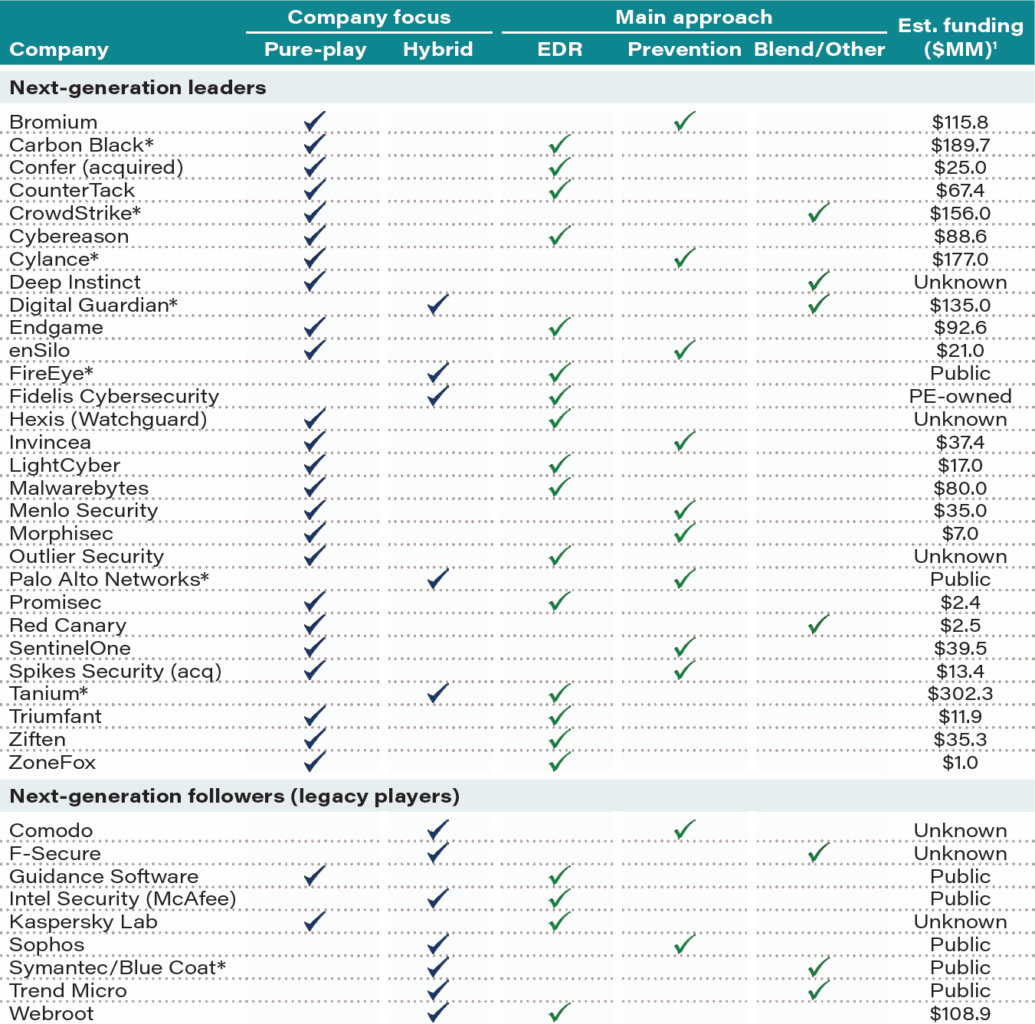
Source: Company reports and websites, various third-party publications, First Analysis.
Notes: *Companies profiled in this report. (1) Funding reflects total company funding, whether hybrid or pure-play.
EDR players dominate the field, see potential for integrated prevention-plus-EDR solutions. We estimate not more than a third of next-gen solutions focus explicitly on prevention. We think this is largely due to the greater technological sophistication necessary to deliver preventive technology. While next-gen offerings are mainly centered on one the two general approaches, solutions may evolve to feature integrated endpoint-security suites encompassing both prevention and detection technologies (an early indicator of this trend is the recent Confer acquisition by Carbon Black, Cylance).
Demand dynamics. Mainly deliberate decision-making, uncertainty about right solution. Despite growing next-gen endpoint need and receptivity, there’s palpable hesitation about which solution/technology either 1) best fits the customer’s environment and/or 2) best addresses the aforementioned security challenges. This is typical: Security buyers tend to be methodical (unless an organization is disrupted by a major, headline-making breach).
Product evaluations unquestionably play a substantial role as part of the endpoint-product sales initiative, but in general, we believe the buying motion is only in its first or second gear as budgets tend to be organized around gradual purchases and tech replacements. An industry contact relates that while organizations are frustrated with antivirus and seek an alternative, due diligence processes can be lengthy, particularly at a time when more organizations tend to shy away from too many security layers (including endpoint agents).
What’s driving new endpoint security solutions?
We see transition to newer, next-generation solutions as driven particularly by 1) elusive advanced malware and exploits, 2) traditional endpoint-technology failures (antivirus), 3) challenges associated with a growing and more diverse attack-surface (more connected endpoint devices, new types/versions of connected devices), and 4) second line of defense beyond network-security measures. We flesh out these drivers below.
TABLE 6: Traditional antivirus strengths and weaknesses
Source: First Analysis.
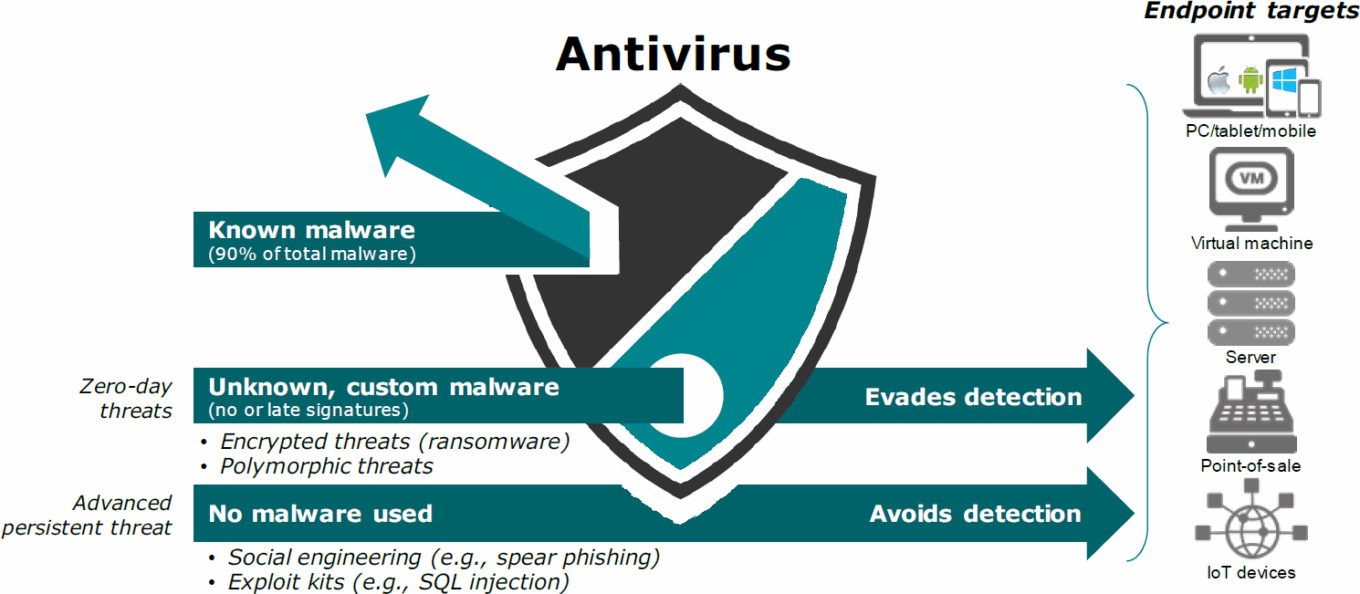
Key driver: Tough-to-catch advanced malware and exploits . . .
A recurring security headache in the last few years is the growing and hard-to-stop preponderance of sophisticated, targeted, and never-before-seen ‘zero-day’ attacks. This includes the important ‘Advanced Persistent Threat,’ or APT category.
An increasing volume of sophisticated and unknown threats employ advanced techniques to disguise malware (easily alter its malicious code to bypass detection), and thus are tougher to detect by network and traditional endpoint security controls. Fast-innovating attackers seek entry points through increasingly sophisticated means, such as script-based attacks (web-based attack using scripting language, instead of conventional malicious code, to exploit vulnerabilities). Socially engineered spear-phishing is also a major infiltration means.
A growing challenge: Encryption. Recent dialogue we’ve had with industry participants repeatedly points to expanding use of encrypted threats to evade detection (uses SSL protocols). While some network-security devices include SSL decryption capabilities (such as FEYE and PANW), they generally don’t seem to be well-equipped to always inspect encrypted traffic, rendering the perimeter wall less useful. While malware seeks to travel incognito through the firewall to reach its destination, it has to reveal itself (decrypt) to execute on the target device. The endpoint therefore is becoming a prime location to discover encryption threats.
…renders antivirus increasingly ineffective due to changing threat landscape.
On the market for about three decades, traditional antivirus (AV) scans files for malicious content using existing digital signatures. Despite its continued endpoint dominance, AV’s effectiveness has been problematic for a while (discussed below).
Antivirus stickiness driven by compliance, basic protection… Antivirus retains an overwhelming endpoint presence due to 1) compliance reasons (such as the antivirus functionality embedded in PCI-DSS and HIPAA requirements), 2) switching costs, and also because 3) it is generally still fairly effective to block mainstream, run-of-the-mill malware.
For instance, according to recent AV-test. org results, “Microsoft does a very good job catching the most widespread and prevalent malware,” and most top-tier AV solutions seem to catch nearly 100% of well-known malware while maintaining at least reasonable false-positive rates. Continuously evolving heuristic techniques for recognizing suspicious behaviors substantially contribute to making anti-malware technology more effective.
…even so, waning effectiveness continues. Despite this, antivirus remains a signature-based technology that no longer adequately addresses malware that rapidly changes (“polymorphic”) or is automatically generated (such as “spray and pray” attacks) and vulnerability exploits. While antivirus packages may feature some advanced capabilities (not always used or well-known), they tend to be particularly ineffective at stopping a smaller volume of critical, but potentially more damaging advanced and zero-day malware (accounts for roughly 5% to 10% of all threats).
Antivirus is challenged because it 1) focuses mostly on pre-identified threats or aims to find new threats through heuristic analysis, a technique which identifies common patterns of known code, structures, and attributes (and subsequently generates a remediating signature), 2) doesn’t update digital signatures frequently enough to quickly identify new malware and to stay ahead of the attack, and 3) may not have sufficient forensic capability (root cause analysis) to enable post breach, insight-generating investigations to try to prevent similar breaches from recurring.
AV disappearance conceivable. Although antivirus as a category may continue to exist for a while, we expect its technology to either 1) become subsumed into a new generation of endpoint security products or 2) be developed into a more robust technology by adding greater capabilities. On this latter point, to the extent legacy players are successful in credibly advancing their technology and executing within their large installed bases, they could pose a considerable competitive threat to the host of mostly private, less resource-rich next-gen vendors.
Growing attack surface (endpoint sprawl, diversity) complicates network security.
Historically, corporate data assets were protected within the data center, which made it easier to guard the perimeter and to manage access from known locations or devices. The increasing number and variety of endpoints is expanding the corporate perimeter, complicating the network’s security and making it even more vulnerable.
Confluence of endpoint developments… Securing the network is becoming more complex due to 1) a growing number of untethered devices accessing open, unprotected networks (for both professional and personal purposes, such as using a hotel wifi without VPN), 2) a variety of computers running numerous operating systems (which may be virtualized), 3) bring-your-own-device policies (generating more vulnerabilities due to harder-to-control personal-app and internet-data usage), and 4) newer types of internet-connected endpoints used as a conduit to carry out attacks, such as point-of-sale systems, which often house older, unpatched operating systems.
…results in larger attack surface, tougher security challenges. The greater number and diversity of endpoints (not necessarily situated behind the relative safety of the firewall at all times) increases breach opportunities. Since this sprawling endpoint posture is targeted by hackers looking for the weakest link to try to infiltrate the network, it increases the malware-attack volume and the number of exploitable vulnerabilities. Since a sprawling endpoint infrastructure requires security of multiple platforms and devices, it spurs interest in faster-to-scale and easier-to-manage solutions.
The opportunity to address these pain points has spurred private-company innovation (and instances of unicorn-level funding) and spurred existing, often originally network-focused vendors to adopt, acquire, and/or integrate their own endpoint-security offerings.
Who is focusing on the endpoint opportunity?
We think some experts rightly assess the next-gen endpoint opportunity as approached by a somewhat broad mix of newer and legacy players. In Table 7, we identify principal groups and respective players focused in some degree on the endpoint security opportunity.
TABLE 7: Three buckets of industry players vying for next-generation opportunity
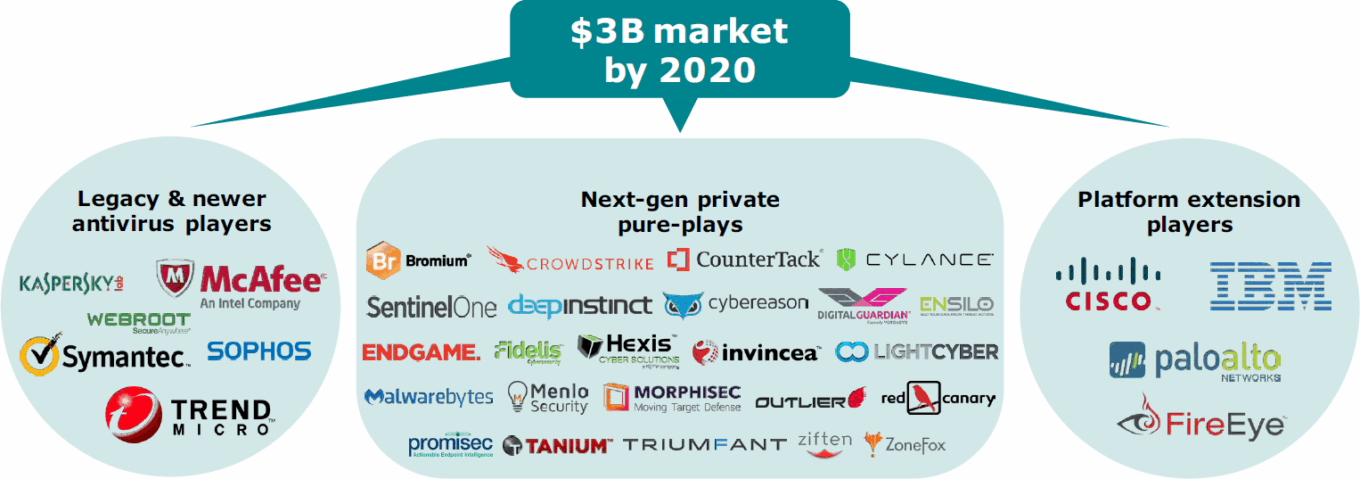
Source: First Analysis.
Endpoint-security primer: what is it and why does it matter?
We briefly outline what constitutes an endpoint, why endpoint security matters, and how it contrasts with network security.
Endpoints: User-accessed, Internet-connected devices. For security purposes, endpoints refer to internet-connected devices (linked to a TCP/IP-enabled wide area network [WAN]) through which users access corporate email, applications, and data, but also the web and various cloud services. Residing at the network edge or outside the corporate periphery, endpoints traditionally include OS-enabled systems, such as desktops, laptops, handheld devices, servers (if they connect to an outside network), and non-traditional devices, such as point-of-sale terminals, industrial control systems, ATMs, and even wearables.
Network control a critical element in security posture . . . Network security aims to protect an organization’s endpoints (constituting the network) by routing all in- and outgoing traffic through a central security device (most notably via a firewall). Such network control provides various centralized security functions, such as threat protection, network access control, authentication, policy enforcement, secure connectivity, and vulnerability assessment and monitoring.
. . . but not a panacea against all threats. Network defenses will remain a critical security layer, but it has weaknesses. While network-level protection may block threats before they land on endpoints (thus posing a preventive threat barrier), without separate endpoint-security controls, all security eggs are put in the network basket (a single point of failure). Moreover, given the multiple security functions, network controls tend to 1) create focus-numbing alert noise (needle- in-the-haystack problem), and 2) suffer from a security-vs.-usability trade-off, meaning the performance and time required to conduct threat inspection may impose a bottleneck problem, reducing usability (user speed and productivity). As a result, a network-only security approach can leave holes causing some attacks to slip through network defenses and spread to endpoints and/or the data center (where valuable data resides).
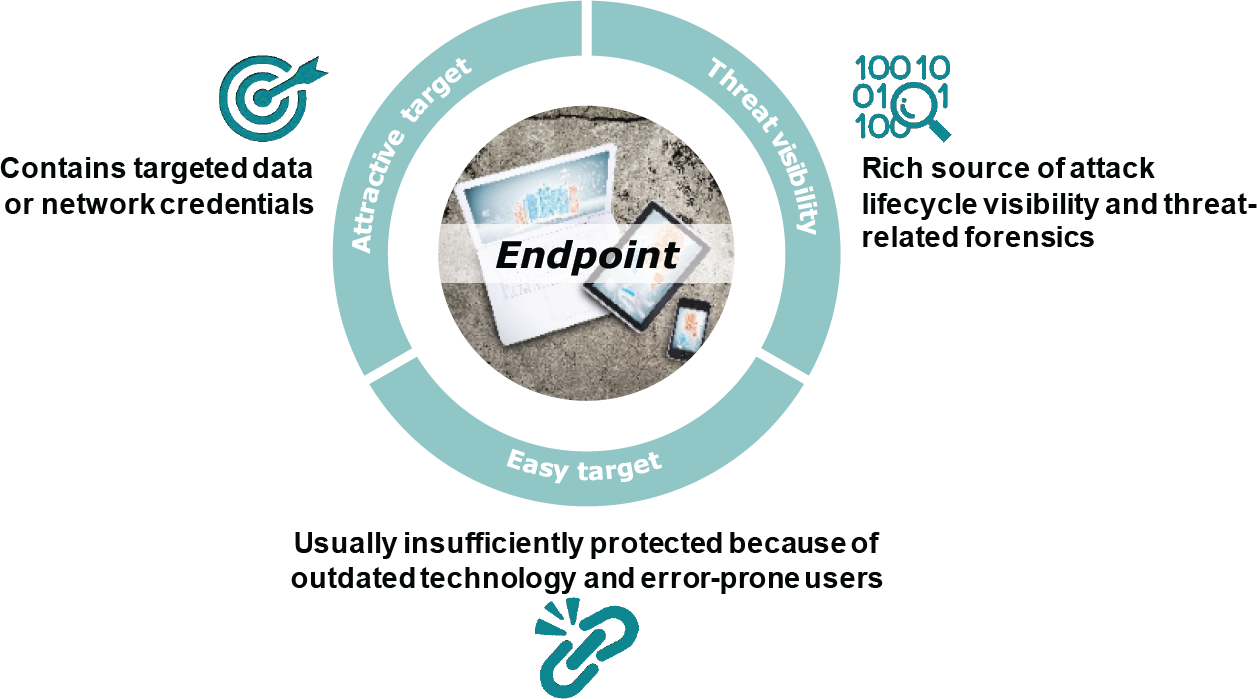
Endpoint security a necessary layer. To well secure an organization’s network, focusing on securing endpoints themselves remains important, and we think increasingly so, for the following reasons:
Endpoints represent attractive target for network, data access. Endpoints are an attractive prey; they contain high-value data and network login or access credentials to get a deeper foot in an organization’s door. Attackers try to exploit any security weakness on endpoints to get access to targeted data (on the endpoint itself) or by escalating privileges once it lands on an endpoint (use the endpoint as a conduit to get to the data center). Local endpoint-security controls are therefore critical; they can either prevent an endpoint breach or detect it early to limit damage.
Porous endpoints continue to pose risk to network safety. Endpoints tend to be poorly protected due to 1) only moderately effective antivirus solutions, 2) error-prone users (credulously providing log-in credentials for instance), and 3) insufficient endpoint-security “hygiene.” A major source of network vulnerability, hygiene concerns refer to unpatched software vulnerabilities and insecure configurations (such as keeping unnecessary application services active). According to a recent study commissioned by NASDAQ and Tanium, nearly 90% of 1,530 respondents don’t consider their malware, antivirus, and patch software to be up to date 100% of the time. Such ill-secured endpoints may require less sophisticated attacks to successfully gain network entry, which is particularly worrisome given endpoint-targeting adversaries sometimes use automated efforts to find endpoint-security holes. By also applying protection directly on endpoints, threats can be prevented from getting inside the network more effectively.
Connecting the dots: visibility, control, and confirmation. Using endpoint protection in addition to perimeter security results in greater visibility and control over threats inside the network (in real time and for historical analysis). While network-based defenses may fire alerts when malware crosses the perimeter, endpoint security measures are deployed on every device. It thus may eliminate blind spots (not having a security agent on a mobile phone for example) and more readily scope actual threats (which endpoints are compromised, whether malware executed, and what other files or processes may be affected). Endpoints contain much of the intelligence necessary to connect malicious-activity patterns and show which attacks pose the most acute danger (prioritize breach response). This facilitates a more efficient response by either thwarting a breach or adjusting the security stance to avert future attacks.
TABLE 8: Why the endpoint is an attractive target
Source: First Analysis.
In the following section, we discuss a selection of some of the (in our view) most prominent representatives of the prevention and EDR approaches: 1) key public security players FEYE and PANW, and 2) a few private vendors.
Company profiles

Carbon Black: Powerhouse EDR play via continuous endpoint monitoring
Reportedly filed confidentially to come public, Waltham, Mass.-based Carbon Black (a newer name, as Bit9 acquired Carbon Black in early 2014) has about 2,000 customers, including about one-fourth of the Fortune 100. It is seen perhaps most frequently by peers with whom we spoke.
Carbon Black’s endpoint security offering was recently restructured in the wake of the Confer acquisition, now combining application control (originally Bit9), EDR (Carbon Black), and next-gen antivirus (originally Confer). Its EDR solution Cb Response uses advanced-detection technology under the premise that 1) not every threat can be detected ahead of time, and 2) endpoint activity is assumed suspicious unless confirmed otherwise. Therefore, endpoint activity is recorded constantly for instant, anytime examination.
Carbon Black: core EDR platform built on continuous endpoint monitoring. Carbon Black is essentially an EDR tool that seeks to make threats easier to detect and faster to contain through continuous endpoint visibility (kill-chain lens). Via a kernel-based agent (<1% CPU) Carbon Black’s technology 1) continuously records all endpoint activity (vs. reactive scans) to look in real time for malicious digital traces, such as binaries, network connectivity, file activity, and configuration changes, then 2) discerns event relationships among the data and correlates it with various intelligence sources using open APIs (malicious-behavior indicators, threat intelligence, and code) to find anomalous attack patterns, and finally 3) responds, via rapid containment and remediation actions and suspicious-activity watchlists.
- Mostly on-prem, local-storage-based solution. While a hosted version exists for up to 40K nodes, the Enterprise-Response product is essentially an on-premises solution. It aggregates endpoint data on local servers (cached in memory when devices are offline), obviating the need to actively scan the endpoint environment.
- Retrospective capability well-suited for incident-response efforts. Given the threat-data retention and access (including relevant breach information), Carbon Black looks particularly useful for providing incident-response-facilitating forensic insight (“rolling back the tape”) and threat attribution. This should help root cause analyses (how the attack entered and where it went) and hence faster, more targeted response (isolating threats, terminating processes, and/or remediating endpoints).
We estimate around 45% of the installed base (800 to 1,000 customers) uses Carbon Black.
Recent addition Confer adds ‘next-gen AV’. Brought on board via the July 2016 acquisition of Confer, re-branded Cb Defense provides a prevention-oriented technology, including 1) a cloud-based platform that digests endpoint IOCs and indicators of attack (IOAs) for further analysis (such as behavioral analysis, reputation assessment, and file inspection), and 2) search and reporting capabilities for contextual threat insights.
Default-deny whitelisting (Bit9) as prevention layer. Now called Cb Protection, Bit9’s whitelisting functionality (allows only “known-good” software to run) is currently delivered through Enterprise-Protection product, including customizable protection and compliance policies.
Regularly-surfacing vendor; some likely competitive challenges. Our conversations with industry observers indicate Carbon Black is a respectable competitor, but we also hear of some drawbacks, such as the understandable scalability challenges likely to occur with predominantly on-premise deployments (relative to cloud-powered alternatives).

CrowdStrike: Aiming for a combined prevention and detection approach via SaaS model
CrowdStrike seeks to differentiate by combining various protection elements into one comprehensive solution. This includes 1) more conventional EDR (IOC-scanning) and exploit mitigation, but importantly also 2) its proprietary, proactively geared “indicators of attack.” Through a holistic-functionality choice, the company seeks to address the full attack spectrum (known and unknown threats, malware and non-malware). Since only about 40% of breaches are malware-related, CrowdStrike considers it paramount to have a complete defense posture that avoids “unknown failure” through both prevention and detection.
Key tech, Part I: Behavior-based indicators of attack (IOAs). While CrowdStrike also performs more traditional security functions (IOC-based detection, black- and white-listing) to uncover malicious files and block exploits, the technology particular to the company – its IOAs – preventively catch unfolding attacks (whether malware is used or other means). IOAs constitute a preventive, adaptable mechanism to look for warning signs (suspicious activity such as code execution, command & control, and lateral movement) of an impending attack. Reminiscent of Traps’ mitigation approach technique, IOAs aim to expose the sequence of steps (attack behavior) that must be executed for an adversary to succeed. These specific indicators are derived through behavioral, machine-learning-based analysis (rules are updated in real time using a cloud model) of continuously recorded endpoint data. Since behaviors are continuously monitored as they execute, the technology delivers continuous visibility and a level of forensic insight (how attackers entered, what was accessed, and where else it moved).
Key tech, Part II: Threat Graph. Unique to CrowdStrike is its cloud-based threat-analysis-and-intelligence database Threat Graph. It is a visual interface that scrutinizes and displays endpoint activity from across the customer base (every customer is securely cloud-connected). The storage scale and computing power of the cloud model facilitate fast malicious-behavior detection using IOAs (irrespective of whether it involves malware).
Cloud model offers various management, security benefits. CrowdStrike’s cloud detection engine can be deployed relatively rapidly (fast time-to-value) across 100K-plus endpoints. It is easy to scale and suitable to protect mobile devices (security travels with the device). The company’s cloud architecture is inherently always on and up-to-date. This mutes the danger of fast-changing attack methods and allows for a continuous-protection stance. An in-house analyst team (intelligence expertise, threat-hunting, and incident response services) can readily access threat information and prioritize alerts to speed up incident response. We think the company’s cloud strategy and prevention mindset should adequately address management and cost overhead.
- Brief product suite overview. CrowdStrike’s offerings consist of the 1) Falcon platform, including cloud-based Host (endpoint sensor), Overwatch (managed security), Intelligence (threat-intelligence subscription), and DNS (DNS blocking), and 2) a series of incident response and proactive security consulting services.
Positioning, ongoing evangelization challenge, down-market intentions. While CrowdStrike’s secret sauce is its IOA technology, sales have been largely driven by its EDR capabilities. Though the company does expect to see greater appreciation for its IOA approach kicking in this year, it looks to better evangelize and market itself. Currently limited to mostly very large enterprise customers, CrowdStrike looks to broaden its mindshare (its roughly $75MM revenue level is similar to Carbon Black’s) and gain a greater number of customers below the top-enterprise segment.
Cylance: Machine-learning for threat prevention
Cylance is among the more prominent vendors to successfully commercialize machine-learning models to enable threat prevention (machine learning continuously watches software operate). The company’s “clean, catch-everything” mission is promising and ambitious. The jury is still out, but we do see in Cylance a prevention-focused player gaining greater mindshare – it is being increasingly seen in product evaluations. The company counts about 1,200 mostly mid-market customers (it is looking to further penetrate the enterprise) and maintains an OEM relationship with Dell for SMBs. Cylance impressively raised $100MM in its most recent capital raise (D round), valuing the company at about $1B.
Prevention through pre-execution technology. Key to Cylance’s technology is the use of “pre-execution” algorithms, which predict if a program is malicious – thus preventing malicious traffic from reaching an endpoint’s memory. These algorithms identify malware even if it has not been seen previously. The company contrasts this to previously discussed approaches, such as signature-based detection (antivirus), exploit detection, behavioral detection, and EDR, which it deems insufficient interventions occurring while or after the malware has executed.
Machine-learning models power preventive capacity. The company applies predictive machine-learning or artificial-intelligence techniques that help generate models of how software should run to identify malicious files or applications. The software models control what can be executed on the endpoint and are updated every six to nine months to maintain computation performance. Claiming a 99% efficacy rate, these algorithms 1) detect malicious content based on file information (hundreds of thousands of file characteristics) instead of the file’s execution, and 2) equally protect against regular and advanced persistent threats (such as zero-days, script-based attacks, and spear phishing).
- Core product features. The company’s main product, CylancePROTECT, features a lightweight agent (30 MB) requiring no updates and no signature database. Optional modules include AppControl (for fixed-function devices, such as ATMs) and exploit prevention. Under the ThreatZERO label, the company also provides a series of services to operationalize the product (deployment, configuration, current-environment analysis).
High prevention rate translates into reduced costs. While the solution’s preventive ability isn’t infallible, the company promotes its cost-neutral nature. Its view is that the detect-and-response paradigm requires an increasingly costly, time-consuming effort to manage and analyze growing volumes of threat data. Given the confidence in its prevention capabilities and ease of use (little IT skill necessary), it looks to deliver 1) incident response and security management cost savings, 2) lower performance overhead, and 3) simplified post-execution analysis due to a narrower threat funnel (fewer alerts requiring a response). Illustratively, a Cylance employee related one of the company’s venture investors decommissioned a competitive deployment when the Cylance product caught threats that had slipped into the network.

Digital Guardian: Securing endpoints via data protection
Originally founded as Verdasys in 2002, Digital Guardian (DG) was largely built on the flagship “Digital Guardian” data loss protection, for which it is still primarily known.
Endpoint-security angle rooted in data-centric approach. The company’s original DLP capabilities (identifying and understanding sensitive data) bolster the threat-protection product by offering data-tied security measures and greater data-driven context. While the goal is to be as preventive as it can via real-time, behavior-based detection, it maintains a see-everything policy (to detect and contain an attack if a breach happens).
DLP vendor incorporates threat protection. Other than DLP (prevents unauthorized data access or transfer via permissions and policies), the company’s modular product portfolio currently also includes 1) application whitelisting (via the May 2015 Savant Protection acquisition), 2) network DLP and cloud DLP (via the October 2015 Code Green acquisition), and most relevant to this report 3) behavior-based advanced threat detection (ATP). The ATP solution was incorporated in early 2015 as part of Digital Guardian 7.0 update, and comes in the form of a license that can be enabled on the same agent providing the DLP functions.
DG for Advanced Threat Protection (ATP): the industry’s data-aware endpoint-security bid. ATP is an EDR solution that detects malicious-activity patterns throughout the attack sequence. It detects malicious intent by performing behavioral analysis on 200+ parameters related to system- and user-activity (such as filesystem, registry, and user activity).
Secret sauce: combine data awareness with behavior-based indicators. DG leverages its data-visibility position (understand what users, apps, and processes can do with data) by applying correlation rules to its dual behavioral-analysis method. This combination of behavioral results and data awareness promises full attack-lifecycle context (which data is targeted and how access is attempted) to 1) identify malicious events and 2) mitigate exposure more quickly and more easily (data-flow knowledge). Since any attack is ultimately about data access, this data context is particularly relevant to address advanced threats (security controls “travel” with the data, protecting endpoints regardless of how the attack is staged) and to prioritize remediation efforts according to how critical the data at risk is.
TABLE 9: Digital Guardian’s EDR – advanced threat protection solution
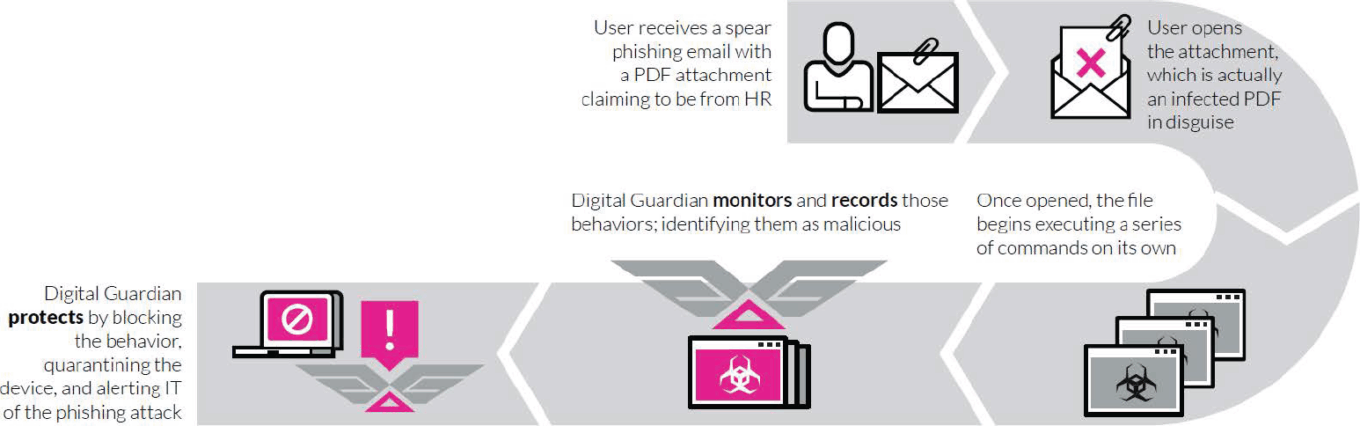
Source: Digital Guardian.
A few other valuable features and benefits. Recently, ATP was included as part of DG’s Managed Security Program featuring an Advanced Threat Analysis Center (ATAC). This service provides access to a threat-hunting team (analysts keeping “eyes on the glass”). By providing threat intelligence and reporting, it addresses skill shortages and advanced-threat management. The product integrates with network-level malware protection (such as FEYE and PANW) and third-party threat feeds. One data-aware, kernel-level agent for both DLP and ATP under a single management console delivers a level of consolidated security functionality. It supports Windows, Mac, Linux, and virtual environments.
MSSP-focused go-to-market; various deployment models. DG for ATP is purposely driven primarily through MSSPs (this channel currently constitutes about 50% of total revenue). Deployments are available in (a hybrid of) on- prem, cloud, and managed-service flavor. Interestingly, we learned about 60% of all Digital Guardian’s deployments are hosted by the company (it is complex for a customer to set up all DLP rules). The company services organizations that have installed up to 300K-plus endpoint agents, which is reflected in an average deal size of about $400K.

FireEye’s HX: A detection & remediation play
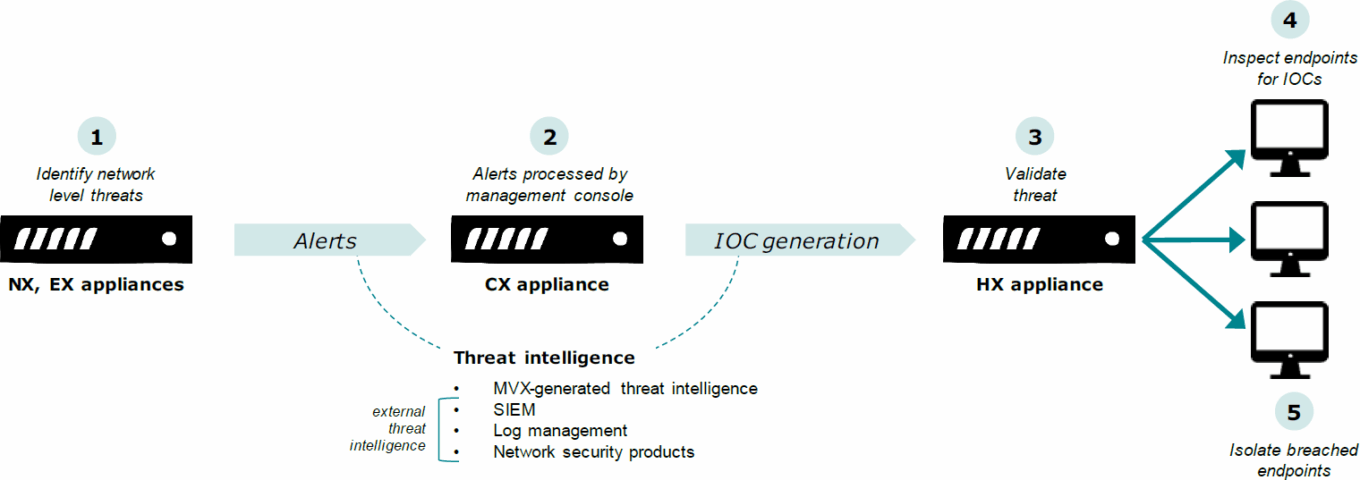
The early-2014 acquisition of incident-response expert Mandiant delivers most of FEYE’s endpoint-tech DNA. Today, FEYE’s endpoint suite consists mainly of the HX appliance, which extends the company’s network-visibility expertise onto the endpoint. A separate Endpoint Forensics (formerly Mandiant Intelligent Response or MIR) appliance is still available for specialized endpoint investigations (we heard most of its functionality was expected to be embedded in HX in H1’16, but this plan may have been delayed or abandoned).
Ideally the dedicated HX appliance is installed in conjunction with the network (and/or email) and management appliances to benefit from threat-intelligence correlation (across core vectors network, email, and endpoint). In this context, we note about one-third of Q2’16 seven-figure deals featured HX as part of such a platform buy.
HX leverages FEYE’s core asset, its highly proprietary threat intelligence, and recently it includes exploit-process detection, which technically makes it in our view a top EDR contender. We believe the potential downside to strong adoption, particularly beyond large enterprises, is the extensive deployment resources and overall cost required.
TABLE 10: FireEye endpoint protection
Source: FireEye.
EDR approach: detect and remediate. FEYE’s security philosophy centers on the idea that breaches are inevitable. The company’s approach involves an EDR-type combination of rapid detection (scanning endpoints for evidence of threats) and swift remediation (when a breach is found). Despite fast detection speeds, the drawback is that it cannot detect malware that hasn’t been seen before in an organization’s network or in an applicable threat-intelligence source.
HX: Threat-intel-based IOC sweeping. As shown in Table 10, in a typical endpoint threat-detection sequence 1) MVX’s premium sandboxing technology (executes suspicious files in a safe, virtual environment) uncovers unknown threats and generates new threat intelligence, which 2) HX uses to find indicators of compromise (IOCs, which we define in the sidebar) to determine whether endpoints are affected. While some automation is available (particularly via the new, separate Invotas workflow tool), FEYE’s approach is to retain most remediation decisions in the hands of security admins.
IOCs: rich, threat-intelligence-based threat descriptions that incorporate logical and/or conditions between traditional signatures, such as file names, registry entries, and running processes. Current IOC standards include STIX, Yara, and OpenIOC.
HX deployment, adoption patterns. Though HX may be deployed stand alone, it is ideally integrated with the company’s network-based products, such as the NX (web) or EX (email) appliance as part of a platform deployment. We note HX is a critical component of the fast-growing FEYE-as-a-Service offering and is easily adopted in the wake of a Mandiant-led breach engagement (resulting in a low or even negative sales cost).
Robust exploit protection plans; other tech down the road. While recently exploit detection was included, exploit prevention is slated for H2’16. In contrast to PANW technique-mitigation technology, FEYE uses a dynamic-scoring algorithm (applying suspicious-activity scores) to block processes from executing. As an effort to bring the MVX capability directly on the endpoint to deliver real-time malware detection, the Ultravisor project (to develop a full MVX clone for the endpoint) is still under development and expected to come to market in 2017 at the earliest. As expressed by a FEYE contact, two other tech components, blacklisting and analytics, are desirable to further beef up the solution.
Cautious threat-intelligence openness. While it does play nice with some other threat feeds (such as Mandiant-created OpenIOC, STIX, and logs), FEYE’s endpoint product tends to rely primarily on its own threat-intelligence eco-system, such as the network products or intelligence subscriptions DTI and ATI. The company sensibly believes intelligence should be high in value (vetted, actionable) and rich in context (attribution). Ingesting a larger number of intelligence feeds would merely risk generating more and less relevant alerts, which would run counter to alleviating the stress of manual intervention.
Unique forensic-analysis strength. Given the Mandiant pedigree, we are inclined to believe the product is particularly well-suited for speeding up incident response and forensic investigation. In order to discern the gravity of a breach, a security analyst may determine specific context, such as which attack vectors were used, whether the threat spread to other systems, and how long the threat has been present. This is technically supported by visibility-enhancing features such as a forensic data collection and an event-timeline viewer.

Palo Alto Networks: Prevention-focused ‘Traps’
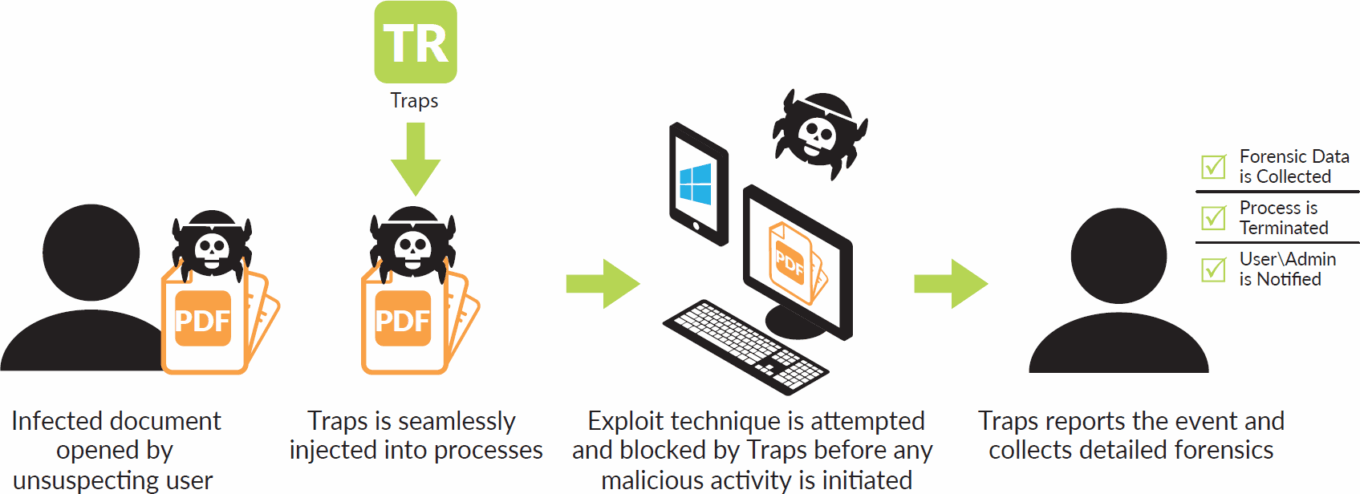
Palo Alto Networks has achieved enviable success with its security platform story, built on its well-received Next-Generation Firewall (NGFW), and a range of both firewall-attached and stand-alone security-functionality subscriptions. One of these stand-alone subscriptions is endpoint-security offering Traps, which solidifies PANW’s platform by adding the key endpoint-protection layer as part of its integrated security proposition.
Traps features technology obtained via the $200M acquisition of Israeli start-up Cyvera that pioneered an approach to interrupting vulnerability exploitations by looking for exploit techniques (before an endpoint attack is fully operational). Deployed at more than 500 customers, Traps is a fast-growing but still minimal revenue contributor (a mid-eight-figure run rate or about 3% of our FY17 revenue estimate).
We think Traps represents an interesting, fairly unique technology that should benefit from the PANW brand and installed base, and also from its recent AV-replacement certification for regulatory compliance purposes from Coalfire Systems (a Qualified Security Assessor). Traps has seen favorable early indicators (decent adoption rate, a recent larger-scale Symantec displacement), while feedback we’ve garnered has been moderately mixed. Our bias is to be optimistic about Traps and PANW’s overall endpoint approach (a potential endpoint functionality consolidator), though PANW’s deliberate, medium-term approach to generating market traction shouldn’t make it an overnight success.
Product strategy: endpoint security as part of critical security infrastructure. Promoting Traps as a platform-enhancing component and an explicit prevention tool, the company looks to turn its endpoint-security element into a longer-lasting and more critical part of a customer’s security infrastructure.
Ambition to break up AV suites; see Traps as core to security posture. PANW doesn’t consider Traps a mere point tool, but rather 1) a key component of at most three endpoint-security tools (along with endpoint management and DLP) and 2) an additional, but integrated element of its three-pronged security platform next to its firewall and cloud-based sandbox. (Traps may be deployed independently of the platform, but it is ideally connected to the platform for intelligence-delivery purposes.) The company hopes to ultimately replace legacy antivirus product suites with its prevention-oriented solution.
Prevention philosophy paramount. Traps’s preventive design approach focuses on 1) blocking malware (malicious executable files) by interrupting malicious processes and behaviors and 2) intercepting exploit execution (vulnerabilities in commonly used files and applications). While it acknowledges it may not be able to deliver bulletproof endpoint protection, the company is confident it can achieve a high level of prevention through this model.
Customers coming around to prevention paradigm. In the last six to 12 months PANW has seen a “healthy change in attitude” toward a prevention mindset and away from detection (due chiefly to alert-volume deluge). Nonetheless, much education in general and for Traps specifically is required.
Gradual, balanced approach toward Traps adoption. PANW takes a long-term view on Traps’ market traction. As a result of the aforementioned company vision to establish endpoint protection as a core part of the security infrastructure and an education-intense prevention philosophy, Traps may see somewhat slower growth than if it were an easier-to-digest, add-on product. The company interestingly expects a similar experience as in the earlier days of its next-generation firewall: It was initially a tougher sell (due to having new technology and being a new company) and slow to find traction, but its firewall has proven to be a market-share-gaining success story. In the meantime, however, PANW’s brand and reputation is an established quantity, which may benefit Traps adoption.
Continue to prove out tech in mostly complementary deployment scenarios. Traps is usually deployed as a complement to existing solutions to prove its incremental endpoint value. In these situations, Traps is expected to take some time and longer evaluation periods before it may entirely subsume existing endpoint-security solutions. Most environments in which Traps is solely deployed today are net-new instances without any next-generation endpoint incumbent. PANW continues to develop the product’s capabilities to ultimately make its replacement potential increasingly credible and plausible. Since the recent v3.4 release, PANW has started to promote Traps more explicitly as an antivirus replacement due to new, antivirus-like features such as local analysis of executables (via WildFire-enabled machine learning) and malicious-file quarantining.
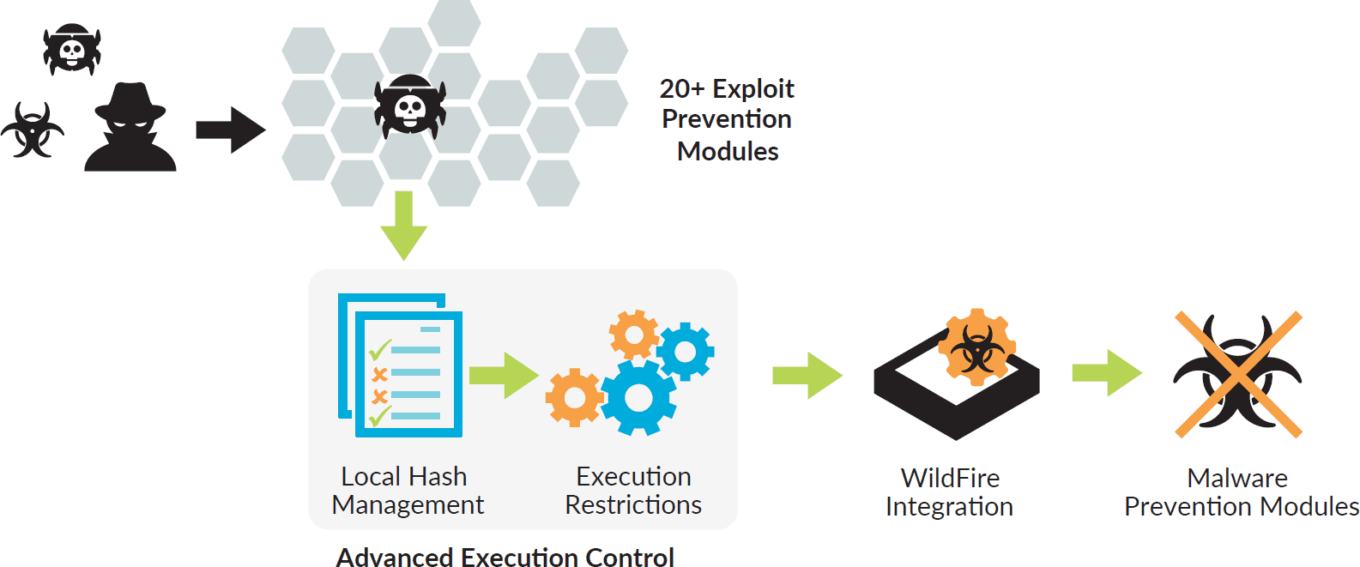
Brief tech review: Traps as part of “kill chain”-based, automated prevention platform. As mentioned, Traps is a key component of PANW’s three-legged, integrated platform components (WildFire threat intelligence cloud, Traps, and the firewall), enabling the company to stop attacks at multiple stages of the kill chain.
Protection against (un)known malware and vulnerability exploits. Traps enables prevention via either a set of prevention modules (for exploits and malware) or sandbox integration with WildFire (for malware only).
Exploit prevention. Default policy rules protect more than 100 common processes in vulnerable, often-used applications (non-default processes may be added). Additionally, Traps detects any of roughly 20-plus techniques (such as memory corruption or logic flaws), of which at least two or three must be used to carry out an exploit.
TABLE 11: Explout prevention – user experience
Source: Palo Alto Networks.
Malware prevention. Traps’s malware-inspection-and-analysis engine seeks to block known and unknown malware, using 1) evaluations of hash-query verdicts (via cache look-ups), and WildFire-enabled suspicious-file execution (provided Traps is integrated with it), 2) pre-set, policy-based execution rules applicable to certain executable files and application behavior, and 3) technique-based mitigation via malware prevention modules (to prevent techniques, such as thread injection).
TABLE 12: Malware prevention
Source: Palo Alto Networks.
Preventive tech renders forensic capability lighter. Forensic content derived from malware-execution processes is limited, but the Traps agent does collect some forensic information. This can be used to identify the cause of an attack, to better understand the nature of the event, and to verify the validity of the preventive measure.

Symantec: Sleepy AV giant seeks next-gen endpoint wake-up
It’s no secret Symantec has been struggling to deliver distinguishing endpoint security product innovation and execution. While the company still boasts a large installed base, its core Endpoint Protection product (including antivirus) is seeing low-single-digit growth. The Veritas sale, the recent Blue Coat acquisition, and another CEO change may put SYMC on a path toward renewed endpoint-security focus and stronger competitiveness, but it’s early to say how successful it will be.
See some preventive capability in mostly antivirus-based Endpoint Protection... Providing some level of threat prevention (mostly for known malware), SYMC’s current Endpoint Protection product incorporates traditional antivirus and a few more advanced technologies (file-reputation analysis, behavior monitoring, advanced-threat scanning).
…and EDR approach in young ATP product. SYMC’s one-year-old Advanced Threat Protection solution addresses advanced persistent threats and includes typical EDR-type functions, such as attack lifecycle visibility, IOC-based endpoint scanning, cloud-based sandboxing, and (rapid) remediation functions. Leveraging the Endpoint Protection agent, modules for endpoint, email, and network are available.
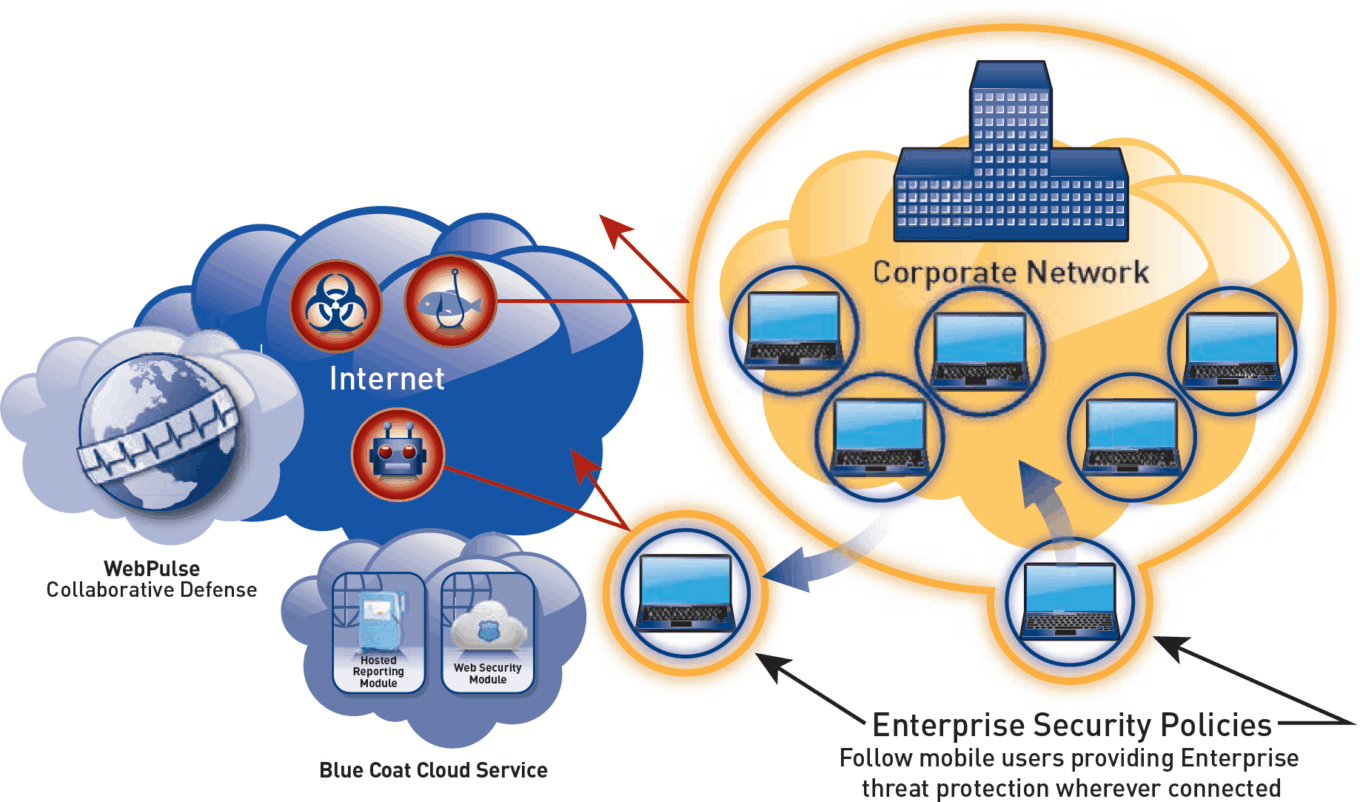
Blue Coat features an interesting approach. In contrast to an endpoint-agent model, Blue Coat uses the cloud to deliver endpoint security against web-born threats. Its employs a ‘web gatekeeper’ (cloud-delivered web security service) to distribute and enforce policy and inspect web traffic for any endpoint device wherever it resides. Cloud-delivered protection includes 1) web filtering (identifies and categorizes, antivirus scanning (anti-malware signature database to prevent malicious files from downloading), 2) encrypted-traffic analysis, and optionally 3) malware analysis (predictive, behavior-based file analysis via sandboxing). This approach may be particularly attractive to protect non-traditional endpoints, such as BYOD and IoT control or “smart” systems, that don’t ordinarily lend themselves to endpoint agents.
TABLE 13: Blue Coat’s cloud-based endpoint security approach
Source: Blue Coat Systems.

Tanium: A detection-as-prevention approach
High-profile, largely high-end private Tanium is garnering considerable interest, amassing about $300MM in venture funding at a whopping $3.5B valuation. According to Forbes, the company delivered bookings of $74MM in 2014, which should have impressively grown to about $200MM in 2015.
Leveraging a novel architecture, the company’s offering was originally designed as a high-powered endpoint management solution sporting various endpoint “hygiene” tools (such as patch and configuration management). While we believe Tanium’s main strength remains endpoint management, we continue to study Tanium’s goal to develop a credible security play. We think only a small number of its customers currently use the solution for security and compliance.
TABLE 14: Traditional hub & spoke architecture versus Tanium’s peer-to-peer architecture
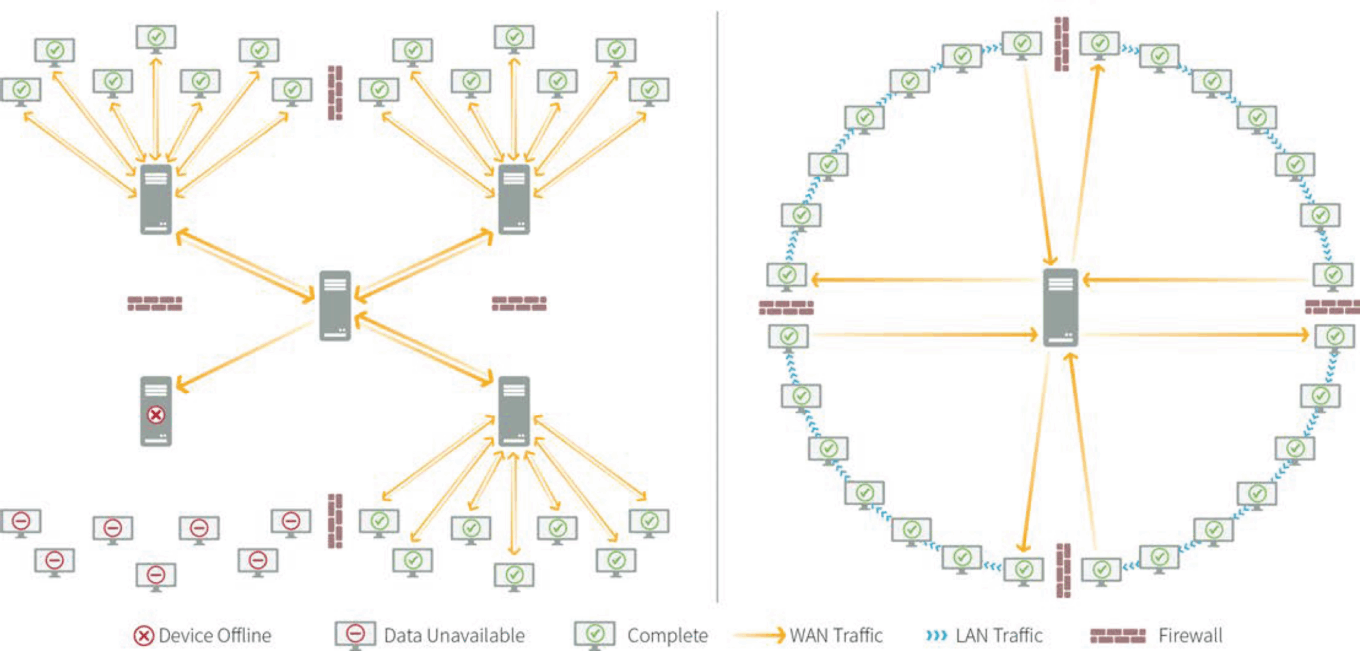
Source: Tanium.
Innovative, distributed architecture underpins platform value. Instead of a traditional hub-and-spoke model as illustrated in the Table 14, Tanium developed a peer-to-peer architecture that connects endpoints to each other in a chain-like fashion over a LAN instead of through various servers over a WAN (which is an intrinsically slower network). Since only a fraction of all deployed endpoints send aggregated endpoint information to the central server (reducing client-server WAN traffic), the architecture promises high processing speeds, great scalability, and better endpoint control. Some feel that the concept of endpoints assuming a server role can cause performance bottlenecks.
Core tech advantage: query-execution speed and scalability. Tanium’s key value proposition centers on executing very fast (the company touts 15 seconds), natural-language-based queries. These queries examine a vast number of endpoints. This methodology speeds up endpoint-management tasks and rapidly remediates endpoint-security vulnerabilities. Potential drawbacks include the possibility of 1) bad or incorrect interventions (such as software patches) that may also be applied quickly and at scale, which means actions should be deployed thoughtfully, and 2) resource-intense queries that may cause availability issues or server exhaustion, which risks service interruption (attention must be paid to the frequency and types of queries).
Query results depend on user input. Output results are determined by the query entered. While a user may not know exactly what he’s looking for, he may find the right answers by iteratively fine-tuning queries. We hear some customers unfortunately struggle to keep up query development to fully leverage the product’s potential.
Query automation supported; manual response. Some degree of query automation is available; queries can be scheduled to run at certain intervals to provide up to a near-real-time view on endpoint changes (every five minutes for instance). While some orchestration is possible, subsequent interventions (such as killing malicious processes) based on query results are not automated.
Query example: For instance, one could enter the query “show all running processes” to retrieve a list of all current processes on all endpoints, indicating vulnerable or malware-associated processes.
Endpoint management: frustrating threats through proper endpoint hygiene. The Tanium offering was originally designed as a high-powered endpoint management solution sporting various endpoint “hygiene” tools (such as patch and configuration management). We understand it is particularly attractive to apply emergency patches.
Agent management: perhaps underappreciated functionality. Our research indicates Tanium may function as a single console for managing other endpoint agents and native Windows controls in particular (such as Windows Defender). Given the many endpoint agents most enterprises still run, this is a potentially valuable feature.
Endpoint security: EDR on steroids key to faster detection and response. Tanium’s inherent capability promotes a more effective endpoint security posture by rapidly detecting and remediating incidents. This should eliminate lengthier endpoint investigations and avoid as much damage as possible.
While Tanium doesn’t advocate prevention per se (viewing it as a false AV-promise related to known threats), we think the company aims to get close via its rapid-detection mechanism. It states the speed factor is particularly critical since 1) damage-related costs increase as the time an incident goes unnoticed lengthens, and 2) threats naturally need to be discovered as quickly as possible to prevent them from spreading further.
IOC-driven detection engine. Using various third-party intelligence sources, Tanium focuses on IOC scanning to capture a possible breach as quickly as possible (and to subsequently patch vulnerabilities or isolate malicious processes). Because Tanium is running on the servers, a user can query and respond (search and remediate) with the same tool to find the needle in the haystack faster (vs. using a separate log management or SIEM solution).
Solid enterprise presence due to large network capability. Since the technology addresses the management pain of large-scale enterprise networks (tens and hundreds of thousands of endpoints) particularly well, Tanium is used in some of the largest organizations (roughly half of the Fortune 100).
Separate buyer profiles likely causing some sales-cycle challenges. Tanium seems to have penetrated its core market relatively well in a fairly short time. Because the platform hosts a variety of modules, we learned, however, that one of its challenges is targeting different IT buyers simultaneously (security tends to be separate buying and decision-making unit vs. device admin and management), potentially slowing down sales cycles.
Feedback all over the map. We’ve heard of satisfied customers successfully deploying Tanium across more than 300,000 endpoints and lauding the fast responsiveness (cutting time-to-fix from 72 hours to under 24 hours). Other customers seem to experience scalability problems (which is interestingly a big selling point).
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
