From the archive: Network security
Network security industry trends
In our introductory Internet report (May 10, 1996), we highlighted several areas we thought would provide investors excellent near-term opportunities. One of these areas was network security. This report expands our coverage of this market by 1) outlining our investment thesis for the network security industry, 2) segregating the market into five components, and 3) analyzing several companies with particularly strong marketing and distribution capabilities, all of which should be well-positioned to benefit as the industry expands.
TABLE OF CONTENTS
Industry investment thesis
Outlines why network security represents a compelling investment opportunity, driven by Internet growth, expanding market demand, multiple addressable segments, and the importance of marketing and distribution as the industry matures.Market segments
Defines the five core components of network security — encryption, authentication, access control, anti-virus, and administration — and explains how they combine to form comprehensive security solutions.Security applications
Examines emerging applications such as virtual private networks (VPNs) and secure electronic transactions, illustrating how multiple security technologies integrate to address real-world business needs.Axent Technologies
Network security company focused on enterprise security management software that allows customers to establish, evaluate, and centrally manage security policies across their networks.Check Point Software Technologies
Network security technology and applications company best known for its Firewall-1 product based on stateful inspection technology.Raptor Systems
Network security products company built around its Eagle application-level firewall and integrated enterprise network security solutions.Security Dynamics Technologies
Network security company specializing in authentication through patented time-based token systems and public key cryptography through RSA.Vasco Corp.
Supplier of data encryption software, authentication tokens, and network security products, with a strong presence in the European market.
Industry investment thesis
We believe the network security industry is worthy of investor attention for the following reasons:
- Interest in the Internet has acted as a catalyst and has highlighted a pent-up demand for security solutions.
- The industry has a large and growing market.
- Many companies can benefit as the market presents a variety of needs.
- There are many companies with strong marketing and distribution capabilities, two factors we believe will be critical as the network security industry matures.
- As Table 1 shows, the market has recently hit stocks in this industry very hard.
Table 1: Network security industry stock performance indexed against Nasdaq (Feb. 28, 1996 to March 31, 1997)*
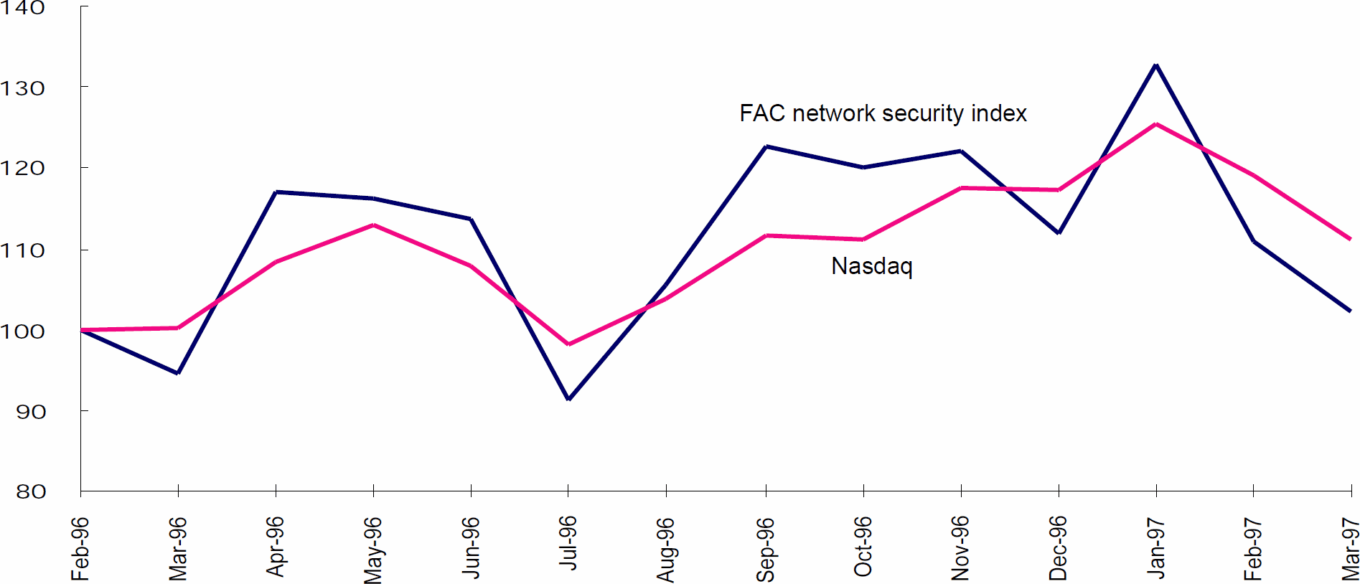
*Market-capitalization weighted indexed stock performance.
Internet as catalyst
Network security in context
Ever since there has been information that someone has wanted to keep private, there has been a need to secure it. In ancient warfare, codes were used to keep battle plans secure and guards were sent to protect messengers carrying vital information. In today’s corporate environment, door security systems, lockable file drawers and desks, as well as receptionists who screen visitors, are all accepted means to secure data.
However, with the advent of computers, a new type of data has arisen: digital data. Initially, only a few people had access to and knew how to use the mainframe computers that held this data. Data security was easily managed by protecting the mainframe. However, as computer networks evolved and PCs stormed the market, new security issues developed. Despite this development, many companies haven’t addressed the new network security issues. Most organizations that have addressed network security employ only simple solutions. Although these measures are inadequate to fully secure information, network administrators have generally considered them sufficient.
Additionally, most companies have had a naive trust of their own work forces. Despite studies that show about 80% of computer-based economic losses occur through internal company personnel, most companies believe their risk is from outsiders. Thus, unless outsiders had access to a company’s network, security issues were largely ignored. The exception to this rule has been in the military and other government departments, where security has been a high priority for years.
Growth of the Internet
For the past couple of years, the Internet has received enormous attention, both in the general media and in the business community. A primary thrust of this attention has been on electronic commerce and the security issues it creates. The network security industry has benefited from this surge of attention. While the Internet and ramifications of its use have produced some new security risks, most risks being highlighted existed before the explosive growth of the Internet and will exist whether or not the Internet continues to gain prominence.
For example, because external users may now have access to an internal network through the Internet, companies have begun evaluating which users should have access to which network resources. While the Internet is the catalyst causing companies to develop such access policies, doing so is essential regardless of whether the network is part of the Internet. Not only will the recently developed Internet infrastructure need to be outfitted with security products, but also most of the networking infrastructure put in place during the past decade. Because of this growing demand, we believe the network security market is much larger than the secure use of the Internet.
Based on the interest in the market and the penetration rate of other technologies into corporate America, we believe most network security purchases will be made during the next three to eight years with a lag in international markets. This demand should create tremendous market growth and opportunity for companies that can establish themselves in this fast-changing market.
Large and growing market
The boundaries of network security are somewhat vague. However, we estimate 1996 sales of network security products exceeded $600 million. We expect this number to grow to at least $4 billion within five years. This implies a compound annual growth rate of more than 45% during this time period. Table 2 shows how we expect this market growth to break down by segment.
Table 2: Estimated five-year growth of network security market (in millions)
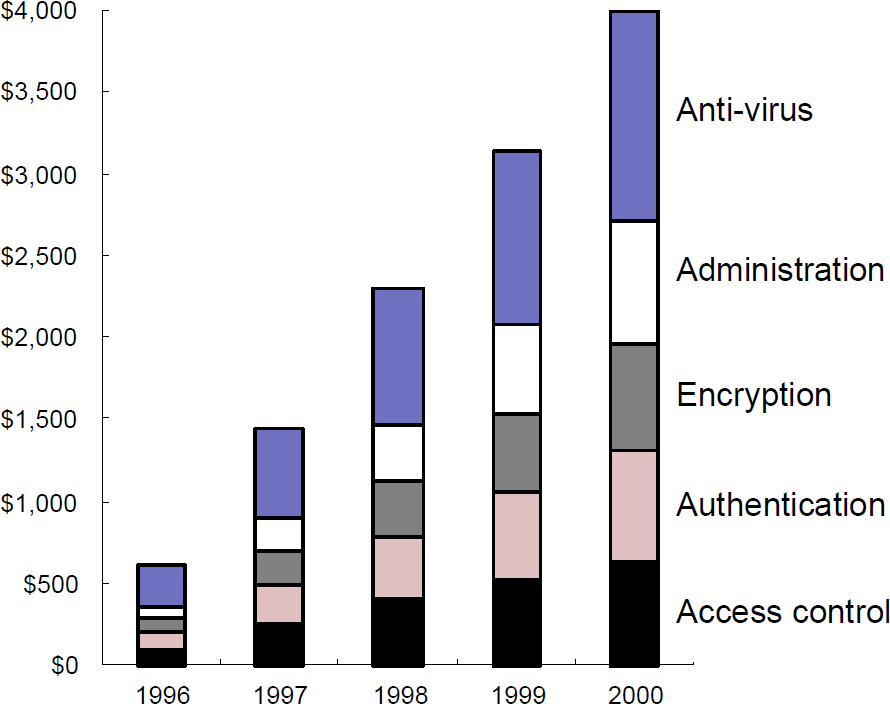
Source: First Analysis Corp.
Market segments
We view the network security market as breaking down into five segments:
- Encryption: Converting information into an unread-able pattern and allowing only authorized parties to decrypt (i.e., decode) the data. Leading companies in this segment are RSA(purchased by Security Dynamics) and Cylink Corp.
- Authentication: Verifying that a user is who he or she claims to be. Leading companies include Security Dynamics and Vasco.
- Access control: Limiting a user’s access to only the resources for which he or she is authorized. Firewalls are included in this category. Leading access control providers include Check Point, Raptor, Trusted Information Systems Inc., and Secure Computing Corp.
- Anti-virus: Programs that scan for and, in many cases, remove computer viruses. Leading companies include McAfee Associates Inc., Symantec Corp., and Dr. Solomon’s Group.
- Administration: Setting, implementing, and monitoring security policies. Leading companies include Axent, International Business Machines Corp. (through its Tivoli division), and Computer Associates International.
Technology-based vs. application-based segments
The segments discussed above are generally technology based, not market based. For example, encryption uses different technology than access control. Buyers are generally less interested in the technology used than in product functionality and the security solution. To date, most security companies have specialized in a single technology. Over time, we believe companies will market security applications and solutions rather than technology. As this evolution occurs, these technology-based classifications will likely blur and lose meaning.
After we examine market segments, we discuss two growing applications, virtual private networks (VPNs) and secure transactions, both of which demonstrate how several technologies can be combined to address business issues.
Multiple needs, multiple solutions
In addition to having outstanding growth potential, we believe network security is an intriguing investment area due to the number of market segments. While we believe many of the leading companies in each area will integrate over time, such as in Security Dynamics’ (authentication) purchase of RSA (encryption), we also believe there will be companies that specialize in one or two segments for several years to come.
Balancing privacy and practicality
Within each category, there are trade-offs unrelated to price. For example, stronger encryption is slower; better authentication can frustrate valid users. Thus, unlike some technologies in which faster or stronger is always better given equal prices, the best security product is that which best meets the customer’s needs. Thus, several companies can be leaders and offer equally good solutions in each segment.
A needs-based market
Before describing each category in detail, we note that we don’t feel any one segment necessarily takes precedent over another. Many analysts, and indeed most of the companies in this industry, present security as a framework with one technology at the core and others building from it. Interestingly, the technology at the core changes from company to company. We feel security needs, and therefore technology needs, depend on the requirements of the customer. Some companies may start with security administration tools and build from this base. Others might start with access control for their World Wide Web site and expand from there.
We feel complete solutions must address all five areas. One doesn’t necessarily come first or have inherently greater importance than any other. The order and importance of each is generally specific to the needs of the company implementing it. We feel trying to develop or impose a single framework is counterproductive. More important to developing a network security solution is ensuring that all five segments are addressed.
Table 3 shows how each segment contributes to a comprehensive security solution. While a certain level of security can be achieved if only a few components of network security are implemented, optimal security can’t be achieved unless all aspects are addressed.
Table 3: Five components of network security
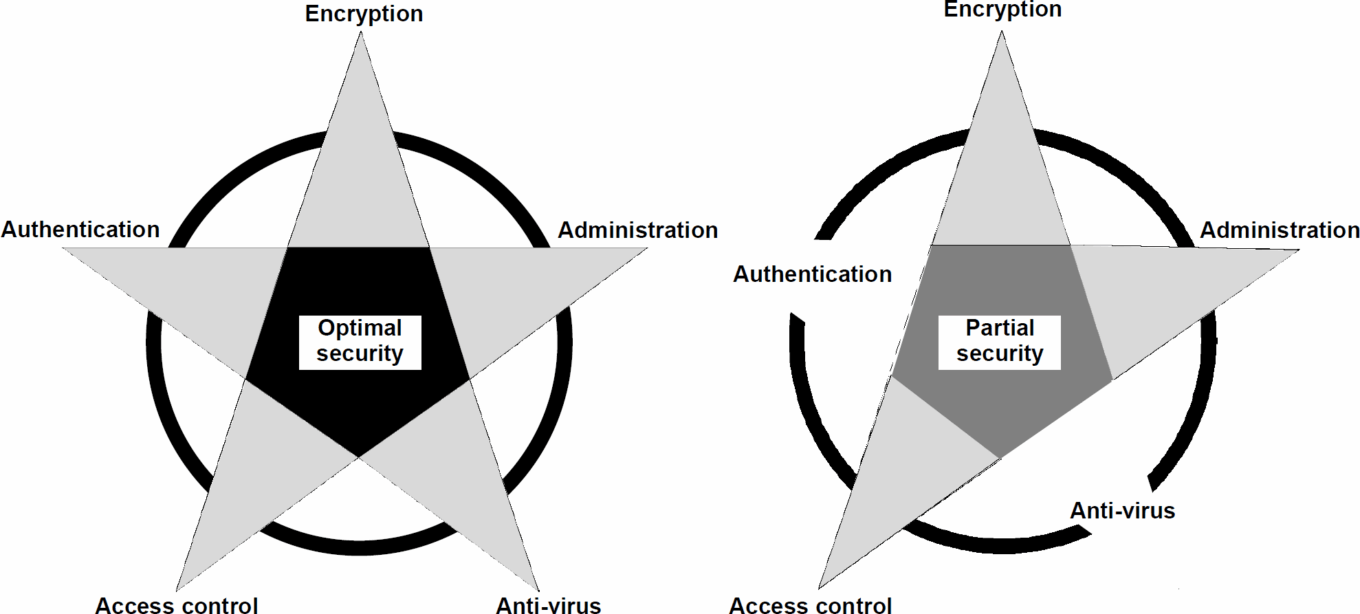
Source: First Analysis.
Marketing and distribution are key
As is true with most emerging high-tech industries, solid technology is only a prerequisite for success, not a guarantee. Many of the companies in this area are engineering rich with deep roots in the high-tech world of government security. However, we believe many of these companies will fail in the commercial market because they will fail to develop the marketing skills, distribution channels, and strategic partnerships critical for long-term success. In addition, their solutions may not be standard products that can be cost-effectively sold in high volumes. We are strongly biased toward companies that appear to be marketing rich as long as they have respectable product offerings.
We are skeptical of a marketing-deficient company regardless of its technology, although it may be an appropriate investment for its buyout potential as the industry consolidates.
Market segments
After we discuss the five market segments in detail, we highlight five companies we feel understand the importance of—and have demonstrated—marketing savvy. Each has strong technology and at this point appears to be among the leaders in developing its market.
Table 4 below outlines which companies participate in which segments. Though it is by no means comprehensive, it presents many of the leading companies in each area.
| TABLE 4: Network security companies by sector |
|---|
| Encryption |
| Cylink Corp. (CYLK) Other companies include RSA (acquired by Security Dynamics), Certicom Corp. and Terisa. |
| Authentication |
| Security Dynamica Technologies (SDTI) Vasco Group (VASC) Other companies include AssureNet (recently acquired by Axent), Enigma Logic (acquired by Secure Computing), Leemah Datacom Security, CryptoCard, and a variety of biometric identification and other companies. |
| Access control and firewall |
| Check Point Software Technologies (CHKPF) Secure Computing Corp. (SCUR) Trusted Information Software (TISX) Raptor Systems (RAPT) CyberGuard Corp. (CYBG) Other companies include MilkyWay Networks Corp., Cisco Systems, International Business Machines Corp. and DEC Enterprises |
| Anti-virus |
| McAfee Associates (MCAF) Dr. Solomon’s Group (SOLLY) Other companies include Symantex Corp.’s Norton division |
| Administration |
| Axent Technologies (AXNT) Memco Software (MEMCF) Other companies include IBM’s Tivoli division, Computer Associates International and Hewlett Packard Co. |
Source: First Analysis Corp.
Companies are listed under the segment from which we feel the company derives most of its revenue and profit; most companies compete in multiple segments.
Encryption
Encryption involves a code or algorithm that changes data into an unreadable form. Only someone who knows the decrypting code can read the encrypted data. Encrypted data is useless, and thus eliminates the need to worry about access control and authentication as long as the data remains encrypted.
The ability to encrypt data has obvious implications for sending data via a network one doesn’t control (e.g., the Internet). However, encryption has broader applications. For example, if all the data on a laptop is encrypted and only the user has the decryption code, anyone stealing the computer can only use the hardware. All the data files would be impossible to decipher, and no sensitive data could be stolen. Taking this to its extreme, every file on every computer could be encrypted and accessed only by someone possessing the correct code to decrypt it. However, as we approach the limits of absolute privacy, we also approach the limits of privacy’s usefulness. Too much encryption can be cumbersome and disrupt productivity.
Keeping the key safe: secret vs. public key
It is mathematically possible to encrypt data so that it is almost impossible to decipher without the decryption key. However, the question arises: How does one transmit the decrypting key in a way that no unintended parties can steal it and thus decrypt data? It is analogous to the challenge of sending a messenger with a locked briefcase but still making it possible for the receiver to open the briefcase and retrieve the message.
Secret key encryption
There are two primary encryption methods in use today, secret key encryption and public key encryption. Secret key encryption involves two parties that know a common code. For example, Sam (the sender) encrypts a message using the secret code and Rachel (the receiver) uses the same code to decrypt. As long as the parties have a secure way to exchange the code, this is a very secure method. (See Table 5.)
TABLE 5: Sending encrypted key message, both parties using a secret key
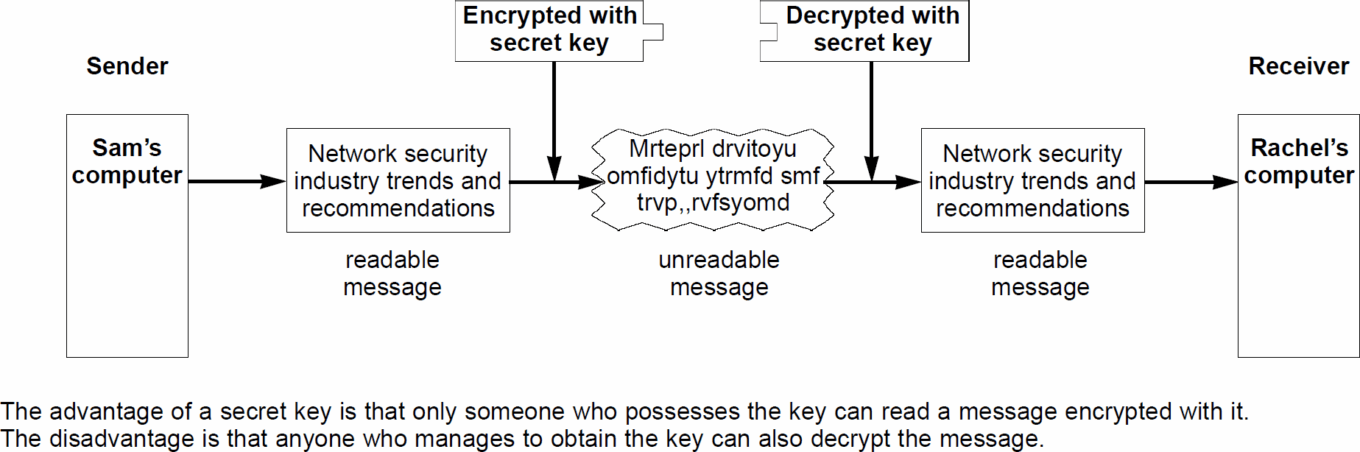
Source: First Analysis.
However, one often doesn’t have any way to send or store the code in a secure manner. Obviously, sending the decrypting code via the Internet just before sending an encrypted message is an invitation for the wrong party to read the message.
Public key encryption
The concept of public key encryption is a response to the problem of sending the keys securely. Under this method, a person encrypts data using a public key to which everyone has access. (Public key codes may be listed in a directory, similar to listing a public phone number in a phone book.) However, when a sender uses public key encryption, the data is encoded so that only the intended receiver’s private key can decrypt the data. Thus, anyone can send Rachel an encrypted message (using her public key) and only she can decrypt the messages (using her private key). (See Table 6.)
TABLE 6: Sending encrypted key message using public-private key pair
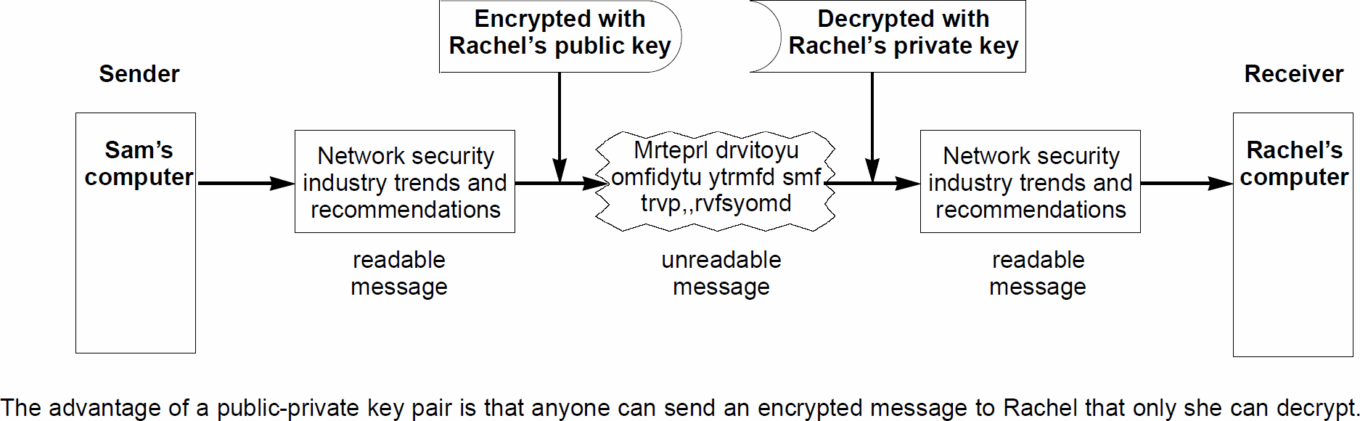
Source: First Analysis.
Software to generate key pairs (a public key and matching private key) can be purchased from a few companies. The two leading public key cryptography companies are Cylink (using Stanford University’s patented public key technology) and RSA (using Massachusetts Institute of Technology’s patented technology).
Strength vs. speed
In addition to the question of secret key vs. public key, a company must determine what encryption strength it needs in light of its cost and in terms of the computer resources (and time) required to encrypt and decrypt a message. As mentioned above, the state of mathematics today makes excellent encryption algorithms relatively easy to produce. However, it takes considerable computer processing power to subject each bit of data to the algorithm. The better the encryption, the more computer resources are required.
Encryption length
Encryption strength is generally measured in terms of bit length. A code using 48-bit encryption is the strongest approved for unrestricted export. A 48-bit encrypted code could be broken in as little as a few days to as long as several weeks, depending on the speed of the computers used to crack the code. Security Dynamics issued a challenge to find the match to a 48-bit key to highlight weakness in exportable encryption. The 48-bit key challenge was solved in less than a month, requiring 312 hours of computer processing time and a network that encompassed 3,250 networked computers testing as many as 1.5 trillion keys an hour. Thus, with the necessary computer resources, the code was broken relatively easily, and while 48-bit encryption may be sufficient for some users, it is obviously not sufficient for all.
A code using 120-bit encryption is orders of magnitude stronger and would take years to crack. A code using 1,025-bit encryption is basically uncrackable with today’s technology. Of course, if a company decides to use software to encrypt all data traveling via the Internet with 1025-bit encryption, its ability to send data would be greatly reduced since advanced encryption software operating on current hardware will reduce transmission speed.
Methods to increase speed
One way to solve the speed issue is through the use of dedicated hardware to perform the encryption. Using an application-specific integrated circuit computer chip (ASIC) or other dedicated hardware, very strong encryption can be accomplished at higher speeds.
Another way to increase speed is to use public key cryptography to send a secret key. Since secret key cryptography is typically faster, sending a unique secret key with each transmission can reduce the computing processing time required for decryption. By encrypting the secret key with public key cryptography, the sender and receiver have greater confidence the secret key won’t be intercepted.
Thus, as network administrators analyze their encryption needs, they must balance the cost of dedicated hardware, the need for strong encryption, and the desired speed of their data transmissions.
Government regulation
The U.S. government has taken an active role in regulating encryption technology. Its most important action has been to establish export controls over strong encryption. There is an ongoing battle between the encryption industry, which wants no restrictions on encryption, and the government, which would like to have access to all encryption keys if needed for law enforcement or national security reasons. Currently, any strength encryption can be used within the United States. For export purposes, significant restrictions exist for encryption of more than 40 bits.
One way restrictions can be eased is if the entity employing the encryption has a key recovery facility (i.e., a copy of all encryption keys being exported). Government agencies feel that if they have legitimate cause, they should be able to recover encryption keys. Trusted Information Systems has a patent related to key recovery and is licensing this capability to major companies such as IBM. Cylink provides key recovery capabilities for its keys.
While export controls are in place, foreign-based competitors have a substantial advantage in international markets. Furthermore, major U.S. companies that wish to build encryption into their products (e.g., Cisco Systems Inc. and Microsoft Corp.) are reluctant to use any encryption stronger than the exportable limits as these products would require both domestic and international versions. Producers of multiple versions would be required to closely track the sale of domestic versions if they use nonexportable encryption. This situation has limited the strength of encryption major networking and software manufacturers have been willing to use in their products. The strength of exportable encryption is a hotly debated issue, and there is legislation before Congress that seeks to resolve the conflicting goals of encryption providers and government regulators.
Authentication
Authentication is the process of making sure a network user is who he or she claims to be. Though tightly integrated with access control, authentication has its own technology and issues. In the past, authentication was visual. An employee came into an office and was given access to certain files because that employee was recognized. A stranger entering the office should be stopped by the receptionist. However, if the employee had an identical twin, the authentication procedure would be foiled. On a computer network, visual authentication is impractical, and thus other means of verification must be found. Three broad methods of authentication are combined by testing for:
- something one knows,
- something one possesses, and
- a physical attribute.
Below is a discussion of how these authentication techniques are used in practice and the strengths and weaknesses of each; no technique is foolproof.
PINs or passwords: Something one knows
With a PIN (personal identification number) or a password, the user enters a name or proxy for a name and a unique code. The same code is used every time. This is unquestionably the most popular type of computer network authentication. However, if someone knows a user’s password or can intercept it as it is sent via a shared communication line, an impostor can pass as that user. The strengths of this system are its ease of use, ease of administration, and low cost. The drawback is the ease with which it can be defeated. While this type of authentication is suitable only for relatively nonsensitive data, it is widely used today even to protect sensitive information.
Tokens: Something one possesses
There are a variety of token devices that vary in procedures; however, the core of the concept is the combination of something you know (a password) with something you have (a device) that must both be present to authenticate a user.
Synchronous tokens
One type of token is the synchronous token, which changes a user’s authentication code every 60 seconds. For example, if Sam has a token from the leading token company Security Dynamics, he enters his password into the authentication device, just as he would if he were only using a pass-word. The device then waits for Sam to enter the number that shows on his SecurID card. This is a dynamic, one-time-only password in the form of a randomly generated number that appears only on his card and only during the particular minute of time during which he attempts to access the network. If he doesn’t have the card in his possession, he won’t know what number it shows and he won’t be able to access the resources he requested. (See Table 7.)
TABLE 7: Access procedures with synchronous token
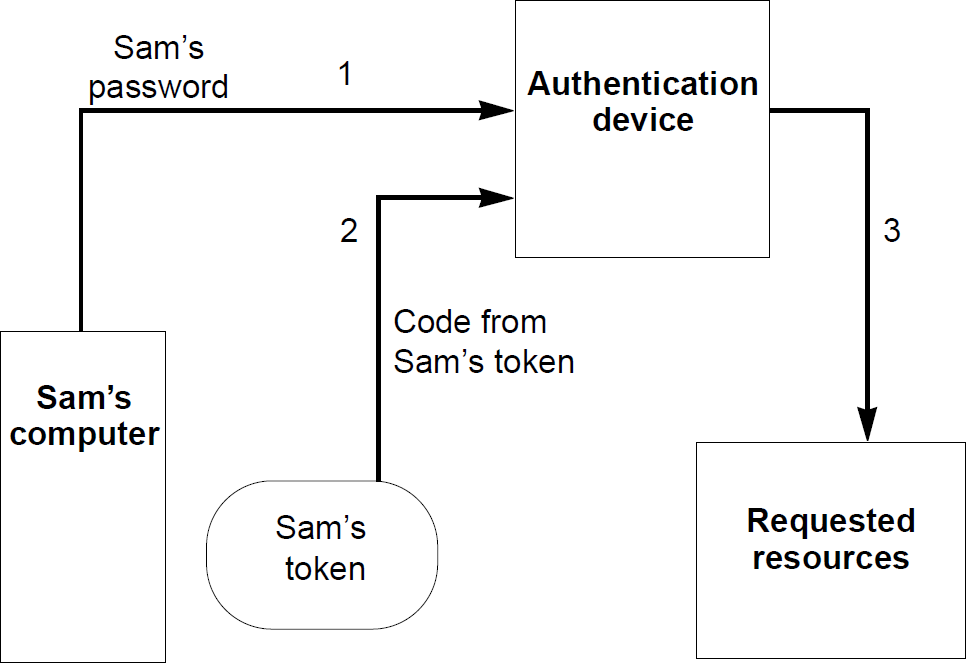
Source: First Analysis.
Challenge-response tokens
Challenge-response tokens offer another type of authentication. When the user (Sam) enters his password into the authentication device, the device responds with a challenge code. Sam enters this challenge into his token, and the token produces another code. Sam then enters this third code into the authentication device. Only if the device accepts this final code will Sam be given access to the requested resources. (See Table 8.)
TABLE 8: Access procedures with challenge-response token
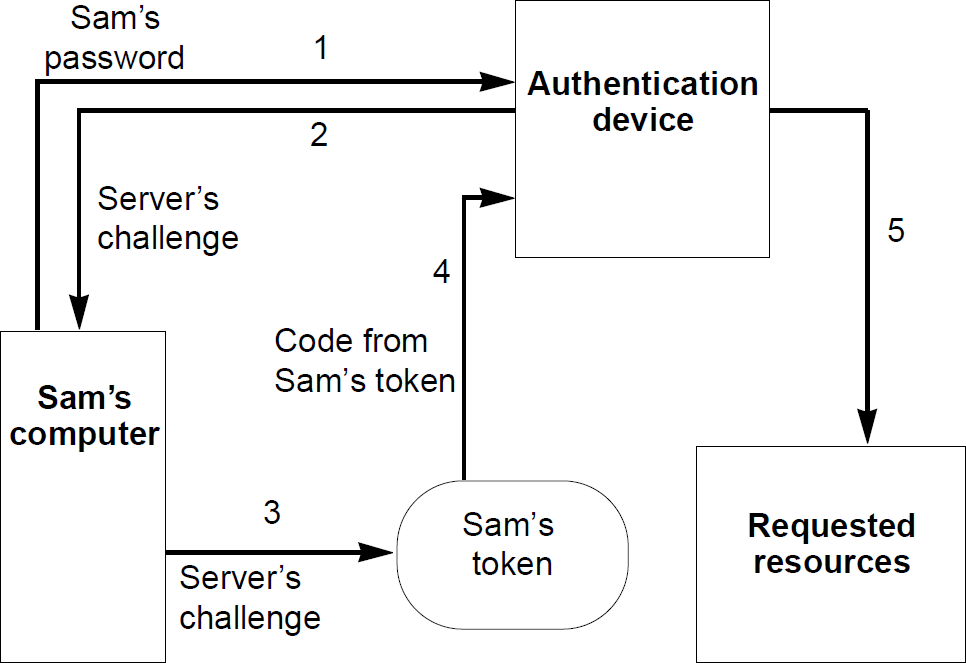
Source: First Analysis.
Other token technologies use variations of these basic concepts.
Tokens vs. passwords
Tokens offer substantially better authentication than passwords alone and have enjoyed tremendous growth during the past few years. One drawback to tokens is the cost relative to password-only systems. However, the cost is relatively minor compared to the potential cost of allowing the wrong people to access a network. For companies serious about security, cost may not be a major issue. Another drawback is administration. Every card must be issued and then tracked throughout its life. Cards that are lost, stolen, or broken must be canceled and replaced. Also, users must remember to keep the tokens with them. If Sam misplaces or forgets a token, he won’t have access to the network without an override of some sort. For a large number of users, the administrative hassle is a major drawback.
Imbedded tokens
To avoid the lost/forgotten/stolen token problem, the concept of software-only tokens is taking hold. The concept is the same as card tokens; however, rather than physically holding a token, the functionality resides as software on the computer. This approach is used mainly for laptop computers and mainly by users accessing a network remotely. The danger of this system is that if someone who knows or can guess the password gains access to the computer, they also have the token and therefore access to the network.
Biometrics: A physical attribute
A third approach to authentication is the use of biometrics. This approach uses some unique physical characteristic to identify a person. The receptionist identifying Rachel by visual recognition is using a form of biometric authentication. For computer networks, the biometric methods most often employed are fingerprint verification, retinal scans, and voice verification. If done correctly, fingerprint checks and retinal scans are highly accurate (though no biometric is perfect), and thus provide a very high degree of security. The drawback to such systems is cost and intrusiveness. Adding fingerprint readers or scanning devices to every network access point is a prohibitively expensive proposition for all but the most sensitive networks. Further, these procedures, particularly the retinal scan, are obtrusive and make many users uncomfortable.
Voice verification is not nearly as intrusive; however, historically, it has been expensive and not as accurate as other biometrics. The equal-error rates (the rate of an equal percentage of authenticating the wrong person and rejecting the correct person) has been much higher than for other biometrics. Improvements in equal-error rates and the lower cost of DSP (digital signal processing) technology have greatly improved the cost-to-performance ratio of voice verification, and we believe this is the most likely biometric to grow in the near to medium term.
Access control
Access control is about limiting the access to a network or parts of a network. Access control works in tandem with authentication, allowing some users to access all parts of a network but others to access only certain parts. For example, the president of a company may have access to the entire network, the network administrator may have access to everything but the president’s personal computer files, and the receptionist may have only limited access to the network. Thus, authentication is required for access control to be possible. However, once a user is identified specifically or generally classified (e.g. unknown user entering via the Internet), systems must be in place to limit the user’s access. Authentication without access control has only limited effectiveness and vice versa.
Physical access control
Controlling physical access to a network is one of the best forms of access control. However, in a distributed computer world, where computers are networked, physical access control is not possible. Therefore, other methods must be found.
For most companies, the primary concern is restricting outside users from accessing the company’s network. Before widespread connection to the Internet, this wasn’t a major challenge as there was no easy way for an outsider to access the network. However, the Internet, and the World Wide Web in particular, are opening organizations’ networks to outside users. The security risk exists because once connected to the network, unauthorized users may find ways to access parts of the networks other than those intended (e.g., other than Internet sites.)
Firewalls
The primary device used today to keep outsiders from penetrating certain areas of the network is a firewall. There are many types of firewalls, but all share a common method of examining an incoming data packet and determining whether it is from a valid user. Only after the user is found to be valid is the data allowed to pass through the firewall. The firewall can be compared to the security checkpoints at an airport. Each person (equivalent to a data packet) is examined, and only if the person has a ticket, which shows he or she has a reason to enter the terminal, is the person allowed to proceed.
The three primary firewall technologies are packet filtering, application-layer gateways, and a newer method called stateful inspection. The firewall companies themselves, of which there are dozens, make tremendous distinctions between the methods, and indeed there are major advantages and disadvantages to each. However, we aren’t convinced consumers care which technology is used, or know which technology is best for them. Thus, though we devote space to describing each, we believe a company’s ability to market its firewall technology is far more important than the technology itself. Further, just as different companies need different levels of encryption, different companies need different levels of access control; therefore, many technologies may have a play in the access control market.
Packet filters
Typically, a packet filter screens communications by analyzing the individual pieces, or packets, of information that make up a communication transmission. A packet filter allows or denies data packets passage through the firewall based on information contained in the packet’s header. Usually, the filter looks at the IP (Internet protocol) address of the packet sender. If it meets a specified rule, the data packet is allowed to pass. If not, it is blocked. For example, data from Sam’s IP address has access to Rachel’s protected local network; unauthorized users don’t. Any packets sent by an unauthorized user are denied. Equally, a packet filter firewall can deny transmissions to certain (or to all) IP addresses outside the local network. (See Table 9.)
TABLE 9: Packet filter firewalls
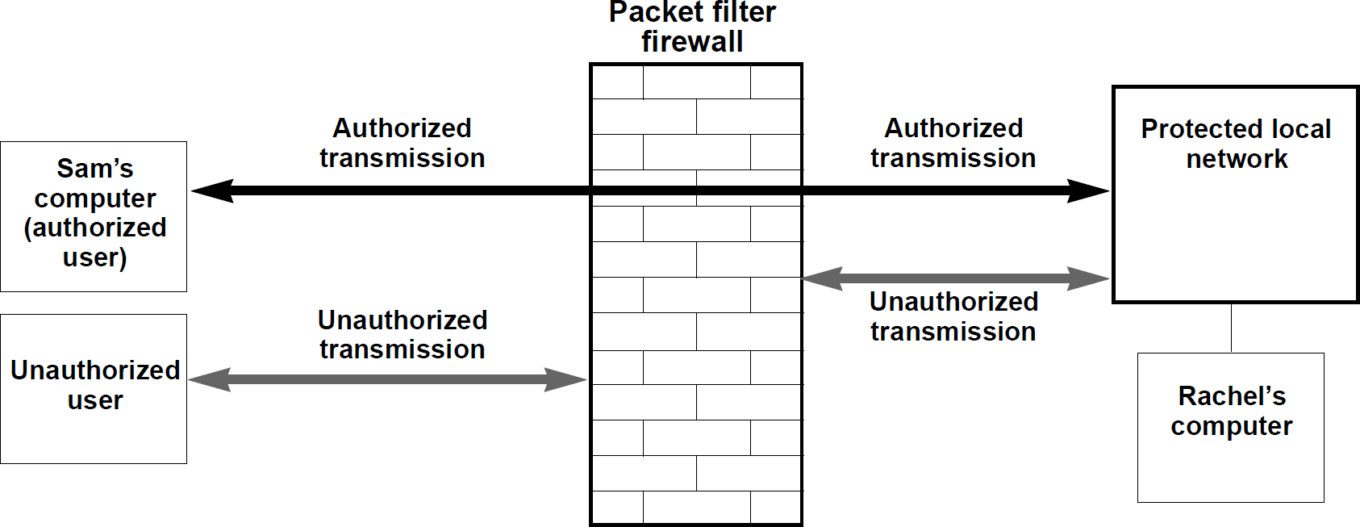
Source: First Analysis.
One drawback is that the IP addresses of authorized users must be updated as changes occur. Another drawback is that IP addresses can easily be spoofed (making an unauthorized IP address look like an authorized IP address), allowing unauthorized users access to the network. For example, everyone who knows Sam’s IP address could make their IP address look like Sam’s and thus have access to Rachel’s network.
Application-level firewalls
Application-level firewalls look at the application being accessed, not just the IP address. Sam’s IP address may be allowed to access Rachel’s IP address to retrieve an .html (World Wide Web) file, but may not be authorized to access the e-mail system at the same IP address. IP addresses both within and outside the network must pass through the firewall before being allowed access to a network’s IP addresses. (See Table 10.)
TABLE 10: Application-level firewalls
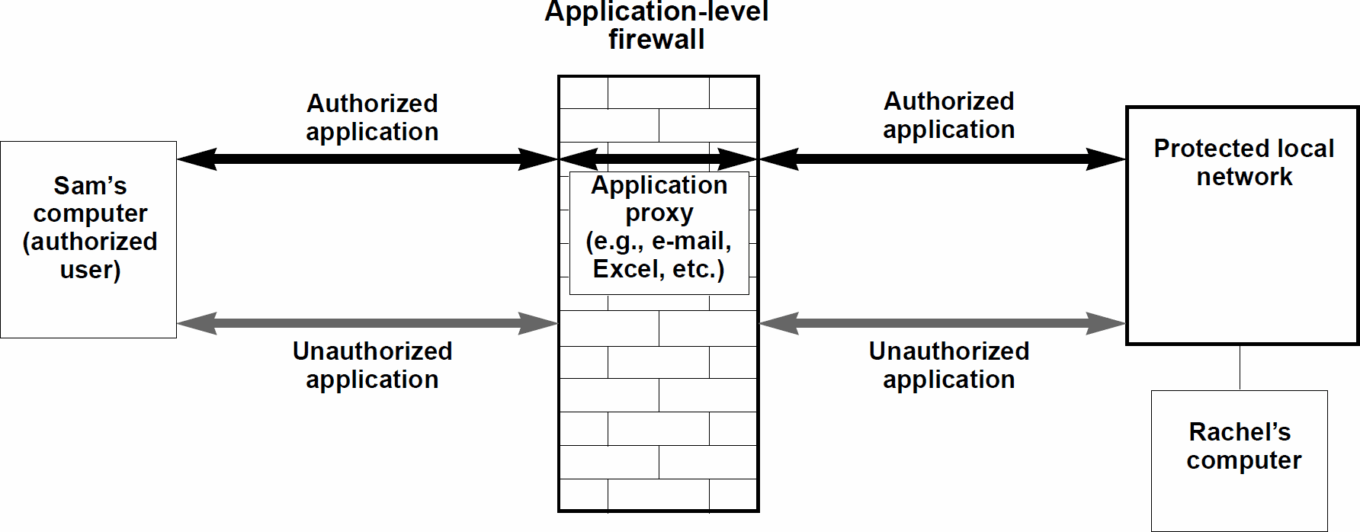
Source: First Analysis.
This firewall effectively becomes the IP address for the data. In some cases, the data is completely replicated before entering or leaving the secured area. In other application-level firewalls, only the IP address is changed, and the rest of the data is passed unaltered. Both methods reduce the chances of IP spoofing.
Application-level firewalls can provide a higher, more finely tuned level of security than a packet filter firewall. The drawback of application-level firewalls is that every application must have a proxy, or copy, on the firewall. If an application doesn’t have a proxy for it on the firewall, the packet can’t pass through. Similarly, application-level firewalls can restrict which applications can be used to send files outside the network.
This requirement for an application proxy can be a problem. For example, if Sam is outside a network protected by an application-level firewall and sends an e-mail to Rachel with an attachment in the latest version of Microsoft Excel, the firewall must have application proxies for both the e-mail system Sam is using as well as the latest version of Excel. If the firewall doesn’t have both proxies, Rachel won’t be able to receive her message or the attachment.
Stateful inspection
The leading firewall provider, Check Point Software, has its own patent-pending solution called stateful inspection. This method looks to the application level to determine whether communication should be allowed. Once a session is started, it tracks the state of this communication, and as long as the state doesn’t change, further communication is allowed without having to access the application level. For example, Sam would be able to continue sending messages with attachments as long as he doesn’t try to do anything else, (e.g., access protected network files). In theory, at least, this provides the safety of an application-level firewall and the speed and scalability of a packet-filtering solution.
Secure operating system
Other debates about firewall technology focus around whether a good firewall must have a secure operating system or whether it can run on a common operating system such as those based on Unix and Windows NT. Even if the type of firewall is meaningful to customers, for the bulk of the market, the operating system question isn’t. We note there is considerable evidence (though not conclusive) that a secure operating system provides a higher level of security.
Anti-virus
Even if a company has excellent authentication, access control, and encryption, it may find its network infected with a virus. For example, Rachel may bring a disk from home that her child used at school where it picked up a virus. A virus is a computer code embedded in a program that causes the computer to perform an unexpected function. This can be as harmless as causing a computer to say hello when it is turned on or as disruptive as deleting all files on a network. A good anti-viral program stops viruses before they cause damage.
The leading anti-virus companies spend their time keeping up with all known viruses so they can distribute updated versions of anti-viral software regularly to customers. Anti-viral software is one of the biggest segments and most mature because 1) the ramifications of a virus infection can be so severe, 2) viruses are so common, and 3) viruses were known to be a threat even before widespread use of the Internet.
Three major players compete in this market: McAfee, Symantec’s Norton division, and Dr. Solomon’s.
Administration
How does a company track all the tokens, firewall access control rules, encryption rules, etc. it uses? Even more importantly, if a company has all the above-mentioned security measures in place, how can it be confident all components of the security system are providing the desired security level? To find the answers to these questions and to help keep track of all the security issues, network security administration has become a major part of the security market. Most companies that offer security products have some administrative capabilities. Others specialize in this area.
Audit security
One type of administration tool is a security audit device. Based on a company’s security rules input by the network administrator, this software continually audits the system and looks for breaches of those rules. For example, an administrator may wish to have all passwords be at least eight characters and be changed once a month. The audit software can monitor passwords and notify the administrator when a password violates this rule.
Monitor activity
Another type of administration tool monitors the network for suspicious activity. Most security breaches by hackers are accompanied by an unusual level of network activity. Administrative software can monitor network activity in real time and take actions such as notifying the administrator, recording the suspicious incident on a report, or even shutting down the network when suspicious activity occurs.
Management control
Finally, administration software allows management control of distributed and diverse security products. If only a single person has the ability to make changes to a network’s security, that person may become a bottleneck. However, the more people given the privilege to make changes, the lower the level of security. Systems with good management administration allow a single user to allow others to make changes only to parts of the systems and only if those changes conform to an overall security policy.
Single sign-on
One application tool that takes advantage of good administration is single sign-on. A problem with today’s networks is that each network, and sometimes each resource, has its own security. For example, Sam may have to enter a password to access his computer’s hard drive, enter a different password to check his e-mail, and yet another to access particular files. Ideally, the information from the original sign-on should be passed between resources and allow Sam access to all the files and applications he is authorized to use and deny him access to the rest without asking him for any more information. This is the promise of single sign-on. However, excellent administration capabilities must be present for single sign-on to work. If all the security solutions don’t work together, single sign-on can’t work either.
Security applications
We highlight two applications that are in dire need of security solutions to realize their full potential. The first is known as the virtual private network or VPN.
Virtual private network
Today, thousands of companies spend billions of dollars leasing dedicated communication lines between facilities. While these lines are cheaper than paying telecommunications companies on a per-use basis, as they do for calls outside of these lines, the cost is still quite high. Importantly, these are dedicated lines being used solely by that company. If the company doesn’t use the full capacity of these lines 24 hours a day, it is paying for excess capacity. All private networks have significant wasted capacity.
Ideally, a company would like to share the lines with other companies so less capacity is wasted and the companies can share costs. However, if a company’s line is not dedicated, some switching must take place by a third party, resulting in a data security risk. The Internet is the ultimate shared network, with the potential for hundreds of parties along the way to look at, steal, redirect, or change data. However, it also has the lowest cost as high-speed Internet connections (where all legs are T-1, T-3, or faster lines) between offices are just a fraction of the price of a dedicated line. Table 11 compares the cost per month of using a direct line vs. a VPN from Los Angeles to New York at various transmission speeds.
TABLE 11: Estimated prices of dedicated communication line vs. virtual private network from Los Angeles to New York
| Connection type | Transmission speed (MBPS)* | Ded. line L.A. to N.Y. cost/mo. | VPN cost per month | Savings per month |
|---|---|---|---|---|
| Dial-up | 0.3 | $300 | $50 | $250 |
| T1 line | 1.5 | $8,500 | $2,500 | $6,000 |
| T3 line | 45.0 | $65,000 | $30,000 | $35,000 |
Source: VPNet, First Analysis.
Notes: *Megabits per second
A VPN uses network security technology and shared communication lines (i.e., the Internet) to imitate a dedicated line. With strong and fast encryption at both ends, good authentication, and strong access control, the Internet can become almost as secure as a company’s own private network, hence the name virtual private network. Table 12 illustrates the difference between a typical VPN and a dedicated line.
TABLE 12: A dedicated communication line vs. a virtual private network
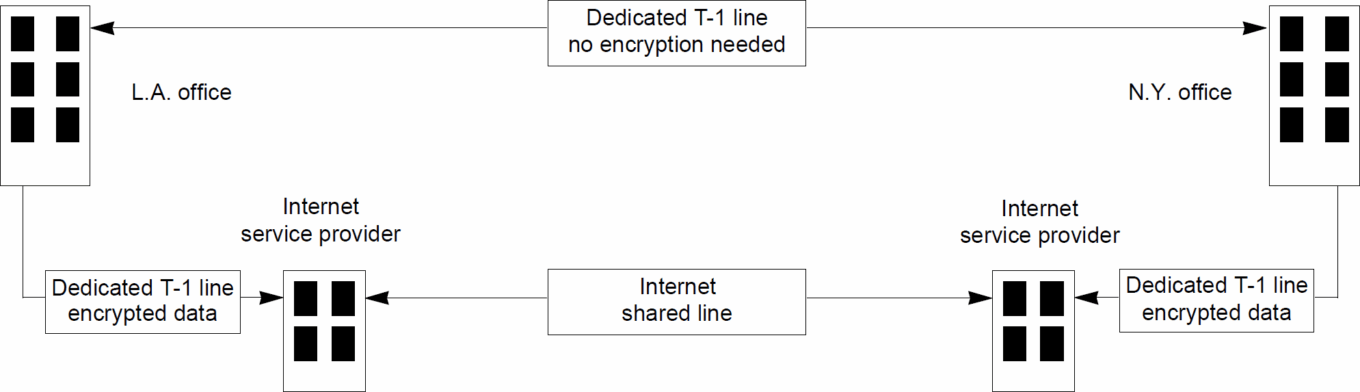
Source: First Analysis.
Secure transactions: Electronic commerce
A second security application, still in the development stages, is the secure electronic transaction. Not every investor will be interested in the details of a secure electronic transaction; however, it illustrates one application of network security technology and how demand may increase as the potential for the technology becomes more widely known. The development of widespread electronic commerce depends on generally held confidence in several key areas:
- secrecy (confidence that no unintended parties have accessed transmitted data)
- certainty of origination (confidence that a document is from the indicated party)
- integrity (confidence that a message hasn’t been altered by another party and that the sender wouldn’t be able to deny ownership). Through combinations of the technologies described above, confidence in all these areas can be achieved.
Encryption addresses the secrecy issue. The certainty of origination issue is addressed by digital IDs. Integrity (unaltered documents and non-repudiation) is addressed by digital signatures.
Digital IDs
Digital IDs are public keys registered by certifying authorities such as Verisign Inc. or the United States Postal Service. A certifying authority registers a public key to a specific person or entity. For example, Sam could create a public key and then take his passport or other proof of identification to a certificate authority. The authority would verify that the specific key belongs to Sam and not to someone claiming to be Sam. In the future, anyone wanting to verify that a key is really Sam’s could check with this certificate authority.
Digital signatures
Digital signatures are different from digital IDs. With a digital signature Sam (the sender) uses his private key and a publicly available algorithm called a hash function. The hash function applies a specific value, called a hash value, to the data he is sending. For example, a hash function may assign a certain numeric value to each character in the message (e.g., A=1, B=2, C=3, etc.). This specific hash function yields a unique hash value (e.g., 2001). Sam then encrypts this value with his private key, thus applying his digital signature. Finally, he encrypts his message and the encrypted hash value using Rachel’s (the receiver’s) public key as he usually would.
When Rachel receives the transmission, she decrypts it with her private key. She then uses Sam’s public key, which she verified with the certifying authority, to decrypt the hash value Sam attached to his message. Finally, she applies the hash function to Sam’s original message. If the hash function yields the same value as the one Sam attached, Rachel knows the message 1) came from Sam (because only his private key would create this value) and 2) hasn’t been altered (because any alteration would change the hash value). Note the use of keys for signatures is the opposite of general encryption where Sam (the sender) would use Rachel’s (the receiver’s) public key to encrypt and Rachel would use her private key to decrypt. (See Table 13.)
TABLE 13: A secure transaction
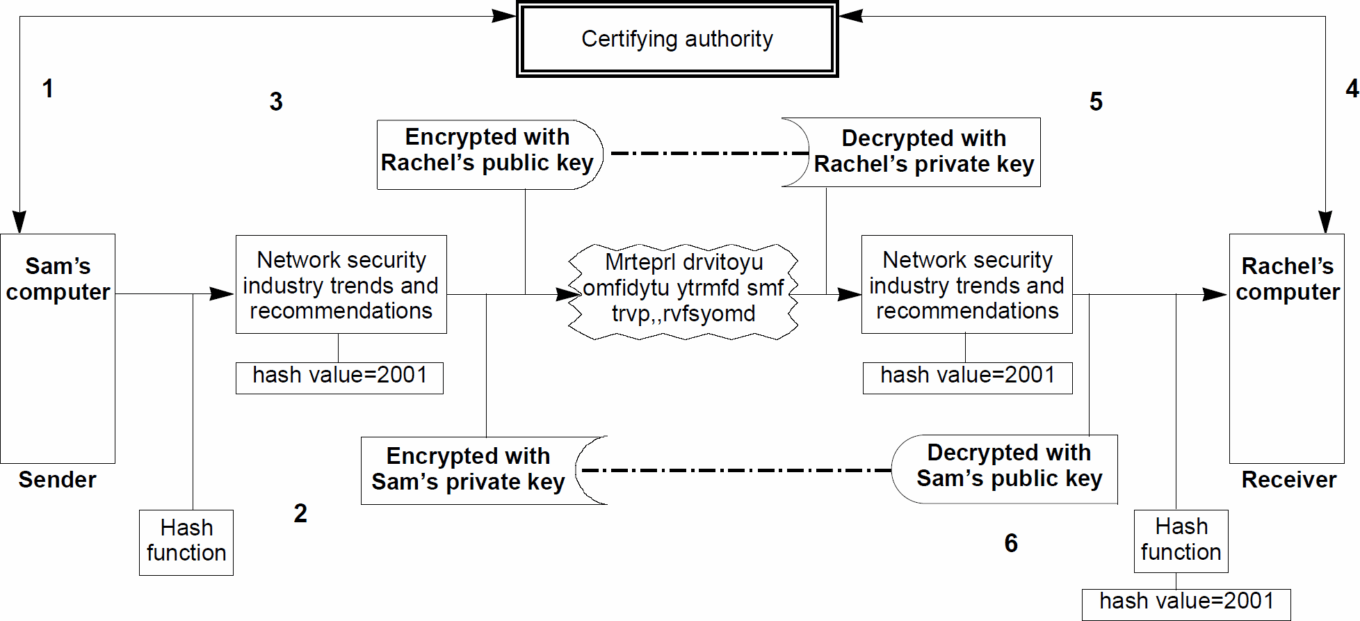
- Sam checks with Rachel’s certifying authority to make sure Rachel’s public key belongs to her.
- Sam applies the hash function and digital signature by encrypting with his private key.
- Sam then sends the message and encrypted hash value using Rachel’s public key.
- Upon receiving the message, Rachel verifies with the certifying authority that Sam’s key belongs to him.
- Rachel then decrypts the message using her private key.
- Finally, she decrypts the attached hash value using Sam’s public key and applies the hash function. If the two hash values match,
she knows the message came from Sam and that it is unaltered.
Though this seems like a time-consuming process, all the steps, with the possible exception of verification of identity with the certifying authority (if the authority is unknown), can be done automatically in microseconds.
Source: First Analysis.
Electronic commerce concerns
While we believe security is necessary for electronic commerce to take place, we believe the general public has a heightened awareness of Internet security issues, which is causing it to receive more attention than other security threats. For example, people who don’t think twice about reading a credit card number via a cellular phone (or via an even less secure cordless phone) are paranoid about sending credit card numbers via the Internet. Brokerage firms that do nothing to confirm the identity of a person placing an order via the telephone are requiring elaborate authentication to trade via the Internet.
Analogies can be found in commerce in the physical world. Banks take extreme measures protecting cash, storing cash in vaults and moving it in armored vehicles. However, every individual using cash doesn’t need an armored vehicle. The same is true for data security. Banks moving vast sums of money via the Internet should have the highest level of security. However, not every transaction needs the same level of security. We are seeing a focus on security of electronic commerce on the Internet unrelated to the real economic risk of loss. This heightened sensitivity to security should spur excess sales of high-end security equipment in the short term that will moderate over a number of years. We have tried to remove these excesses from our estimates of long-term market size.
Summary
Due to the growth of the Internet, organizations around the world have begun to focus on ways to secure their data networks. While no one solution is appropriate for every organization, there are several basic security threats, each of which must be addressed in some way to achieve optimal security.
As network security technology develops, solutions to meet security threats will likely evolve and overlap. The network security providers most likely to succeed are those who 1) are best able to meet and anticipate rapidly changing needs, 2) incorporate additional technology or form necessary strategic relationships, and perhaps most importantly, 3) effectively market their solutions to a diverse and changing set of customers.
Company profiles
Axent Technologies
Company background
Axent began as a software security division of a software predecessor company and has been focused on network security products. Axent was incorporated as a new entity in 1995. As part of Axent’s legal creation, the Open VMS (operating system) business was spun off to shareholders as a company called Raxco.
Axent’s current business activities began in late 1994; however, the management team worked together for several years in the predecessor company. It was their decision to create a company focused on network security. To accelerate the company’s research and development efforts in this area, Axent purchased Datamedia in December 1994. Datamedia had a PC security product and, importantly, in-process research and development that Axent incorporated into its ERM product.
Axent’s network security business
We believe Axent takes a fundamentally different approach to network security issues than most other network security companies. Axent’s main product, Omniguard Enterprise Security Manager (ESM), doesn’t solve security issues directly. Rather, it allows a customer to set up network security policies, audit its network, and monitor changes over time to see if the stated security policies are in place. The authentication, encryption, authorization, or other segment-specific solutions needed to implement the policy aren’t part of the ESM product. Axent does provide a growing number of point solutions, but more often than not, a customer will purchase segment-specific solutions from another company.
Despite the potential for customers buying other vendors’ security products to implement ESM-designed security policies, we believe Axent is building long-term value through an approach we term “owning the customer.” By being involved with a customer’s overall security strategy, Axent is in an ideal position to sell products to this customer over many years. Even if the security market changes emphasis (e.g., from firewalls to encryption), Axent can retain its position with the customer. Axent can also leverage its policy position by providing the solutions it sees its customers demanding. Axent has already introduced a number of solutions under the Omniguard name. The acquisition of AssureNet, which provides software-based authentication, is an example of how Axent can expand its product offering in areas where it sees its customers showing strong demand.
As part of its overall value proposition to customers, Axent sells its expertise and its ability to anticipate the long-term needs of its customers. Thus, Axent gives customer service greater prominence than most security product companies. As a result of Axent’s conscious strategy to have a consultative, high-level relationship with its customers, Axent limits its ability to expand its overall business to the same rate it expands its service and support organization. Therefore, Axent may not grow its revenue as fast as other companies in this industry. However, it should be able to gain greater visibility into its earnings from its close customer ties and the earnings should be more stable in a dynamic market. Axent also uses its knowledgeable staff as a source of material consulting revenue.
Products
ESM: Enterprise Security Manager
As mentioned above, Axent’s flagship product, ESM Omniguard, allows a customer to establish, evaluate, and centrally manage security policies. Once policies are set, ESM monitors the network and reports violations. For example, a simple policy may be that all passwords have eight characters of which at least three are letters. ESM continually monitors the passwords of everyone on the system and takes any corrective action the administrator has dictated for this violation. Because ESM typically monitors many parts of a network, software must reside on each piece of hardware. Table 14 illustrates a typical network configuration using Axent’s ESM Omniguard product.
TABLE 14: Typical network configuration using Axent’s ESM Omniguard product
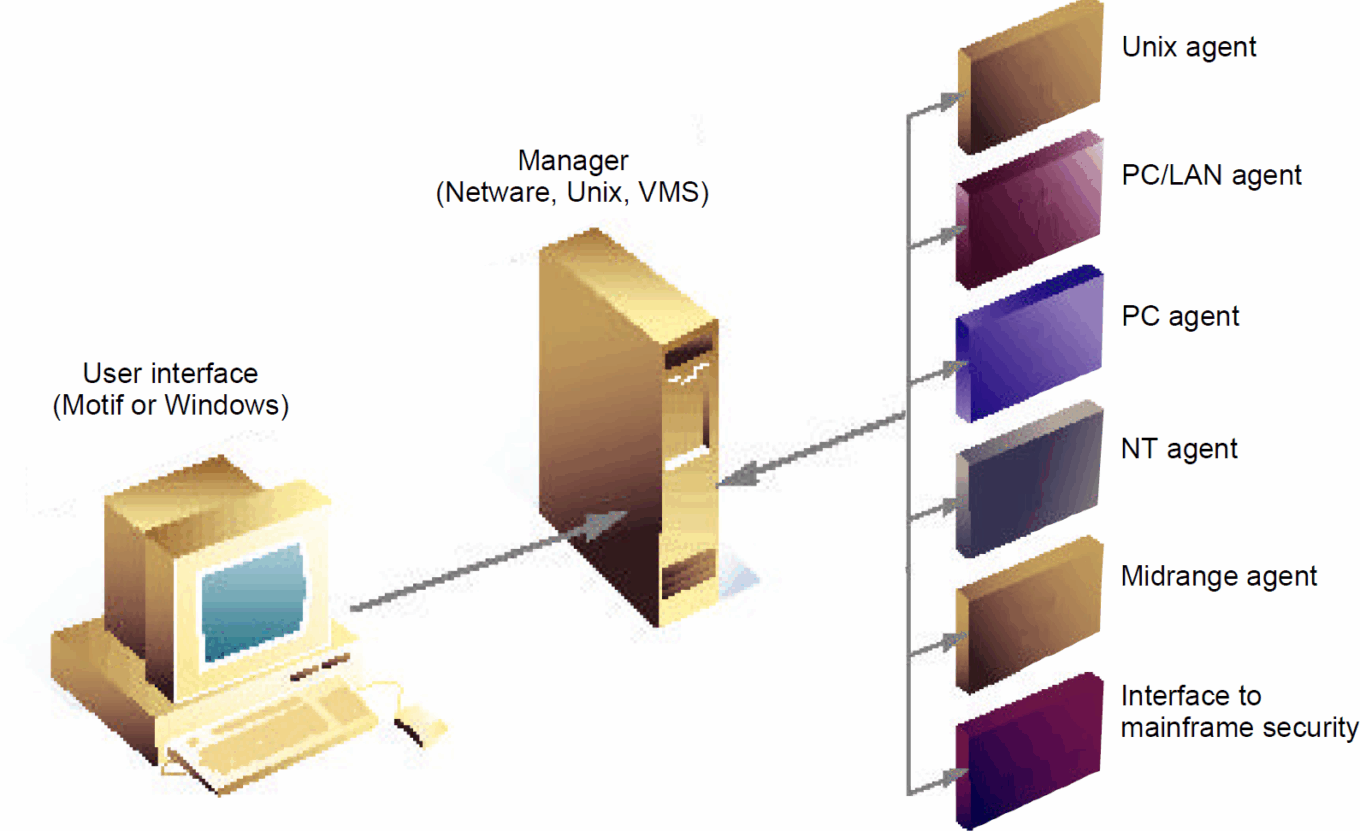
Source: Axent Technologies.
Importantly, ESM works with most major operating systems and thus works well in environments where several machines run different operating systems. For less common or proprietary operating systems, Axent provides an open application programming interface (API), which allows for integration. About 40% of Axent’s revenue is from ESM. ESM’s single-copy list price ranges from $395 to $3,995.
Other products
Other Axent products in the Omniguard suite include:
- Intruder Alert: Monitors a network for unauthorized access and takes actions, predetermined by the administrator, when an intrusion occurs.
- Enterprise Access Control for Unix (EAC/Unix) and PCs (EAC/PC): Allows managers to centrally control access to data on desktops or Unix platforms based on a variety of parameters such as time of day, file type, and user identification.
- ERM: A family of products designed to identify and authenticate network users and to administrate users’ computing resources. The products were generally released in the 1997 first quarter, and list prices range from $95 to $19,950.
- Services: Between 10% and 20% of Axent’s revenue comes from maintenance and support contracts.
Contract services
Axent has about 20 professionals available for consulting services and helping clients establish their security policies. However, these professionals can also help install the Omniguard product line. In quarters of strong demand for Axent’s Omniguard products, we believe consulting revenue will be lower. Axent believes installing its products to start the long-term relationships with clients is more valuable and a better use of scarce resources than a consulting project. On average, consulting is a little more than 10% of revenue.
Check Point Software Technologies
Company background
Check Point was incorporated in 1993, and unlike other network security product companies that began as government contractors, Check Point’s sole purpose from inception has been to market network security technology and applications. Check Point’s core technology comes out of experience the company founders had with the Israeli defense forces. Check Point had its initial public offering in June 1996.
Products
Firewall-1
Check Point generally sells its products under the Firewall-1 name. Check Point’s first version of Firewall-1 relied on packet filtering, and through its excellent distribution with Sun MicroSystems Inc. (under the FireWall-First name), quickly became the world’s best-selling firewall. During the past two years, packet filtering became synonymous with lower-level security firewalls. Check Point maintains, and we have every reason to believe, it implemented its packet filtering technique in a way that made it more secure than most packet filters. However, we believe the connection between packet filtering and Check Point, driven home by Check Point’s application-level firewall competitors, hurt Check Point’s image in the market for a period of time. (See pages 9 to 11 for a discussion of different types of firewalls.)
Check Point’s current version of Firewall-1 is based on its own patented stateful inspection technology. As a result, the packet filter association is no longer an issue. The company introduced an NT-based version of Firewall-1 in the September (third) quarter. Sales of Check Point’s NT-based product are increasing quickly, and we expect it to account for the majority 1997 first-quarter and future-quarter sales. Check Point’s fourth-quarter average firewall selling price was $9,600, up from $9,100 in the third quarter. This increase reflects a trend toward larger, enterprise-wide solutions rather than smaller, group-level solutions.
Open platform standard
In November 1996, Check Point announced its Open Platform for Secure Enterprise Connectivity (OPSEC), which lays the foundations for Check Point’s product direction in the future. OPSEC uses a combination of published application programming interfaces (APIs), support for industry-standard protocols, and a high-level scripting language (INSPECT, Check Point’s programming language for OPSEC) to create a relatively open security platform. Check Point hopes to capitalize on its market leadership position and cause third parties to design products that meet its OPSEC standard. If the strategy is successful, customers will be able to integrate security applications from multiple vendors and manage network security products (such as access control, authentication, administration, encryption, and content security) on a Check Point-based platform. Furthermore, by scripting in INSPECT, customers can customize the OPSEC platform to integrate with custom and in-house applications.
This approach is different from most of Check Point’s competitors. Other network security product companies have integrated with partner company products to create solutions that span the network security market; however, they have stopped short of publishing an API that allows anyone to integrate products without the company’s control. Competitors have therefore reserved the right to expand into other market segments (e.g., authentication, anti-virus, encryption, etc.), without being concerned that customers may already have integrated competitive products.
In addition to the basic firewall products, Check Point sells a variety of management and administration software products designed to enhance the usefulness of FireWall-1. Table 15 outlines Check Point’s complete FireWall product line.
TABLE 15: Check Point’s firewall product line
| Item | Product description | List price |
|---|---|---|
| Enterprise | ||
| FireWall-1 Enterprise | Enterprise, internet and intranet gateway(s) with distributed management capabilities | $18,900 |
| Firewall-1 Network Security Center | FireWall-1 Enterprise with added router management capabilties | $39,900 |
| Firewall-1 Inspection Module | Additional inspection modules for multiple gateway implementation | $6,000 to $11,000 |
| Internet gateway | ||
| FireWall-1 Internet Gateway | Internet and intranet gateway(s) with full-featured network security for small- to medium-sized businesses | $4,900 to $9,900 |
| Entry level | ||
| FireWall-First! | Basic internet and intranet access control with an easy-to-use World Wide Web interface | OEM only |
Source: Check Point Software Technologies.
Raptor Systems Inc.
Company background
Founded in 1991, Raptor spent several years developing its network security products. In late 1994, Raptor received venture funding, and it recorded its first material revenue in 1995. Raptor is a new company relative to most of its competitors, many of which have years of experience working with government agencies. This is an important distinction. Unlike many of its competitors, Raptor has designed its products and organization with commercial sales in mind from inception.
Products
Raptor is branching out into several parts of the security market; however, Raptor continues to build from its core product, its Eagle application-level firewall. Raptor has a number of related products sold under the Eagle name, each of which addresses various security concerns. Raptor refers to these concerns as domains. Table 16 shows Raptor’s vision of a network and how its products fit into this network as well as a description of some of its leading products. Raptor defines this vision as integrated enterprise network security.
TABLE 16: Raptor’s domain 5 – integrated enterprise network security
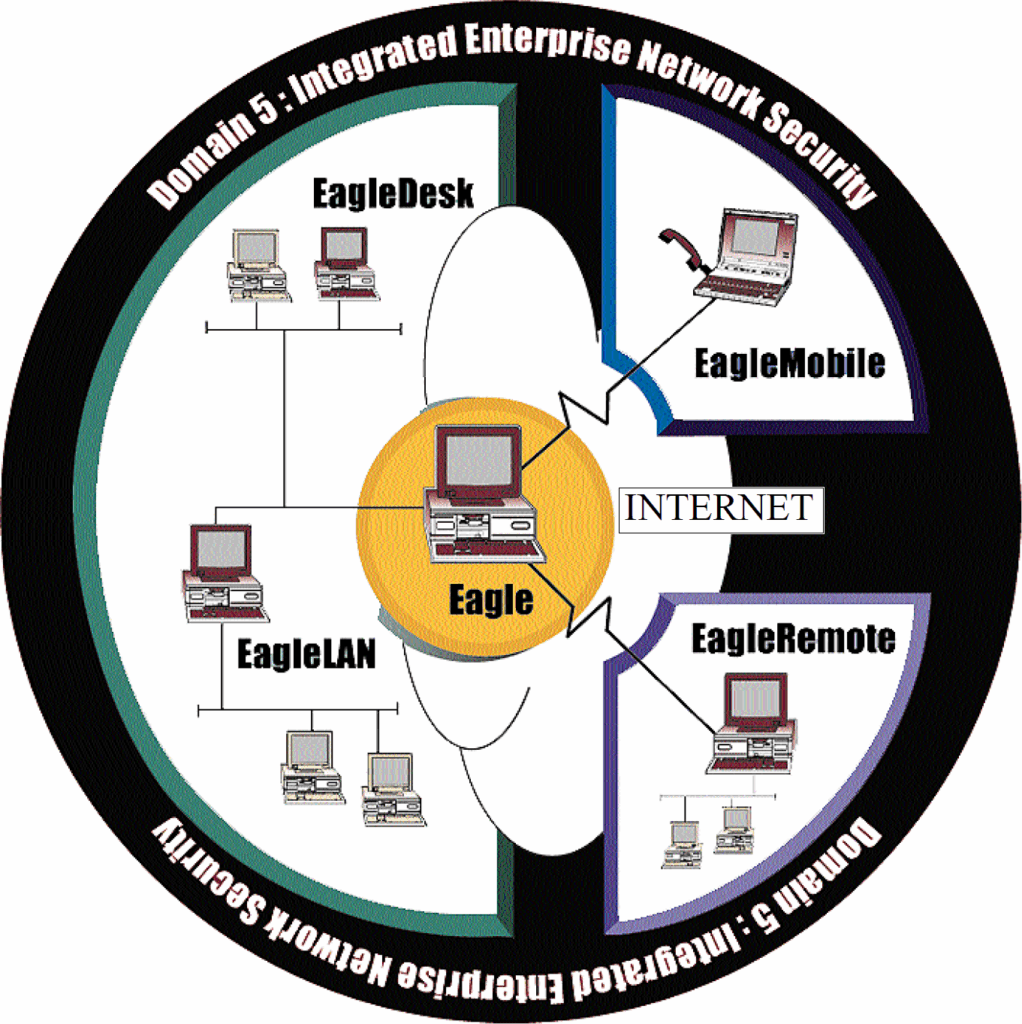
Source: Raptor Systems.
Raptor only sells software, allowing its customers or distributors to choose the hardware and platform. All Raptor’s products are designed with an open architecture that conforms to industry standards. Raptor integrates with many of the leading token authentication companies, and its products run on almost any standard hardware. The company takes pride in having many firsts with its products. These claims include:
- first NT-based firewall
- first application-level, plug-and-play firewall for small businesses (The Wall)
- first firewall with real-time suspicious activity monitoring
- first firewall with remote management and administration for firewalls at other locations.
From this list, we note that Raptor is continually on the leading edge of technology and works diligently to keep its products current with whatever computer platform or operating system is popular in the market, thus giving its customers confidence that Raptor will be able to service their security needs in the future.
Revenue breakdown
Eagle products
About 90% of Raptor’s revenue is from the Eagle firewall product. Raptor was the first to introduce a high-end NT fire-wall, shipping this product in meaningful volumes in the 1996 March (first) quarter. The NT-based version quickly accounted for the majority of revenue and constituted 74% of Raptor’s firewall units shipped in the 1996 fourth quarter. The NT-based products have lower average sales prices than the Unix-based products, due primarily to configuration differences, and represented 65% of fourth-quarter revenue. The remaining 35% of revenue is from Unix-based products. Raptor supports a wide variety of Unix-based products from Sun Microsystems Inc., Hewlett Packard Co., and Siemens-Nixdorf. (Raptor is the only firewall supporting Siemens-Nixdorf’s Unix-based servers.) Though we expect NT-based products to account for the vast majority of revenue going forward, we believe many customers and potential customers are committed to Unix and that the Unix-based line will remain important for several years. The price to end users is between $6,500 and $25,000 per firewall.
EagleDesk and EagleMobile
EagleDesk and EagleMobile carry a suggested selling price of $99 per copy and reside on the PC. The products include password protection, strong authentication, and communication encryption. The products are designed to create a virtual private network between client users and the server or other users. (See pages 12 and 13 for a description of a virtual private network.) These are new products, and Raptor sold 3,400 copies of them in the fourth quarter. We expect quick market acceptance and substantially higher volumes in 1997.
Other products
Raptor sells several other products aimed at the various domains with a variety of prices. With all of its products, Raptor focuses on enhancing administrative and monitoring capabilities. Hawk, EagleConnect, and EagleNetwatch are Raptor products specifically designed to address these needs. We believe Raptor is one of the leading firewall vendors when it comes to understanding the tremendous market demand for administrative and monitoring tools. Raptor makes considerable effort to integrate end-user needs with its products.
In the 1997 first quarter, Raptor introduced a new firewall product line called The Wall, which is designed to bring high- end access control to small- and medium-sized businesses. Pricing begins at less than $1,000 for 25 users. Raptor designed the product’s administrative features to be simple and meet the administrative needs of a small business computer network. It is too early to estimate sales from this product.
Security Dynamics Technologies Inc.
Company background
Security Dynamics has a long history in the authentication space; the company began shipping its patented time-based (synchronous) token system more than 10 years ago. For a company selling network security products commercially, Security Dynamics is a veteran. Fortunately for the company, the growth of remote access to networks (in the early and mid-1990s) and the explosion of the Internet (beginning in 1995) prompted intense interest in its authentication technology and has continued to propel its value.
By being present before the extremely strong market growth of the last few years, Security Dynamics was able to capture a leading position, which it has held.
In mid-1996, using its stock as currency, Security Dynamics acquired the market leader for encryption, RSA. The two companies have remained largely separate, and RSA has maintained its own brand identity, as the customer bases and distribution strategies of the two companies are quite different. However, Security Dynamics is starting to more tightly integrate RSA’s encryption into its products. We look at the product and market dynamics of each division separately.
Products
Patented authorization technology
The core of Security Dynamics’ authorization business is its time-based tokens. Until recently, these tokens have been hardware. In 1996, Security Dynamics introduced software- only versions of this product based on the same authorization technique. (See Table 17.)
TABLE 17: Security Dynamics’ SecurID authentication token
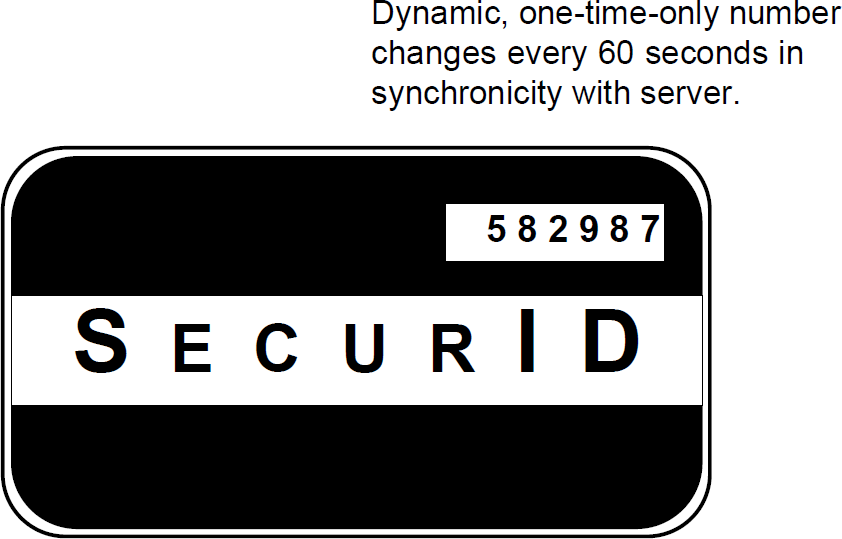
Source: First Analysis.
Security Dynamics’ methodology is fairly simple: Patented technology based on something one knows (a password) and something one has (the token). See pages 8 and 9 for details of authentication techniques.
The customer buys tokens and issues a specific token (identified by serial number) to an individual. Each token displays a code (the customer can specify the number of digits) that changes every minute and is determined by a unique permutation. At the same time, Security Dynamics’ server software tracks each issued token and is synchronized to know what code each token displays each minute. When the user wants to access the network, he or she enters a password (identifying the person issued the token) and then enters the code on the token. Only someone knowing both the password for this user and the code on the token at that minute can access the network. See Table 7 for an illustration of this procedure.
The appeal of this type of authentication vs. other token technology is its speed and simplicity. Most other tokens are challenge-response requiring the user to enter a challenge into the token device and then submit the outcome back to the network. This process is necessarily more cumbersome than Security Dynamics’ direct-entry approach. See Table 8 for an illustration of this procedure.
Additional security option
For added security, Security Dynamics offers a version of its token that has a numeric keypad. Rather than displaying an access code at all times, these tokens display the code only when the user enters a unique pass code into the keypad. The advantage of this system is that a user ID is never transmitted via the network, which in many cases is not secure.
Token lifetime
From an investment perspective, some other attributes of Security Dynamics’ tokens are advantageous. The tokens have a limited life, either programmed or due to battery life. Security Dynamics doesn’t allow users to replace batteries or reprogram expired cards. Thus, the tokens have a replacement revenue stream that is both recurring and predictable. The renewal rate has been about 80% historically.
This attribute, though attractive to investors, is a selling point for competitors that claim a lower lifetime cost by allowing customers to program the tokens and replace batteries. Prices for tokens average around $60, and they account for about 60% of Security Dynamics’ non-RSA revenue.
Other revenue
The remainder of Security Dynamics’ non-RSA revenue comes from server products used to control and administer its authentication tokens. These include the ACE/Server and ACM software and hardware. These are secure systems that can run on a variety of operating systems. The ACE/Server is a stand-alone system that includes both client and server software to allow an administrator to control access to resources on a TCP/IP network (e.g., the Internet). The ACM products integrate directly with the host computer operating systems to provide authentication as well as reporting and audit capabilities. SecurADM software introduced in 1995 offers single-sign-on capabilities for environments with a variety of computing platforms and operating systems.
Vasco Corp.
Company background
Vasco is a little-known manufacturer of data encryption software, authentication tokens, and other network security products. However, it is one of the largest suppliers of data security authentication and encryption products in Europe. Vasco has a relatively modest but growing presence in the United States. Its European focus is due to 1) the company’s acquisition strategy and 2) a strong distributor relationship in Europe.
Consulting company
Vasco was originally a consulting and computer training company that acquired the remnants of a corporation called ThumbScan in 1989. ThumbScan had two important pieces of technology. One was the Gordian Access Key, a challenge-response token system for computer user authentication and access control. (See pages 8 and 9 for a discussion of challenge-response technology.) Vasco has enhanced the challenge-response token into a robust technology for user authentication that is beginning to gain market recognition, mostly in the financial community. Today it is being used by ABN-Amro Bank in the Netherlands and more than 110 other large financial institutions to allow customers direct access to their accounts via the Internet. The second technology is a patent portfolio of biometric technologies, mostly related to fingerprint verification, which it has yet to bring to market. These biometric patents may have significant value as biometrics gain acceptance, a phenomenon we expect in the next two to five years.
Lintel acquisition
Vasco completed a second highly strategic acquisition, Belgium-based Lintel Security, in June 1996. Lintel has expertise in encryption and markets data encryption chips. It offers 1) dedicated chips to enhance the processing of encrypted documents (using both the RSA and DES algorithms), and 2) complete board-level encryption solutions. It has an important distribution network in Europe. Lintel’s data-encryption technology is being built into a number of devices, including cellular phones, fax machines, call routers, servers, and modems. Because Lintel is a Europe-based company, it isn’t subject to U.S. export controls on encryption products, giving it an important competitive advantage over U.S.-based suppliers of similar products.
Digipass acquisition
Vasco’s most recent acquisition, in July 1996, was Belgium-based Digipass, a manufacturer of low-end challenge-response tokens and formerly a major competitor to Vasco in Europe. The Digipass token operates in a response- only mode and can apply a digital signature. The Digipass product accounts for the majority of Vasco’s token installed base.
Products
In 1996, 93% of Vasco’s pro forma revenue was from the sale of tokens. Vasco sells a family of tokens with most of the revenue derived from the Digipass and Access Key II products.
- Digipass is a lower-end, response-only token. List price is $57 for a single unit, and it has an average selling price between $35 and $45. These tokens issue a dynamic, one¬time password based on time synchronicity (similar to Security Dynamics tokens discussed earlier).
- Authenticard is a challenge-response token acquired in the Lintel acquisition and is Vasco’s mid-priced token solution.
- Access Key II is a challenge-response token that employs an optical bar-code-type reader to authenticate users. The computer screen generates a challenge that appears as a configuration resembling a bar code. By holding the token in front of the screen, the response is generated and authentication is achieved. The Access Key lists for $89 and has an average selling price around $60.
- Access Key II is a challenge-response token that employs an optical bar-code-type reader to authenticate users.
Server-level products: Shiva partnership
In January 1997, Vasco announced a relationship with Shiva Corp., with substantial ramifications for marketing (discussed below). From a product standpoint, Vasco licensed some software that allows it to offer a turnkey solution called VACMan. Prior to this announcement, Vasco offered its comprehensive family of token devices, but not the server software to administer these devices. In Europe, most companies preferred to develop their own server software, so the absence of a turnkey solution wasn’t a material drawback. However, in the United States, most companies want to buy client tokens and a network server solution together in a turnkey format. This is how Security Dynamics and other competitors market their products.
VACMan is an authentication server that also performs authorization, and it is Vasco’s first server-level product offering. VACMan supports both Radius and Tacacs+ protocols, allowing interoperability with most leading remote-access servers. Licenses run $5,000 per server for up to 500 users, a price materially lower than most competing products on the market. Vasco and Shiva have developed and are continuing to develop features for the VACMan product. These include:
- VACMan/accountant ($750 for 500 users) works with open database connectivity (ODBC) and handles logging and other administrative and auditing functions
- VACMan/LDAP (Lightweight Directory Assistance Protocol) ($500, unlimited use) adopts the industry standard LDAP method for searching for user information and authenticating users
- VACMan/client NT ($500) converts any NT workstation into a Radius client, allowing VACMan to authenticate any NT client on the network
- VACMan/personal NT allows the same authentication for any NT client as VACMan/client NT, but runs client software, which permits authentication on portable computers even when not connected to the LAN. This product is expected to be available in the 1997 second quarter for $59 per client.
We expect further VACMan-enhancing products later this year. We note that VACMan and its related enhancements are designed to expand the functionality and use of Vasco’s token products. The vast majority of revenue and profit should still be derived from tokens for the foreseeable future.
Glossary
Access control: Limits access to part or all of a computer network by identifying a user or type of communication; often works in concert with authentication. The most common applications of access control are firewalls.
Application-specific integrated circuit (ASIC): A computer circuit designed to perform specific, limited functions very efficiently; often used to increase data processing speed.
Authentication: Verifying that a user is who he or she claims to be. Types of authentication include passwords, tokens, and biometrics. Authentication often works in concert with access control.
Authentication token: A device that verifies a user’s identity when accessing a computer network. Two main types are: synchronous tokens (time-linked to the computer network) and challenge-response tokens (using multiple codes to verify identity).
Biometric: Analyzes some unique physical attribute to identify a user. Types of biometric authentication devices include fingerprint readers, retinal scans, and voice verification.
Certifying authority: A company or organization that registers a public encryption key to a specific person or entity. Message recipients can verify the identity of the sender through the certifying authority that registered the key.
Data encryption standard (DES): A U.S. government encryption standard using a single (secret) key; probably the most widely used encryption method.
Dedicated line: A communication line used by a single entity, usually on a leased basis.
Digital ID: A verifiable public-private key pair registered by a certifying authority.
Digital signature: Using digital technology to verify a transmission is from a specific sender (individual or entity). Digital signature is usually accomplished by using a verifiable private key to encrypt a message.
Encryption: Applying a code (usually a mathematical algorithm) to a message making it unreadable until a decoding algorithm (decryption) is applied.
Firewall: A system that controls the flow of data between an internal network and the Internet or between segments of an internal network. Types of firewalls include packet filter firewalls (which check a data packet’s origin and destination only) and application-level firewalls (which check packet application usage as well).
Hash function: The attachment of a specific value (based on a specific code) to a message; the value can verify that a message wasn’t altered during transmission.
Intranet: A private computer network that uses Internet data formats and protocols.
Internet: An open, global network of interconnected computer networks that use common communications protocols.
Operating system: A master control program for a computer that manages the computer’s internal functions.
Public key: An encryption key registered to a particular person and available to the public; data encrypted with the key can only be decrypted with the matching private key.
Secret key: A unique encryption key used to encrypt and decrypt data; not available to the public.
T-1 line: A high-speed communication line capable of transmitting data at 1.54 megabits per second.
T-3 line: A very high-speed communication line capable of transmitting data at 45 megabits per second.
Shared line: A communication line to which more than one user has access and which is therefore more open to data interception.
Spoofing: Making a data transmission from one IP address appear to originate from some other IP address.
Virtual private network: Using encryption, authentication, and other security measures on both ends of a shared line to approximate the security of a dedicated line.
Virus: A computer code embedded in a program that causes the computer to perform an unexpected function.
World Wide Web: A network of computer servers that uses a special communications protocol to link different servers across the Internet; permits transmission of graphics, data, and sound.
