Quarterly insights: Cybersecurity
Evolution of network-based security favoring network detection and response

Cybersecurity threats have evolved to evade many of the basic building blocks of network-based security systems. We believe newer network detection and response (NDR) solutions will increasingly address these new threats and grow to become another major building block of network-based security systems.
Increased computing power that enables cost-effective network monitoring at scale, as well as advances in machine learning and artificial intelligence, have made NDR a powerful and accessible cybersecurity tool.
In this report, we provide a high-level overview of how NDR systems work and why they are needed. We also discuss key areas where NDR systems differentiate themselves, such as in decryption capabilities, and profile four key NDR solution providers.
TABLE OF CONTENTS
Includes discussion of Darktrace, ExtraHop, Stamus Networks and Vectra AI
- A new vanguard of network-based security systems
- Like an all-knowing network administrator
- Historical challenges shape buyers’ NDR purchase decisions
- The decryption debate
- Key NDR solution providers
- Meeting the never-ending challenge
- Cybersecurity index range-bound in deeply negative territory
- Q3 cybersecurity M&A pace similar to Q2
- Q3 cybersecurity private placement pace steady
A new vanguard of network-based security systems
The building blocks of effective network-based security systems continue to evolve. Firewalls and endpoint detection systems (including newer endpoint detection and response systems), which monitor and stop malicious behavior at networks’ perimeters and endpoints, have been two of the most basic elements of network-based security systems. However, some threats have adapted to evade these protections, so network-based security systems evolved to include intrusion detection systems (IDSs) and network security monitoring (NSM) solutions to monitor and act on malicious data as it moves within networks. These newer solutions have also seen widespread adoption, but the growing number of successful cyberattacks and dozens of additional cybersecurity subcategories have shown organizations need still more robust and complementary solutions.
We believe network detection and response (NDR) solutions will increasingly address this need and grow to become a major building block of network-based security systems. Increased computing power that enables cost-effective network monitoring at scale as well as advances in machine learning and artificial intelligence have made NDR a powerful and accessible cybersecurity tool. Many NDR providers have integrated their solutions into workflows of other leading cybersecurity and network solutions, further advancing NDR usability. Further, today’s more sophisticated attack environment is revealing the inadequacies of some other approaches, particularly signature-based approaches, highlighting NDR’s increasing value as part of risk managers’ arsenals.
Like an all-knowing network administrator
The premise of NDR is quite simple: If an all-knowing network administrator could see what data is being sent to whom, this person could do a decent job of identifying malicious and highly suspicious traffic and take action against it. For example, seeing a CFO’s computer being used to query a database for an accounting record would not raise suspicions, but seeing the same query from a software engineer’s computer would be a red flag. Likewise, seeing any computer sending pings to hundreds of network devices (a technique that could be used to map a network) would also be a red flag. This all-seeing network administrator could detect potentially malicious or dangerous activity that the firewall, the endpoint detection and response platform and other solutions failed to stop. Of course, no single person nor even team of people can cost-effectively monitor all network traffic in this way.
NDR solutions take this same approach but execute it with computing power on a physical network device, a virtual appliance or a combination of the two. They recognize known malicious attack techniques and use machine learning and artificial intelligence to identify malicious and highly suspicious traffic and take action against it. More specifically, they observe data traffic flowing across networks through unobtrusive network test access points, or TAPs, that gather data while not actually managing or manipulating data flows like typical switching devices. NDR solutions then determine baseline normal network activity and patterns using machine learning and artificial intelligence. Once they establish baseline activity levels, NDR solutions identify anomalous activity and unauthorized protocols, port utilization, and data transfers that may be associated with threats. NDR solutions alert cybersecurity personnel to threats, and the solutions may take other steps such as quarantining devices and blocking or disabling network segments and traffic.
NDR systems avert cyberattacks with comprehensive visibility across networks
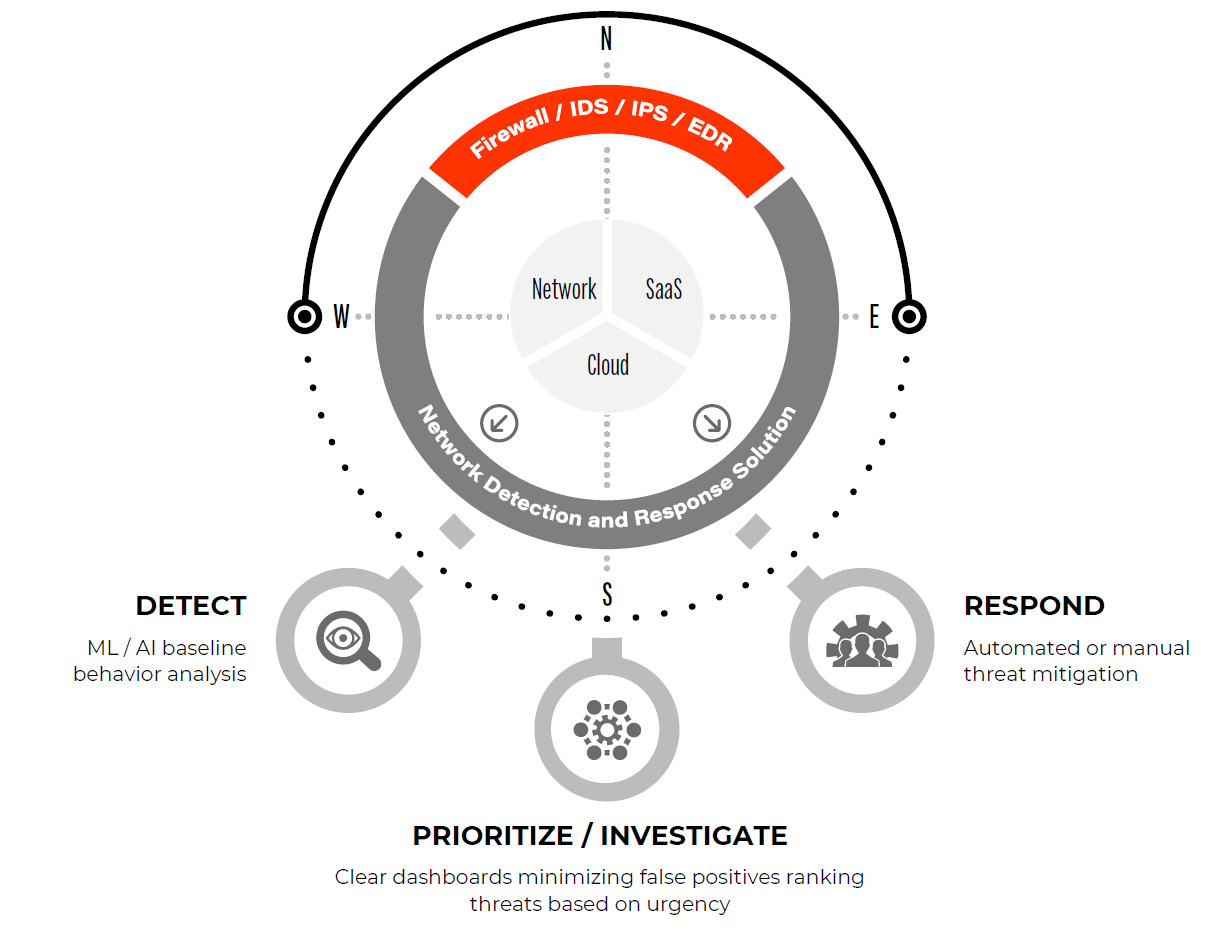
Source: First Analysis.
Note: ML = machine learning. AI = artificial intelligence. IDS = intrusion detection system. IPS = intrustion prevention system. EDR = endpoint detection and response.
Importantly, NDR solutions can detect unknown or emerging threats in real time because they augment the signature-based methods often seen in traditional IDSs and other solutions. NDR solutions continually improve their knowledge and effectiveness based on feedback from cybersecurity professionals indicating which alerts are true risks. Effective NDR implementations highlight and help mitigate many network infiltration attack vectors, including abnormal software installation, command-and-control, lateral movement, exfiltration and malware. They also help prevent non-malicious compromises internal network users may cause, such as accidentally leaking sensitive information, enabling non-permissioned users, and sharing account access information.
Historical challenges shape buyers’ NDR purchase decisions
Until now, several challenges have prevented NDR from being widely adopted. The specific challenges NDR vendors have focused on, and the ways they have surmounted these challenges, help differentiate them in the market and represent key criteria for buyers’ purchase decisions.
Ability to cost-effectively monitor all traffic – The more network segments an NDR solution monitors, the more effective it can be. Ideally, all traffic should be monitored; however, there is a cost to do so. Acquiring the information needed to make intelligent decisions and analyzing such data volumes requires significant computing power. The larger the data pipe, the more resources (and expense) required to monitor it. With exponential growth in network traffic, solutions can become quite costly. Virtually all NDR vendors focus on maximizing their solutions’ efficacy while minimizing computing resource demand and cost.
Ability to minimize false positives – To be effective, NDR solutions must identify and minimize the negative impact of malicious network traffic. However, acting against legitimate traffic needlessly disrupts organizations’ business, and false alarms can overwhelm security personnel and waste their time. NDR solutions often need extensive tuning to avoid generating a substantial number of false positives. It’s also important for NDR solutions to tackle the related challenge of prioritizing threats so cybersecurity teams can focus on responding to the most immediate and pressing risks.
Ability to integrate into existing infrastructure and workflows – Customers want to use NDR solutions alongside other systems in which they’ve already invested. Further, they want their NDR platform to bolster the visibility, functionality and analytics already provided by their IDS, NSM system, security information and event management system (SIEM) and other solutions. A siloed NDR solution forces cybersecurity analysts to switch between multiple security and network consoles to confirm and remediate threats. Ideal NDRs tie into the other cybersecurity systems, network systems, and workflows professionals already use. They also provide complete and immediate network and cybersecurity context so analysts can quickly grasp and act on threats.
The decryption debate
Knowing basic attributes about data flows in a network can be extremely valuable. Easily accessible information such as source internet protocol (IP) address, destination address, packet volume, time and geographic location can provide strong clues that traffic is suspicious. But malicious actors have become increasingly adept at masking their activity, sometimes by embedding tiny amounts of harmful data in otherwise regular data flows to avoid being detected by NDR solutions, thus limiting the utility of these basic data flow attributes. When data flows are encrypted, as network traffic increasingly is, some threats become almost impossible to detect using only basic attributes.
To address this issue, a few NDR solutions now decrypt network traffic. This requires increased compute power and can cause network latency during high-traffic periods as data flows are routed through appliances or endpoint agents for further analysis. These solutions also require endpoint agents to be regularly updated to remain effective and keep pace with organizations’ other technical infrastructure. Some NDR solutions minimize these drawbacks by ingesting traffic already decrypted by other network security appliances.
Other NDR solutions eschew handling any decrypted data due to the risk of leaking protected information contained in encrypted streams, which are sometimes used to protect personally identifiable information and other information that must be protected under laws and regulations such as the General Data Protection Regulation in Europe and the Health Insurance Portability and Accountability Act in the United States. While we believe these concerns are valid and may be a reason not to decrypt certain data streams, our research leads us to believe the benefits of decrypting data to impose a data security framework outweigh the risks if the decryption plan is well documented as part of an overall security framework and implemented with rigorous procedural safeguards.
Key NDR solution providers
The NDR market contains numerous players. Below, we highlight Darktrace, ExtraHop, Stamus Networks and Vectra AI – a few of the pure-play NDR players in the market today. Several other significant companies offer NDR solutions, often as part of broad security offerings. They include Barracuda, Cisco (CSCO), FireEye, Gigamon, RSA Netwitness, Sangfor and ThreatBook.
Darktrace is likely the largest player in the NDR market and the only publicly traded pure play (listed on the London exchange). The company markets four products: Prevent, Detect, Respond and Heal. These tools work together along attack life cycles to assess vulnerabilities, analyze unique data points with self-learning artificial intelligence, and autonomously disarm attacks when they occur. Heal, a product Darktrace is set to release in 2023, helps restore networks to a trusted operational state after attacks. This function is unusual in the market and, if successful, could be a differentiator. Darktrace integrates into over 50 other products cybersecurity teams typically use, enabling teams to use Darktrace’s artificial intelligence capabilities across their systems for SIEM; security orchestration, automation, and response; virtual private networks; and security service edge to fill the gaps where NDR may not be sufficient.
All these features can be deployed across multiple environments including virtual, cloud, Internet of Things, and industrial controls. Darktrace’s website highlights its large enterprise customers such as Anheuser-Busch, Coca Cola, AT&T Mexico and the McLaren Group; however, our research leads us to believe the solution works exceptionally well among small and medium-size businesses and smaller enterprise-size businesses. One potential weakness of Darktrace’s solution is it requires significant tuning to minimize false positives generated by its unsupervised, self-learning machine learning algorithms.
ExtraHop is likely the largest private, pure-play NDR company. It offers its Reveal(x) solution in two forms: Reveal(x) Enterprise, a self-managed and highly customer-tailored NDR solution, and Reveal(x) 360, a cloud-based NDR platform delivered as a service that seeks to quickly eliminate manual burden and overhead. Both solutions can be deployed on premise and in cloud environments. ExtraHop seeks to automate workflows for cybersecurity analysts by detecting threats in real time using rules and behavior-based machine learning, providing comprehensive visibility across the attack surface and then prioritizing threats for investigation.
ExtraHop’s attack visibility dashboard

Source: ExtraHop.
We believe ExtraHop is the only significant player offering a solution that fully decrypts network traffic. It can decrypt all secure sockets layer and transport layer security encrypted traffic, and it can decode more than 70 enterprise protocols for comprehensive risk management. While we believe this provides many benefits in terms of fuller visibility, as discussed above, the solution requires regular agent updates to keep the encryption capabilities in tune with the latest changes from vendors of networking equipment and software operating systems.
ExtraHop offers continuous packet capture and a 90-day record of network traffic, which helps it excel at assisting in streamlined, in-depth forensic investigations. It integrates with most major third-party systems customers use. It is deeply integrated with CrowdStrike’s (CRWD) endpoint detection and response solution and Splunk’s (SPLK) SIEM. This forms a unified extended detection and response solution that seeks to provide complete visibility across networks, endpoints and logs. ExtraHop has even layered functionality from these solutions into its own interface, a time-saver for cybersecurity analysts.
ExtraHop is an enterprise-class solution with large customers including Home Depot, Ulta Beauty, Seattle Children’s, the city of Dallas and others with sophisticated needs and response capabilities. It is likely not the best fit for smaller organizations with little time and few resources to manage the product. We believe ExtraHop’s product is one of the most powerful and impactful, making it a market leader.
Stamus Networks has a differentiated approach to providing organizations with the network detection capabilities they need. When considering NDR solutions, cybersecurity teams often do not want to lose the functionality of their legacy IDS and NSM systems by replacing them with NDR. Knowing this, Stamus Networks provides an NDR solution that integrates and builds on top of existing technologies. In combining the functionality of the three platforms, Stamus Networks brings additional functionality, visibility and detection capabilities into organizations’ network monitoring capabilities, all within the same interface.
Stamus Networks product features
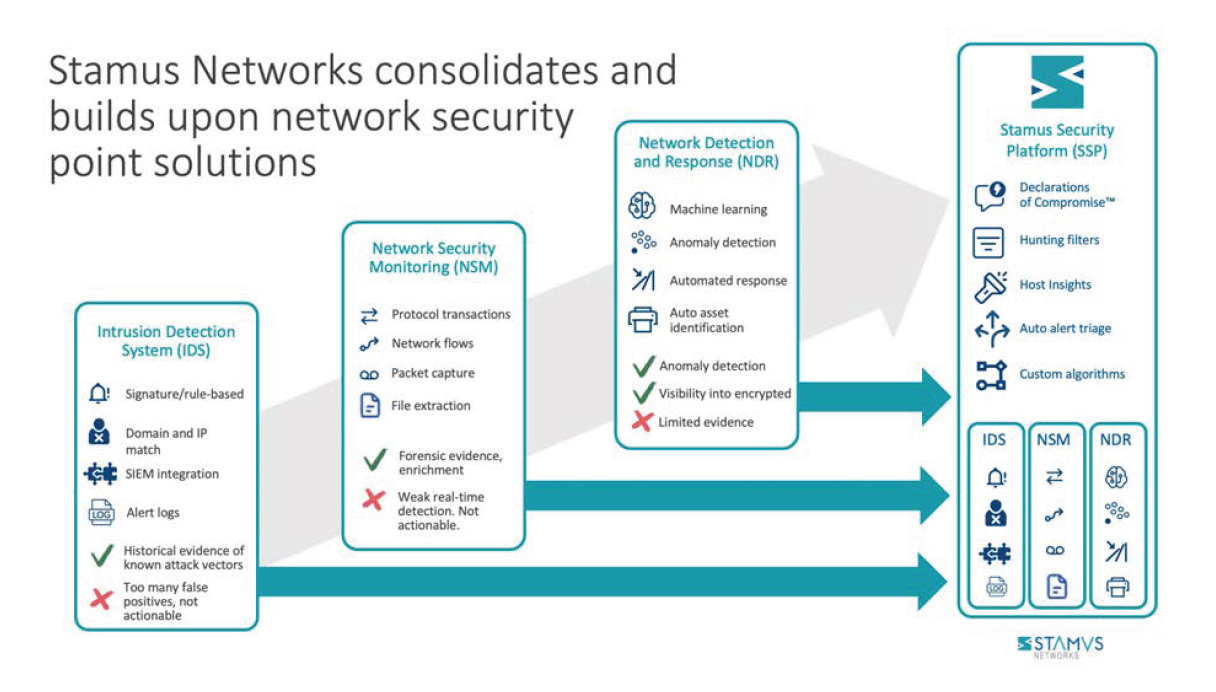
Source: Stamus Networks.
More specifically, the Stamus Networks solution is based on Suricata, an open-source network threat detection engine that has significant market adoption in both commercial and home-grown enterprise solutions. Stamus Networks’ solution is multi-threaded, enabling it to handle high traffic volumes, and it easily integrates with tools for SIEM; security orchestration, automation, and response; and extended detection and response. Stamus leverages its Suricata expertise to replace organizations’ legacy IDS and NSM systems or to supercharge their existing Suricata deployment. From there, the company presents a clear upgrade path for customers looking for increased network visibility from an NDR system. Thus, Stamus customers keep their existing SIEM solutions and can improve their Suricata IDS and NSM functionality, while gaining the benefits of a full-blown NDR solution.
While the company has a strong North American presence, its most significant customers are in Europe and include many leading European financial institutions. We think Stamus is an ideal fit for organizations seeking to upgrade and improve their existing threat detection technology with a comprehensive view of their network.
Stamus Networks’ NDR replaces several legacy technologies and adds modern anomaly detection, automated response, threat hunting, and security event triage to provide protection across entire organizations.
Vectra AI is one of the larger players in the NDR market. It offers three main component applications: Cognito Detect, Cognito Recall and Cognito Stream. These products work together to monitor networks for suspicious activities, collect and analyze information into clear dashboards with actionable insights, assist with investigations and, ultimately, respond to threats.
Vectra positions its artificial intelligence and machine learning capabilities as key differentiators. Its platform triages threats and then works behind the scenes to enrich network metadata with additional network and host information for further examination. Vectra indicates this enables it to identify more compromised network components, creating more visibility for organizations. Vectra keeps the large volume of information manageable by organizing threats into comprehensive dashboards with scoring systems, enabling cybersecurity teams to prioritize threats.
Our research indicates Vectra’s solution is used by a broad range of entities, from mid-size companies through large enterprises. As a pure-play NDR solution, Vectra, like others, partners and integrates with Crowdstrike, Amazon Web Services, Splunk and Microsoft (MSFT) to provide improved visibility and additional functionality relative to that found in traditional IDS and SIEM solutions. Vectra does not decrypt network information for threat monitoring, believing it creates too great a risk of violating privacy laws and slowing network performance.
Meeting the never-ending challenge
The cat-and-mouse game of cybersecurity is a never-ending challenge with enormous real-world economic and societal costs. Fortunately, innovative technology providers continue to develop compelling solutions, turning adversity into opportunity. NDR solution providers are a new vanguard of the effort and one whose compelling benefits should drive substantial adoption in the coming years as NDR becomes a basic building block of network-based security.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
