Quarterly insights: Cybersecurity
Data loss prevention market heating up

A confluence of factors has contributed to an increase in activity in the data loss prevention (DLP) market, which consists of a variety of solutions aimed at keeping organizations’ sensitive information from being accessed or used by unauthorized parties. Key among these factors are the migration of data and computing to distributed cloud platforms that span diverse physical networks, the advent of regulations that demand better data protection, and the explosion of remote computing that occurred as a large percentage of the workforce began working from home due to COVID-19.
While a handful of relatively mature cybersecurity players have dominated the DLP market, a number of these companies may see their positions erode or shift in the current environment, and several relative newcomers appear well positioned to disrupt the market with new technologies and novel approaches.
We provide a high-level overview of DLP technology and the DLP market and highlight a few of the new solutions that aim to make DLP more effective, easier to manage and less costly.
TABLE OF CONTENTS
Includes discussion of AVGO, MSFT, PFPT, PANW and 4 private companies
- DLP market background
- Major players dominate
- Changing IT environments complicate DLP programs
- DLP sometimes integrated with other security solutions
- Recent sector transactions, COVID-19, and regulation drive increased interest in DLP
- Seeing new DLP entrants and approaches
- Incumbents still a force; Microsoft another to watch
- Cybersecurity index continues post COVID-19 rally, in line with Nasdaq
- Cybersecurity M&A continues its post-COVID-19 pause
- Cybersecurity private placement activity retreats in Q3
DLP market background
DLP is somewhat of a catch-all term for a variety of solutions focused on keeping an enterprise’s sensitive information from being accessed or used by unauthorized parties. Sensitive data includes a wide variety of information such as personally identifiable information (names and associated personal data), corporate records such as financial statements and board packages, and intellectual property. While an important goal of DLP is to keep such data out of the hands of malicious actors, it also aims to prevent well-intentioned employees from inadvertently violating regulations or otherwise putting their organizations at risk by sharing data with certain people or in specified geographies.
Solutions vary widely. Simpler solutions identify sensitive information, make sure it is encrypted when stored (at rest), and typically use some type of identity- or role-based authorization to control access. Comprehensive approaches go beyond those basics with measures such as ensuring data is encrypted when being moved (in motion), controlling under what circumstances access will be granted (often in conjunction with machine learning algorithms that detect anomalous behavior), and monitoring and reporting on when and how data is accessed, copied, moved or used. Because comprehensive approaches require identifying and classifying all types of sensitive data, understanding the role of every user of the data, and contemplating every type of network, device and application that might transfer, show or use the data, they are exceptionally complex solutions. Done correctly, a comprehensive approach goes beyond controlling original sensitive data to ensuring unauthorized copies cannot be made or transferred.
Major players dominate
These comprehensive solutions, sometimes referred to as enterprise DLP, grew into a fairly established cybersecurity segment in the early 2000s. A narrow definition would put the market at roughly $1.5 billion in size this year based on a November 2019 study by the Radicati Group. A broader definition that includes related functionality discussed below pushes the market size to multiples of this number. The market – at least as more narrowly defined – is dominated by a handful of relatively mature cybersecurity players, with Broadcom (through its purchase of Symantec), McAfee, Raytheon (through its ownership of Forcepoint, formerly Websense) and pure-play Digital Guardian having the largest market shares.
These companies came to dominance during a period when the network environment was simpler and more centralized than today: Sensitive data typically was created and used inside a controlled network environment where firewalls delineated and controlled boundaries. Many solutions focused on ensuring sensitive data could not leave the corporate network. File names and types could be examined and blocked as they tried to pass firewalls, and the concept of fingerprinting sensitive files (mathematically tagging file contents so that changing a file name or type cannot circumvent controls) became an important part of DLP solutions. As workers and other parties increasingly accessed corporate networks from devices located outside corporate firewalls, enterprise DLP providers added endpoint software to address the risk of data being incorrectly used or transferred on these remote devices.
Changing IT environments complicate DLP programs
Even in a tightly controlled network environment, the need to constantly classify data and users and remain current on contextual changes makes DLP complex and costly, leading many users to feel DLP’s promised return on investment is difficult to obtain. However, networks and computing have changed rapidly in recent years: Now organizations create data in a distributed fashion and access and share it well beyond corporate applications and devices – in cloud-based applications such as Box, Dropbox and Gmail and on smartphones, tablets and personal computers that communicate across diverse and far flung networks including cellular and home Wi-Fi networks.
This trend has only been accelerated by the huge increase in the portion of the workforce working from home due to COVID-19. The result is 1) even greater pressure on companies to monitor and protect sensitive data, prompting an uptick in DLP interest, 2) a more complex computing environment that increases the challenge of creating effective DLP solutions and highlights the limitations of traditional solutions, and 3) opportunities for existing and new DLP providers to win business with innovative solutions.
DLP sometimes integrated with other security solutions
Over the past decade, as organizations sought out simpler DLP solutions with quicker return on investment, they looked for existing security solutions and implementations to incorporate DLP in order to avoid purchasing a dedicated DLP solution. This approach, while not as comprehensive and thus as effective as a well-maintained dedicated enterprise DLP implementation, is better than nothing and often better for those organizations that lack the resources to maintain a dedicated, comprehensive DLP solution. As a result, several cybersecurity areas have become closely aligned with DLP functionality. The following are three areas we think are particularly relevant:
Next generation endpoint security and endpoint detection and response (EDR) – While data can be accessed and misused anywhere, the most likely points of abuse are remote devices. These “endpoints” are also one of the more easily compromised parts of the IT architecture. Therefore, basic DLP rules can be integrated with, enhanced by, and enforced by endpoint security solutions. All the leading DLP companies have endpoint agents that are key to their solutions; McAfee and Symantec historically have been endpoint protection leaders and examples of the tight coupling of DLP with core network security.
However, we often hear complaints that endpoint-only DLP is incomplete and lacks an integrated set of rules and policies used with other risky parts of a computing environment, such as networks and the cloud. The bigger negative we hear is that many endpoint DLP solutions are primarily focused on endpoint detection and response with DLP being an afterthought and therefore relatively ineffective in enterprise implementations.
User and entity (or event) behavioral analytics (UEBA) – This takes the view that it can be equally or more effective to focus on users rather than data. Instead of relying on rules-based data classifications, UEAB focuses on users and learns how they normally interact with data. If the software detects an anomaly, such as access from an unusual location or network route, access at an unusual time, access to data that a user has not accessed before, or access to larger amounts of data than typical, the software can flag this activity, block it or take other actions.
Cloud access security broker (CASB) – Since a CASB controls traffic and enforces security and privacy policies on data moving between an enterprise’s on-premise or otherwise protected infrastructure and cloud-based applications and infrastructure, DLP functionality is inherently part of a CASB’s core function. But a CASB does not provide comprehensive cloud-based DLP because 1) it only covers supported cloud applications, 2) it only enforces rules on traffic moving through the CASB, and 3) like endpoint-based DLP, it is not a comprehensive solution that addresses risks such as loss inside the firewall.
Nonetheless, the risk to an organization’s data entering cloud environments outside of its control has been top-of-mind over the past few years, blurring the line between CASB and DLP. Three of the four leading DLP players have acquired companies specializing in CASB, and the fourth DLP leader, Digital Guardian, has partnered with leading CASB players.
TABLE 1: The most likely root causes of data breaches, 2017
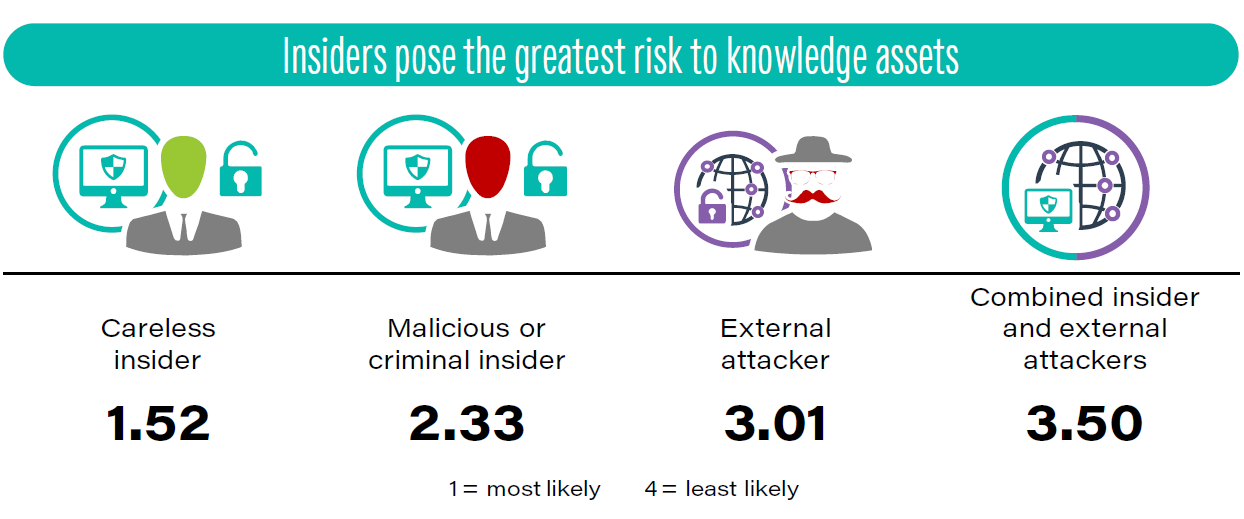
Source: Kilpatrick Townsend and Ponemon Institute, Second Annual Study on the Cybersecurity Risk to Knowledge Assets, April 2018.
Recent sector transactions, COVID-19, and regulation drive increased interest in DLP
For some years, new regulations such as the General Data Protection Regulation (GDPR) in Europe, payment card industry standards (PCI DSS), and myriad healthcare standards have been tailwinds for DLP that continue to gain force in prompting organizations to implement more formal DLP programs. Stolen sensitive data is at the root of most high profile cyberattacks that show no signs of slowing. Two more recent trends – transactions among major DLP players and the impact of COVID-19 – are further accelerating interest in DLP by end-user organizations and existing and potential DLP providers.
First, Broadcom’s purchase of Symantec and a resulting tweaked strategic focus left many observers believing a significant number of Symantec legacy accounts, particularly smaller accounts that may not be as strategic to Broadcom, will reevaluate vendors and might seek to replace their Symantec DLP solutions. Second, Raytheon earlier this year purchased Vista Equity’s minority stake in Raytheon’s Forcepoint business and is expected eventually to divest Forcepoint, creating uncertainty about Forcepoint’s future and an opportunity for competitors to approach Forcepoint’s customer base. Finally, McAfee has had several ownership changes since it became a DLP leader, and some feel it has lost its edge in DLP. In aggregate, the changes have convinced some cybersecurity players that now is an ideal time to take share.
Most recently, COVID-19 has disrupted IT operations, and the sudden shift to working from home (or from other remote locations) has left data protection policies in the dust. Employees are creating and accessing data on home computers, tablets and smartphones that were not part of a controlled IT environment. Further, they have increased use of all types of cloud-based applications and tools, creating significant data control issues and challenging IT department efforts to ensure sensitive information isn’t being compromised, for example, by being displayed and then photographed or screen captured on these devices for later unauthorized use.
Seeing new DLP entrants and approaches
Proofpoint is a good example of a company looking to shake up this market. As a longtime leader in email security, Proofpoint has an accepted email DLP solution. It acquired CASB capabilities several years ago. In November 2019, Proofpoint acquired insider threat management specialist ObserveIT. Proofpoint management has clearly stated its intentions to combine and extend these three capabilities into a next-generation DLP platform and challenge what it sees as vulnerable incumbents. It believes its cloud-native and people-centric approach will enable it to provide the market a more context-aware DLP solution. On Proofpoint’s most recent earnings call, CEO Gary Steele said, “We believe this could be a potential game changer when compared to other legacy on-premise DLP solutions that are currently deployed in the market and represents an opportunity in excess of $3 billion, when including our CASB and insider threat management functionality.”
Palo Alto Networks also highlighted enhanced DLP capabilities on its most recent earnings call, noting it expected to release in the September quarter a new data security module on its Prisma Cloud platform, combining updated DLP capabilities with malware scanning and applying them to cloud storage. The aim is to address the problem of cloud data breaches. This augments its existing significant DLP capabilities, which leverage its ability to apply policies at virtually all parts of the IT architecture due to its already exceptionally broad portfolio of security offerings.
We also expect smaller, nimble companies to provide novel DLP approaches and to address emerging DLP areas. For example, while most companies focus on sensitive data moving into or from the cloud (so-called north-south data flows), early-stage company ShieldX, a specialist in monitoring data movement within cloud environments (so-called east-west data flows) is increasingly playing up its potential for DLP. ShieldX’s solution stops short of taking enforcement action on violations, so for now it is most effective when paired with additional technology to form a comprehensive intra-cloud DLP solution.
Another example is Silicon Valley based SecureCircle, which emphasizes its ability to protect data at rest, in transit, and in use in a way that does not require changes in applications or existing workflows. As a result, it can protect even unstructured data in channels that are difficult to secure but where data is increasingly being created and shared, including SaaS applications and cloud application programming interfaces.
Incumbents still a force; Microsoft another to watch
While we generally agree with market challengers’ claims that the incumbents have not kept pace with IT architecture migrations and are vulnerable to losing share, the incumbents have not been standing still. Immediately after Broadcom acquired Symantec, which brought Broadcom into the DLP game, Broadcom acquired UEBA vendor Bay Dynamics in part to enhance Broadcom’s DLP capabilities. Forcepoint acquired RedOwl in 2017, extending its UEBA capabilities, and Digital Guardian acquired Code Green Networks in 2015 to enhance its position in cloud and mobile environments. Digital Guardian also touts its pure-play focus, history of solving the most complex DLP issues and recent innovations as reasons it stands to gain market share against both incumbents and new market entrants.
Finally, Microsoft has built DLP capabilities into Office 365 and some of its other offerings and has been acquiring the pieces necessary to build a full solution. It touts that DLP is built natively into Windows 10 and the new Edge browser. In late July, Microsoft more formally entered the market with its public preview of Microsoft Endpoint Data Loss Prevention. While it’s too early to assess its performance and market reception, it could be a competitive game changer among organizations using Microsoft computing environments; we’re less sanguine about its prospects and effectiveness in non-Microsoft architectures. In sum, we think DLP is an often overlooked market that is seeing a resurgence of interest and competitive entrants and deserves increased monitoring and focus by investors going forward.
Request full report
To access the full report, please provide your contact information in the form below. Thank you for your interest in First Analysis research.
